Fake Malwarebytes Renewal Calendar Invites Deploy Credential‑Harvesting Links
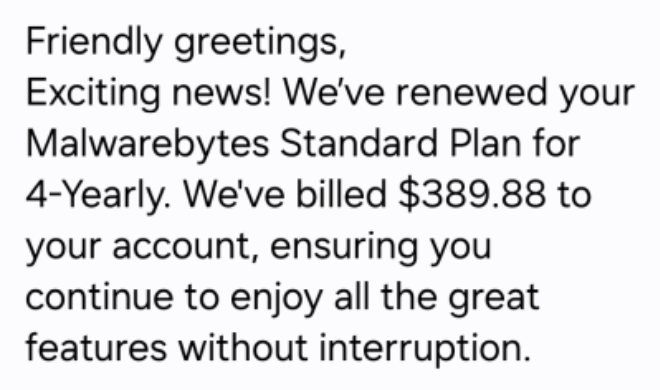
Attackers are sending calendar invitations that mimic Malwarebytes renewal notices. The invites contain malicious URLs that, when clicked, direct users to credential‑phishing pages and subsequently deliver malware payloads. By leveraging calendar platforms instead of traditional email, the campaign bypasses many standard email security controls.
The impact includes potential credential theft, malware infection, and possible lateral movement within the organization. Defenders should treat calendar invites as a threat vector, enforce URL filtering, monitor for anomalous calendar activity, and educate users to verify renewal notices through official channels. Implementing MFA and endpoint protection can further mitigate the risk of compromise from these deceptive invites.
Categories: Threat Intelligence, Malware & Ransomware, Security Culture & Human Factors
Source: Read original article



Member discussion