Ghost Fleet Scan Surge Floods Sensors with Hong Kong‑Based Noise
Ghost Fleet Scan Surge Floods Sensors with Hong Kong‑Based Noise
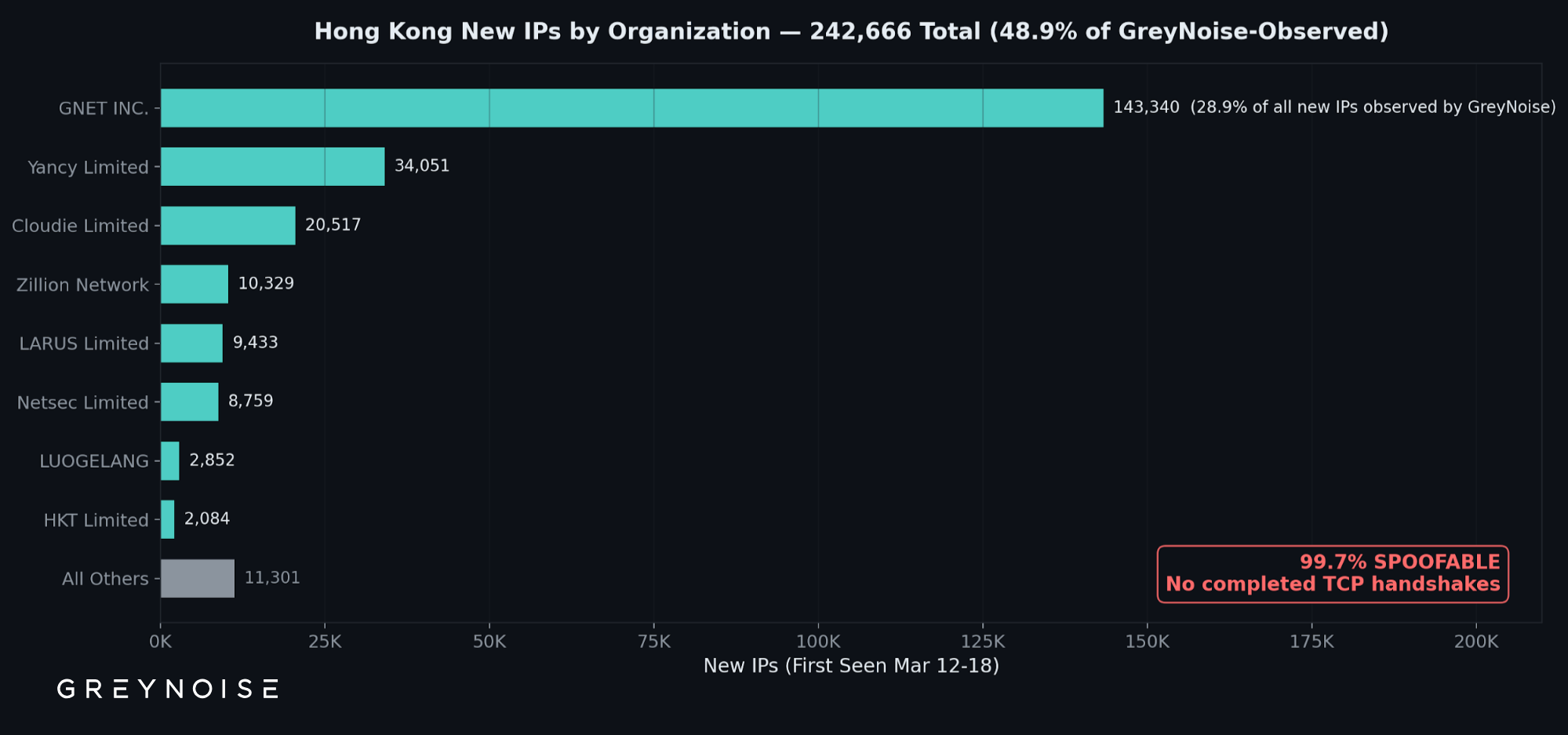
GreyNoise’s latest telemetry shows a sudden spike in internet‑scanning activity dubbed the “Ghost Fleet” surge. Roughly 50 % of the new probes now originate from IP blocks registered in Hong Kong. Most of these scans never complete a TCP handshake, but the sheer volume—tens of thousands of half‑open connections per minute—overloads IDS/IPS sensors and inflates baseline traffic metrics.
For defenders, the flood creates two immediate problems: it drowns out legitimate alerts, generating noise that masks genuine threats, and it contaminates threat‑intelligence feeds with low‑confidence data. Teams should adjust their filtering rules, prioritize verified source reputations (e.g., leverage GreyNoise or similar enrichment), and consider rate‑limiting or black‑holing the identified Hong Kong prefixes until the activity subsides.




Member discussion