Why it matters
Executive leadership must reinforce security awareness training and enforce URL verification policies, as compromised credentials provide attackers with footholds into privileged networks, increasing the risk of data exfiltration and lateral movement.
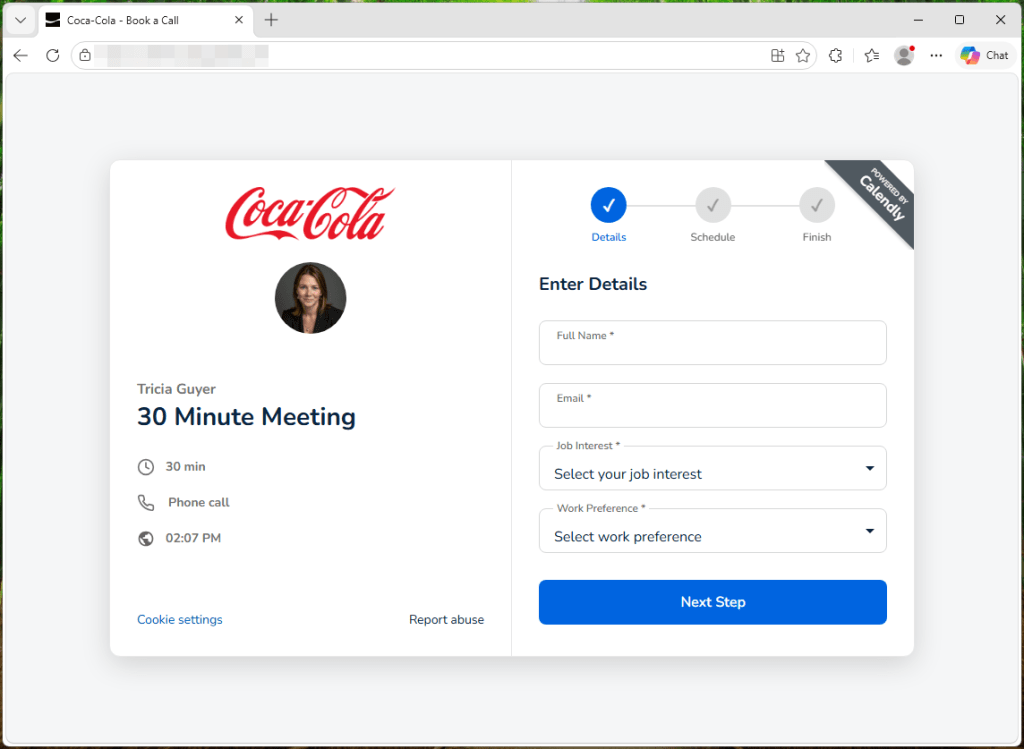
A surge of credential‑theft operations is using fabricated high‑profile job offers to trick job seekers. Victims receive emails that appear to come from well‑known tech firms or recruiters, directing them to look‑alike application websites. Those sites capture entered usernames and passwords and, in many cases, silently drop malicious payloads onto the user’s device to establish persistent access.
The compromised credentials enable attackers to infiltrate corporate networks, move laterally, and exfiltrate sensitive data. For defenders, the campaign highlights the need for robust email filtering, domain‑spoofing detection, and web‑gateway controls, as well as user awareness training focused on employment‑related phishing. Early identification of the counterfeit portals and rapid blocking of associated URLs can prevent both credential theft and malware infection.
Comments ()