Ghost Fleet Scan Spike: Hong Kong IPs Lead Coordinated Probing
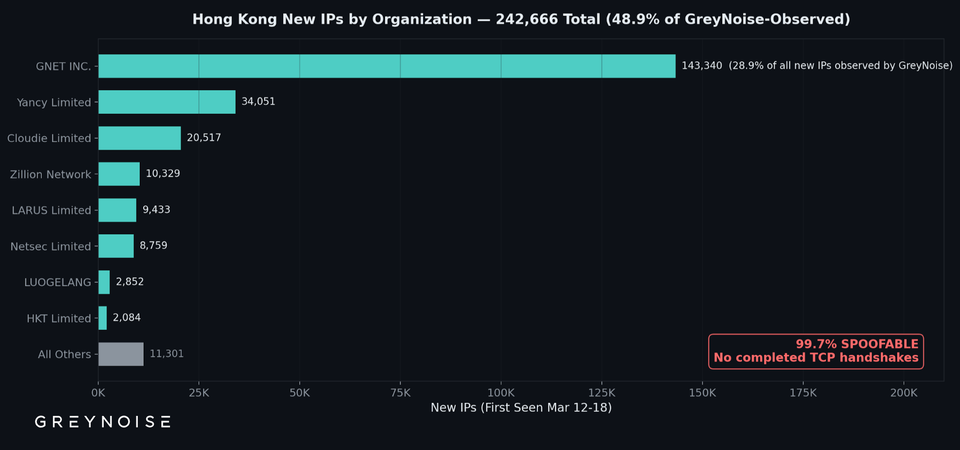
GreyNoise reported a sharp rise in low‑skill scanning activity tied to the Ghost Fleet campaign. Roughly half of the newly seen source IPs originated from Hong Kong, and while most attempts failed to complete a TCP handshake, the sheer volume points to a coordinated effort rather than isolated noise.
The surge likely serves as reconnaissance ahead of a more focused intrusion, giving attackers a map of exposed services and potential entry points. Defenders should treat this as an early warning, tighten network segmentation, update IDS/IPS signatures, and consider temporary blocks or throttling of the identified Hong Kong ranges while monitoring for any escalation.
Categories: Threat Intelligence, SOC & Automation
Source: Read original article




Member discussion