Global espionage campaigns and AI‑driven threats shape February's cyber landscape 🌐; Cloud misuse and social platform safeguards add new twists 🔐
Good day, February 10 2026 – here’s your concise briefing on the most critical cyber and AI threat developments of the day.
Today's headlines
- Shadow Campaigns exploit over a dozen vulnerabilities across SAP, Microsoft, and D‑Link products.
- Amaranth‑Dragon leverages the newly disclosed CVE‑2025‑8088 for targeted espionage in Southeast Asia.
- Romania's national oil pipeline operator suffers a disruptive cyberattack.
- Unit 42 unveils a novel cloud‑logging technique to track threat‑actor activity.
- ScanBox keylogger distributed via watering‑hole attacks against Australian and offshore energy firms.
1️⃣ Shadow Campaigns: Global Espionage Unveiled
Key Points:
- Tracked exploitation of 20+ vulnerabilities across enterprise software.
- Observed privilege‑escalation techniques targeting SAP Solution Manager and Microsoft Exchange.
- Detected remote code execution attempts on D‑Link and Ruijieyi network devices.
Description:
Unit 42’s analysis of the Shadow Campaigns group reveals a systematic abuse of known and zero‑day vulnerabilities to infiltrate critical infrastructure worldwide. The threat actors combined credential‑theft, privilege escalation, and remote command execution to maintain persistence in targeted networks.
Why It Matters:
Understanding the breadth of exploited flaws helps defenders prioritize patching for high‑impact software and harden detection of lateral movement, reducing the risk of widespread espionage and sabotage.
2️⃣ Amaranth‑Dragon Exploits CVE‑2025‑8088 in SE Asia
Key Points:
- Weaponization of CVE‑2025‑8088 against government and telecom entities.
- Attribution to the APT‑41 affiliated Amaranth‑Dragon group.
- Use of custom malware loaders to evade conventional AV solutions.
Description:
Checkpoint researchers detail how Amaranth‑Dragon has incorporated the recently disclosed CVE‑2025‑8088 into its espionage toolkit, targeting organizations in Southeast Asia with a multi‑stage payload that leverages the vulnerability for remote code execution.
Why It Matters:
The rapid weaponization of a fresh CVE demonstrates the need for accelerated patch deployment and threat‑intel sharing to prevent exploitation before mitigation measures are widely adopted.
3️⃣ Romanian Oil Pipeline Operator Hit by Disruptive Attack

Key Points:
- Attack caused outage of Conpet’s public website and internal systems.
- Initial indicators point to a ransomware‑like intrusion vector.
- Incident highlighted gaps in incident‑response readiness.
Description:
The 9 February Threat Intelligence Report from Check Point notes that Romania’s national oil pipeline operator, Conpet, experienced a cyber intrusion that knocked its IT services offline, disrupting communications with stakeholders and damaging operational credibility.
Why It Matters:
Critical infrastructure operators must reassess their resilience strategies, ensuring segregation of OT and IT environments and bolstering backup and recovery capabilities against similar disruptive incursions.
