🛡️ Global cyber‑attack trends & AI‑driven threats surge in 2025 🚀

Hello, here’s your Daily Cybersecurity & AI Threat Intelligence roundup for January 30 2026.
Today's headlines
- Check Point’s 2026 report reveals a 27% rise in ransomware attacks worldwide.
- CrowdStrike uncovers the split of Labyrinth Chollima into three distinct groups.
- Bitdefender tracks an Android RAT delivered via Hugging Face hosting.
- VMware publishes an AI‑powered framework to accelerate Zero Trust deployments.
- Unit42 warns of Russian cyber operations aiming at the 2026 Winter Olympics.
1️⃣ Check Point 2026 Cyber Security Report Highlights

Key Points:
- Global telemetry shows a 27% increase in ransomware incidents during 2025.
- AI‑generated phishing lures accounted for 18% of all malicious emails.
- Supply‑chain compromises rose by 12% across multiple sectors.
- Mobile malware activity peaked in Q4 2025, driven by credential‑stealing trojans.
Description:
The Check Point Cyber Security Report 2026 aggregates telemetry, vulnerability research, and active investigations to map attacker behavior in 2025. The report highlights a sharp uptick in ransomware, the growing use of AI for crafting phishing content, and expanding supply‑chain attack vectors across finance, healthcare, and manufacturing.
Why It Matters:
Understanding these trends helps CISOs prioritize defenses, allocate resources toward AI‑enabled threat detection, and reinforce supply‑chain security programs before the threats materialize in 2026.
2️⃣ CrowdStrike Labyrinth Chollima Splits into Three Adversaries

Key Points:
- The original Labyrinth Chollima group has fragmented into three independent actors.
- Each faction now targets distinct industries: finance, telecom, and critical infrastructure.
- New toolsets include file‑less payloads and credential‑stealing modules.
- Operational tempo increased, with weekly campaign launches observed.
Description:
CrowdStrike’s analysis shows the once‑unified Labyrinth Chollima adversary evolving into three separate groups, each with specialized tactics and target selections. The shift reflects a strategic refocus that enables faster development cycles and diversified attack infrastructure.
Why It Matters:
Enterprises must update detection rules to account for varied indicators of compromise and monitor for the emerging toolsets, as the fragmentation raises the probability of simultaneous multi‑sector attacks.
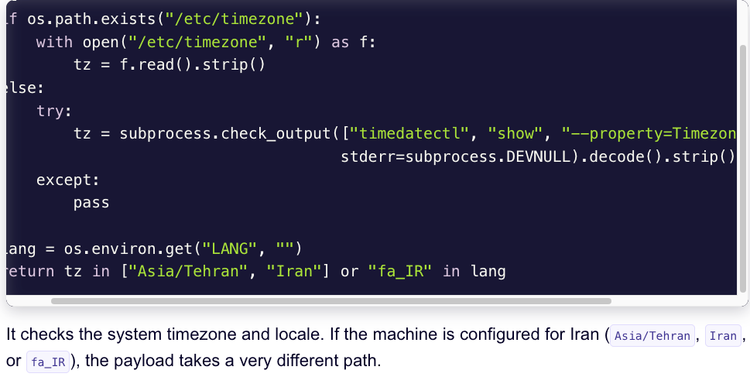
3️⃣ Bitdefender Android Trojan Uses Hugging Face for RAT Delivery

Key Points:
- Malware payloads were hosted on Hugging Face repositories to bypass traditional filters.
- Dropper hashes such as d184d705189e42b54c6243a55d6c9502 were identified in the campaign.
- Command‑and‑control servers include trustbastion.com and au‑club.top.
- The RAT targets Android devices, exfiltrating contacts, messages, and location data.
Description:
Bitdefender uncovered an Android trojan campaign that leverages the popular AI model hosting platform Hugging Face to distribute remote‑access trojan (RAT) payloads. By using legitimate cloud services, the attackers evade static detection and achieve rapid spread across compromised devices.
Why It Matters:
Mobile security teams need to expand threat‑intel feeds to include cloud‑based hosting services and implement behavioral analytics on app installations to detect such stealthy delivery mechanisms.
4️⃣ VMware AI‑Driven Zero Trust Blueprint Released

Key Points:
- AI automates policy mapping across workloads, reducing manual configuration time by 60%.
- Integrated with VMware SASE to provide continuous micro‑segmentation.
- Machine‑learning models adapt to new traffic patterns, alerting on anomalous access attempts.
- Case study shows a 45% drop in breach‑related incidents after deployment.
Description:
VMware’s new whitepaper outlines how artificial intelligence can streamline the implementation of Zero Trust security objectives. The solution leverages AI to automatically generate and enforce access policies, continuously adjusting to evolving network conditions and threat landscapes.
Why It Matters:
Enterprises seeking to adopt Zero Trust can accelerate their timelines and reduce operational overhead, while gaining real‑time visibility that strengthens overall security posture.
5️⃣ Unit42 Russian Cyber Threat Targeting 2026 Winter Olympics

Key Points:
- State‑sponsored actors are conducting reconnaissance on Olympic venues and IoT infrastructure.
- Disinformation campaigns aim to erode public confidence ahead of the games.
- Potential DDoS and ransomware attacks on ticketing and broadcast systems are being prepared.
- Threat actors are experimenting with AI‑generated deepfake videos for propaganda.
Description:
Palo Alto Networks’ Unit42 reports that Russian cyber threat groups are actively mapping the digital footprint of the 2026 Winter Olympics. Their operations include probing IoT devices, crafting phishing lures for staff, and planning disruptive attacks to coincide with high‑visibility events.
Why It Matters:
Organizers and national cybersecurity agencies must harden critical infrastructure, monitor for AI‑driven disinformation, and establish rapid response capabilities to protect the integrity of the Games.
6️⃣ Check Point Report Shows Surge in AI‑Generated Phishing Campaigns
Key Points:
- AI‑crafted emails achieved click‑through rates 2.5× higher than traditional phishing.
- Deepfake video attachments were observed in 8% of phishing incidents.
- Malicious actors exploit large‑language models to personalize lures at scale.
- Recommendations include AI‑based email filtering and user awareness training.
Description:
The Check Point 2026 Cyber Security Report highlights a rapid increase in AI‑generated phishing attacks, noting that adversaries are now using large‑language models to automatically produce highly tailored malicious content, including deepfake videos that bypass conventional filters.
Why It Matters:
Organizations must adopt AI‑enhanced email security solutions and reinforce training programs to recognize sophisticated social‑engineering attempts before they compromise credentials.
Stay vigilant and keep your defenses updated.


Member discussion