Fake Google Meet Update Deploys Remote‑Access Trojan with One Click
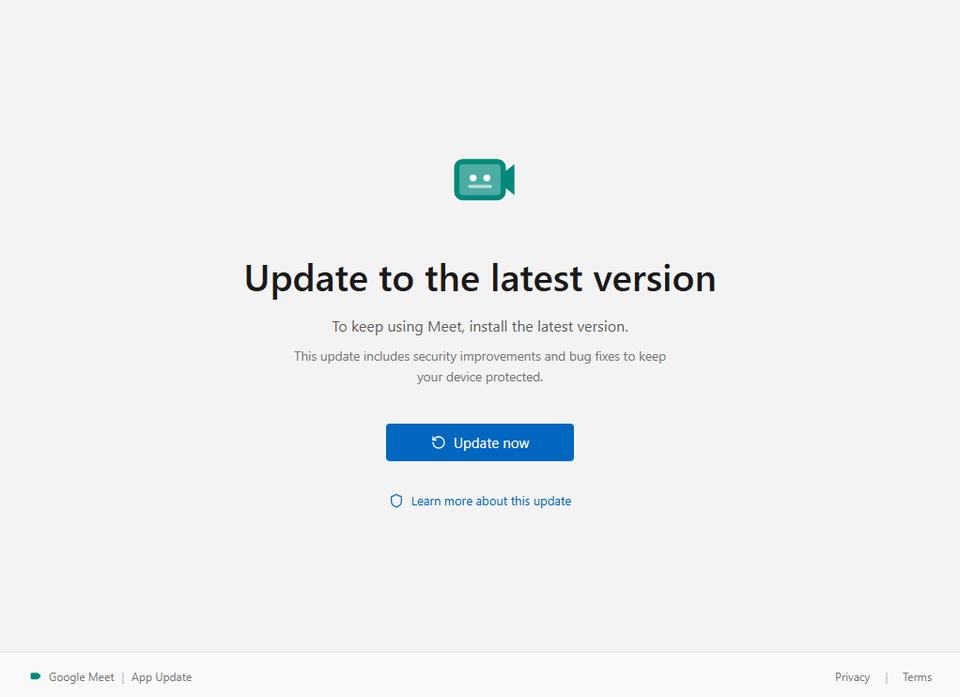
A new phishing campaign observed by Malwarebytes distributes a malicious executable masquerading as a Google Meet update. The file is delivered through deceptive emails and social‑engineered download pages that prompt users to “install” the update. When the executable is run, it silently installs a remote‑access trojan (RAT) that grants the attacker full control over the compromised system.
The RAT enables credential theft, data exfiltration, and lateral movement across the network, posing a severe risk to enterprise environments. Defenders must update endpoint detection rules to flag the counterfeit installer, enforce strict application allow‑lists, and educate users about verifying software updates through official channels. Monitoring for unusual outbound connections and RAT‑specific behaviors will help detect infections early and limit attacker footholds.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article




Member discussion