Fake Google Meet Update Delivers Full‑Control RAT to Enterprises
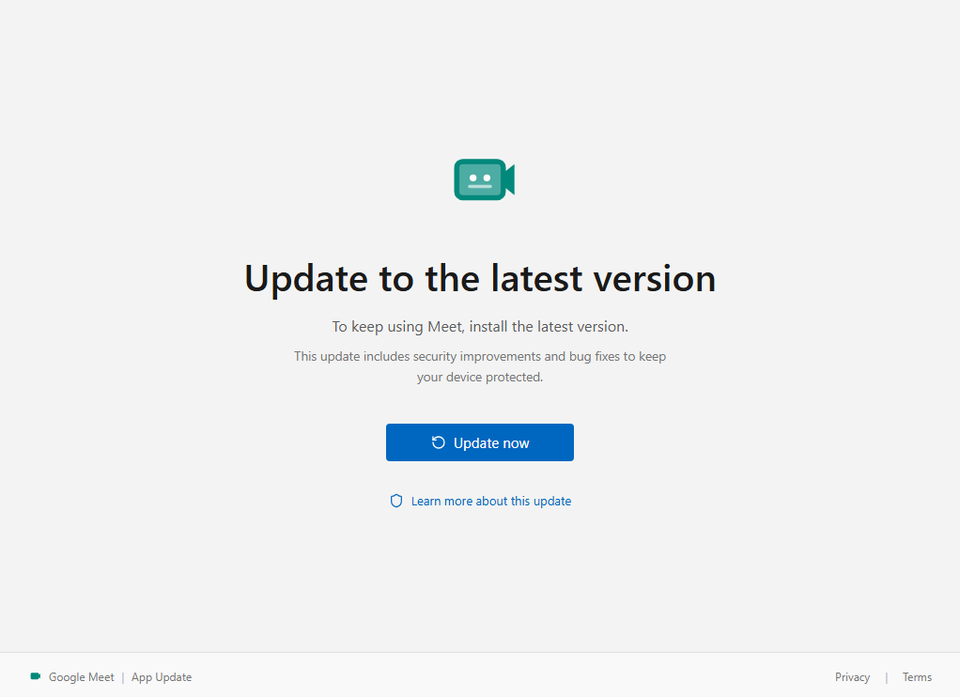
A phishing campaign is distributing a counterfeit Google Meet “update” dialog that mimics the legitimate UI. When a user clicks “Update,” a malicious installer drops a remote‑access trojan (RAT) onto the system, granting the attacker full administrative control of the PC. The payload can capture credentials, move laterally across the network, exfiltrate data, or deploy ransomware, turning a single compromised workstation into a foothold for broader compromise.
Defenders must treat this as a reminder that trusted‑software update mechanisms are prime targets for social engineering. Deploy strict application whitelisting, enforce code‑signing verification, and monitor for unknown executables launched from user profiles. User‑education campaigns should highlight the difference between official update channels (e.g., Google Workspace admin console) and unsolicited pop‑ups, and SOC teams should set alerts for outbound connections to known RAT command‑and‑control domains.
Categories: Malware & Ransomware, Threat Intelligence, Security Culture & Human Factors
Source: Read original article



Member discussion