Hong Kong‑Based Scanners Flood GreyNoise, Signal Recon Before Real Attacks
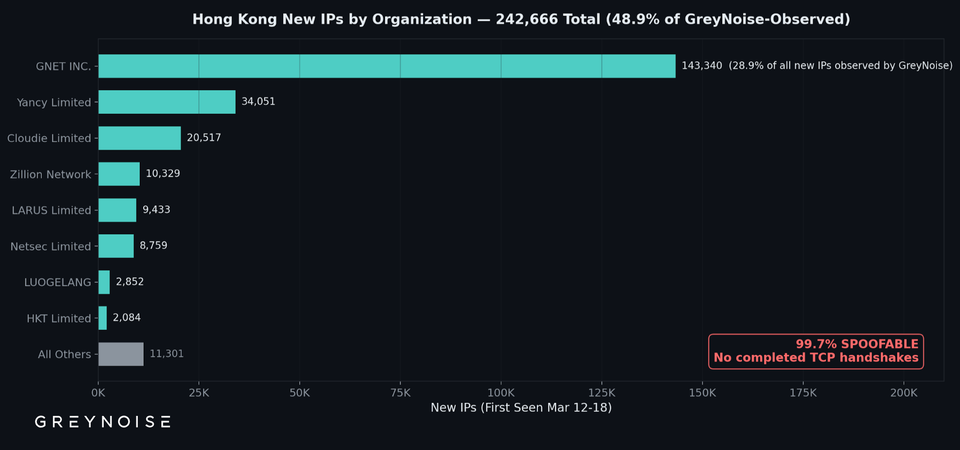
GreyNoise observed a sudden surge of scanning activity, with roughly 50% of the new source IPs geolocated to Hong Kong. Most of these probes failed to complete a TCP handshake, indicating they were limited to banner grabs and port sweeps rather than attempts to exploit services.
The pattern suggests a pre‑attack reconnaissance phase: threat actors are mapping exposed assets, profiling services, and building target lists before launching more sophisticated intrusions. Defenders should treat this noise as an early warning sign, adjust monitoring thresholds, and consider leveraging GreyNoise’s configurable blocklists to filter out low‑signal traffic, reducing alert fatigue and preserving bandwidth for genuine threats.
Categories: Threat Intelligence, SOC & Automation
Source: Read original article




Member discussion