Hong Kong‑Based Scan Surge Signals Coordinated Reconnaissance Campaign
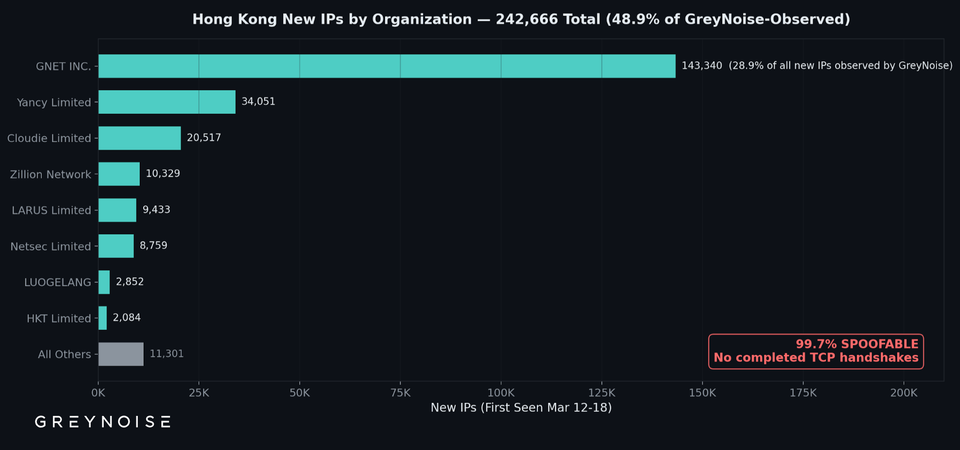
GreyNoise reported a sudden rise in previously unseen scanning IPs, with roughly 50 % of the traffic geolocated to Hong Kong. Unlike typical opportunistic scans, the attempts showed a uniformly low connection success rate and followed a repeatable pattern, suggesting a deliberate, systematic probing effort rather than random background noise.
The activity is a classic “low‑and‑slow” reconnaissance step that often precedes more focused intrusion attempts. Defenders should treat the surge as an early warning sign, tighten network monitoring, enrich threat intel with the identified IP ranges, and adjust firewall or IDS rules to limit exposure while investigating any follow‑up behavior. Ignoring such coordinated scans can leave organizations vulnerable to foothold‑building and subsequent payload delivery.
Categories: Threat Intelligence, SOC & Automation
Source: Read original article




Member discussion