4️⃣ Novel Cloud‑Logging Method Tracks Threat Actors
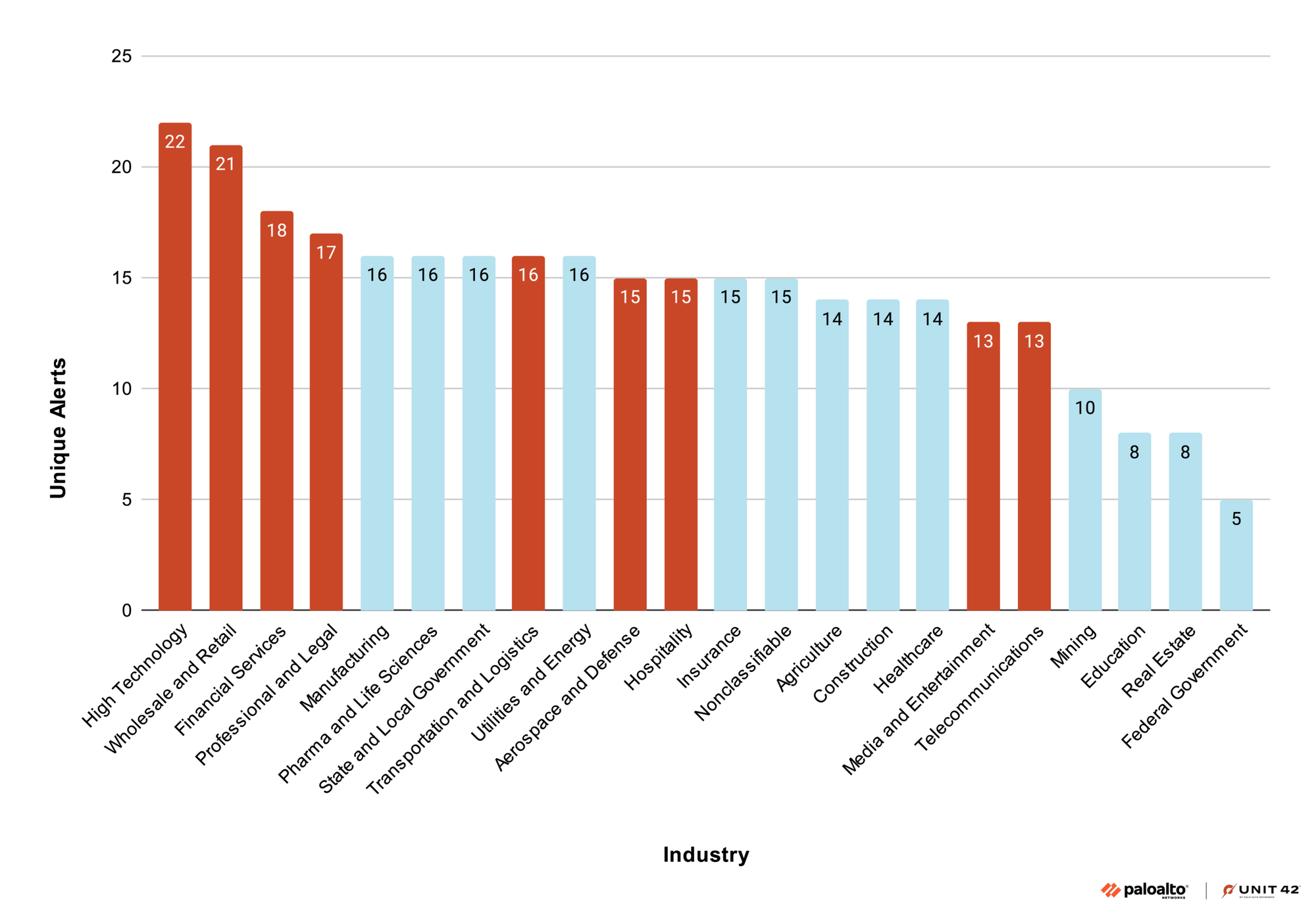
Key Points:
- Introduces a logging framework that correlates cloud‑API calls with attacker behavior.
- Demonstrates detection of Scattered Spider and other groups shifting to cloud services.
- Provides actionable alerts for suspicious role‑assumption events.
Description:
Unit 42 presents a new technique that leverages native cloud‑logging capabilities to monitor and attribute malicious activity within cloud environments, shedding light on the operational patterns of groups such as Scattered Spider and Halcyon Silk Typhoon.
Why It Matters:
As adversaries increasingly exploit cloud infrastructure, enhanced visibility through logging can early‑detect compromise attempts, limiting exposure and facilitating rapid containment.
5️⃣ CISA Catalogs Publicly Available Attack Tools
Key Points:
- Lists over 150 publicly released tools used in recent cyber incidents.
- Classifies tools by functionality: exploitation, credential dumping, and data exfiltration.
