Fake Google Meet Update Delivers Remote‑Access Malware to Victims
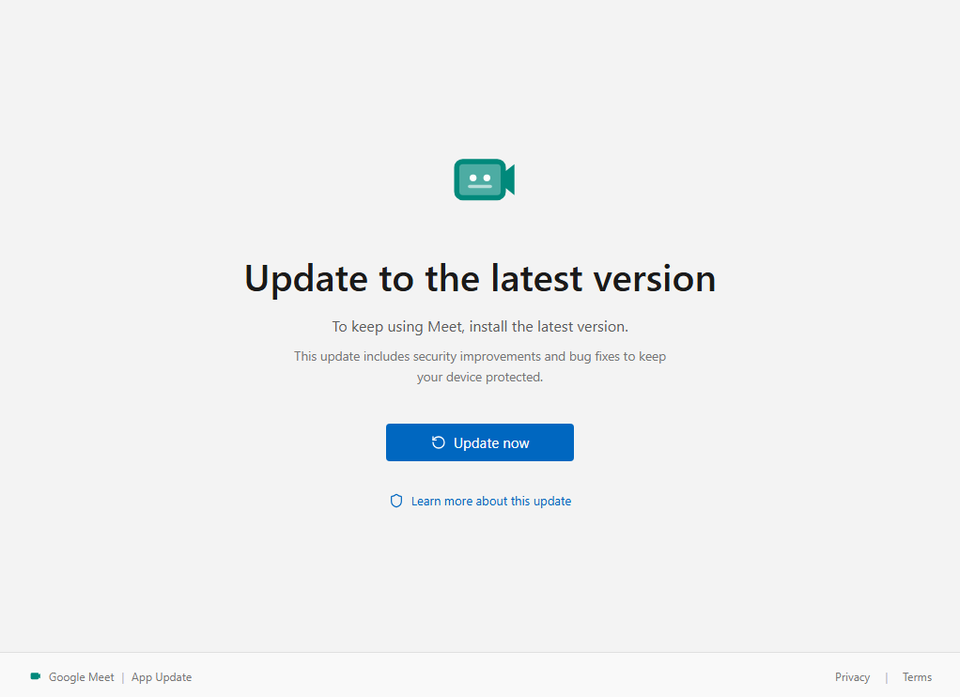
Attackers circulated a phishing campaign that mimics a legitimate Google Meet client update. Recipients receive an email with a bogus “Google Meet Update” attachment or link; when executed, it installs a remote‑access trojan that grants the attacker full control of the endpoint, including screen sharing, keystroke logging, and file manipulation.
Defenders must treat the lure as a high‑severity credential‑and‑access threat. Monitoring for unknown installers named like “GoogleMeetSetup.exe,” blocking execution of unsigned binaries in user directories, and enforcing application whitelisting can stop the payload. Additionally, user awareness training about verifying software sources and the use of multi‑factor authentication will reduce the chance of an attacker leveraging the compromised machine for lateral movement or data exfiltration.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article




Member discussion