Fake Renewal Notices in Calendar Invites Target Corporate Credentials
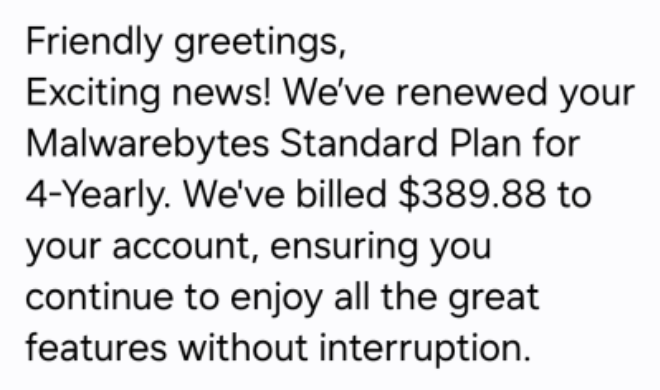
Malwarebytes has uncovered a social‑engineering campaign that uses malicious calendar invites to deliver counterfeit renewal notices. The invites mimic legitimate branding and include a call‑to‑action button that redirects recipients to a spoofed login page designed to harvest credentials. The attack leverages trusted calendar platforms, making the lure appear benign and increasing click‑through rates.
The primary impact is credential theft, leading to compromised email accounts, unauthorized access to internal systems, and potential lateral movement within the network. Because calendar invites are routinely accepted and often auto‑added to users’ schedules, the threat can spread quickly across an organization.
Defenders should prioritize filtering calendar invite metadata, educating users about unexpected renewal prompts, and deploying URL‑reputation services to block known malicious landing pages. Monitoring for anomalous login activity and enforcing multi‑factor authentication will further mitigate the risk of account takeover from this vector.
Categories: Threat Intelligence, Security Culture & Human Factors
Source: Read original article



Comments ()