- Recommends mitigation steps for organizations encountering these utilities.
Description:
The Cybersecurity and Infrastructure Security Agency (CISA) releases an advisory documenting the proliferation of publicly accessible tools that have been incorporated into real‑world attacks, emphasizing their role in lowering the barrier to entry for threat actors.
Why It Matters:
Awareness of widely available malicious utilities enables defenders to adjust detection rules and educate stakeholders on the heightened risk posed by “tool‑based” adversaries.
6️⃣ Watering‑Hole Campaign Deploys ScanBox Keylogger
Key Points:
- APT TA423 uses compromised news sites to deliver ScanBox JavaScript keylogger.
- Targets include Australian media outlets and offshore energy firms in the South China Sea.
- ScanBox gathers keystrokes and system information before exfiltration.
Description:
ThreatPost reports a watering‑hole operation attributed to Chinese‑based APT TA423 that injects the ScanBox reconnaissance framework into popular news sites, silently harvesting credentials from visitors in the targeted sectors.
Why It Matters:
The campaign underscores the persistent threat of supply‑chain compromise via legitimate web properties, urging organizations to enforce content‑security policies and monitor anomalous outbound traffic.
7️⃣ Rise of the Digital Parasite Extends Ransomware Dwell Time

Key Points:
- Picus Red Report 2026 reveals attackers favor long‑term footholds over quick ransom.
- Techniques include stealthy credential harvesting and legitimate tool abuse.
- Detection gaps in endpoint monitoring allow persistent compromise.
Description:
The Hacker News highlights findings from Picus Security’s Red Report, indicating a shift from overt ransomware to ‘digital parasite’ tactics where adversaries maintain covert, long‑lasting presence within networks to exfiltrate data and manipulate systems.
Why It Matters:
Security teams must evolve from signature‑based alerts to behavior‑analytics and continuous monitoring to uncover hidden persistence mechanisms before critical data is compromised.
8️⃣ CrowdStrike Enhances Linux Web‑Shell Detection
Key Points:
- Falcon sensor now identifies anomalous PHP/Node.js web‑shell patterns on Linux.
- Integrates machine‑learning models to reduce false positives.
- Provides automated containment actions for detected shells.
Description:
CrowdStrike’s latest blog details improvements to its Falcon platform that focus on detecting and preventing advanced web‑shell deployments on Linux servers, leveraging AI to spot malicious script behavior in real time.
Why It Matters:
As attackers increasingly target Linux web infrastructure, enhanced detection capabilities help organizations block persistence mechanisms before attackers can leverage compromised servers for further exploitation.
9️⃣ CrowdStrike Recognized as Gartner Customers’ Choice 2025

Key Points:
- Earned top ranking for External Attack Surface Management (EASM).
- Customer surveys cite superior visibility and rapid remediation.
- Highlights integration of AI‑driven asset discovery.
Description:
CrowdStrike’s announcement celebrates its selection as the sole vendor to receive Gartner’s Customers’ Choice award for EASM in 2025, reflecting strong market confidence in its AI‑enabled asset management and exposure reduction solutions.
Why It Matters:
Adoption of advanced EASM tools like Falcon empowers organizations to proactively identify and secure shadow IT assets, a growing vector for breaches in hybrid cloud environments.
🔟 Discord Enforces Age‑Verification Mode for Teens
Key Points:
- Users under 18 will see restricted content until age is verified.
- Aim is to reduce exposure to malicious links and scams on the platform.
- Implementation includes optional phone verification for full access.
Description:
Malwarebytes reports that Discord will roll out a teen‑appropriate mode, limiting the visibility of potentially harmful content for unverified younger users, in an effort to curb social‑media‑borne cyber threats.
Why It Matters:
Platform‑level safeguards can substantially lower the attack surface presented by social networks, protecting vulnerable demographics from phishing, malware distribution, and targeted social engineering.
Stay vigilant and keep your defenses up.
Member discussion