Hidden Risks: Proprietary Apps Create Security Blind Spots

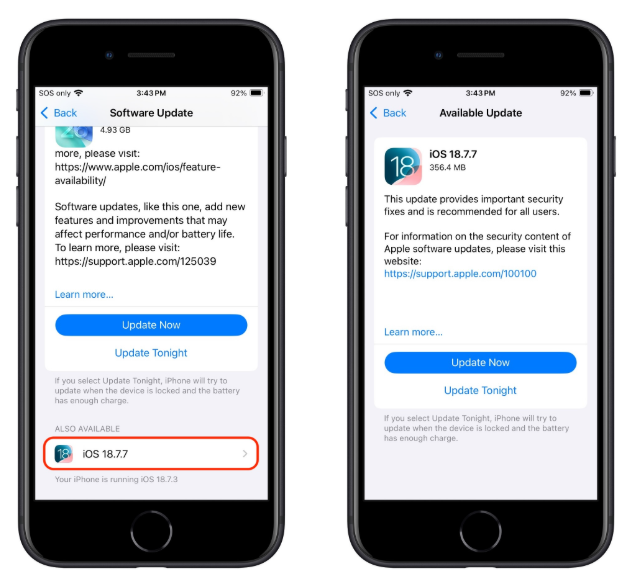
A recent Security.StackExchange discussion highlighted how organizations that depend on proprietary software often operate without full visibility into the code base. Because the source is closed, internal security teams cannot perform thorough code reviews, and they must rely on the vendor’s own testing and disclosure practices. When a vulnerability is discovered, the vendor may prioritize other products, delay a fix, or release a patch without detailed information about the root cause, leaving defenders in the dark.
The result is a widening attack surface: undisclosed flaws linger longer, patch cycles become unpredictable, and defenders must scramble to apply work‑arounds or mitigate exposure without knowing the full scope. For security teams, this means increased risk of exploitation, compliance challenges, and higher operational overhead. Prioritizing inventory of proprietary components, demanding transparent vulnerability timelines, and building contingency plans are essential steps to prevent hidden maintenance gaps from becoming entry points for attackers.
Categories: Security Culture & Human Factors, Vulnerabilities & Exploits
Source: Read original article


Member discussion