Exploit surge in remote tools and OS kernels. AI recommendation poisoning expands attack surface 🛡️🚀
Good morning, February 17, 2026. Here are the top threats shaping executive cybersecurity decisions.
Today's headlines
- BeyondTrust RCE reconnaissance suggests imminent exploitation.
- Dutch telecom provider Odido suffers a data breach affecting customer records.
- QR‑code phishing campaigns rise across web and mobile devices.
- Microsoft Patch Tuesday releases six zero‑day fixes actively exploited in the wild.
- AI recommendation poisoning manipulates chatbot outputs for commercial gain.
1️⃣ BeyondTrust RCE CVE‑2026‑1731 Reconnaissance Signals Imminent Exploitation
Key Points:
- GreyNoise observed active scanning targeting the new BeyondTrust vulnerability.
- CVE‑2026‑1731 enables remote code execution on privileged management consoles.
- Early indicators suggest exploitation may appear in the wild within weeks.
Description:
GreyNoise reported a surge in reconnaissance traffic aimed at BeyondTrust's remote administration tools, specifically probing for CVE‑2026‑1731. The flaw grants attackers the ability to execute arbitrary code with high privileges, potentially compromising entire enterprise networks that rely on BeyondTrust for privileged access management.
Why It Matters:
Enterprises using BeyondTrust must treat this as a high‑severity risk, as successful exploitation could lead to full system takeover. Immediate threat‑intel monitoring and temporary traffic blocking on suspected IPs are essential until patches are released.
2️⃣ Odido Telecom Data Breach Highlights Persistent Customer Data Exposure

Key Points:
- Unauthorized access to Odido’s customer management system.
- Personal data of thousands of subscribers was exfiltrated.
- Incident aligns with a rise in targeting of telecom infrastructure in Europe.
- Remediation included credential rotation and multi‑factor authentication enforcement.
Description:
Checkpoint’s February threat‑intelligence report details a breach at Dutch telecom provider Odido, where attackers accessed the internal customer management platform. The intrusion exposed names, contact details, and service usage records, underscoring the attractive surface area of telecom operators.
Why It Matters:
Telecom breaches have downstream effects on supply‑chain security and can be leveraged for credential stuffing attacks. CISOs must prioritize hardening privileged access, ensure continuous monitoring of privileged accounts, and assess third‑party risk exposure.
3️⃣ QR‑Code Phishing Escalates on Web and Mobile Platforms
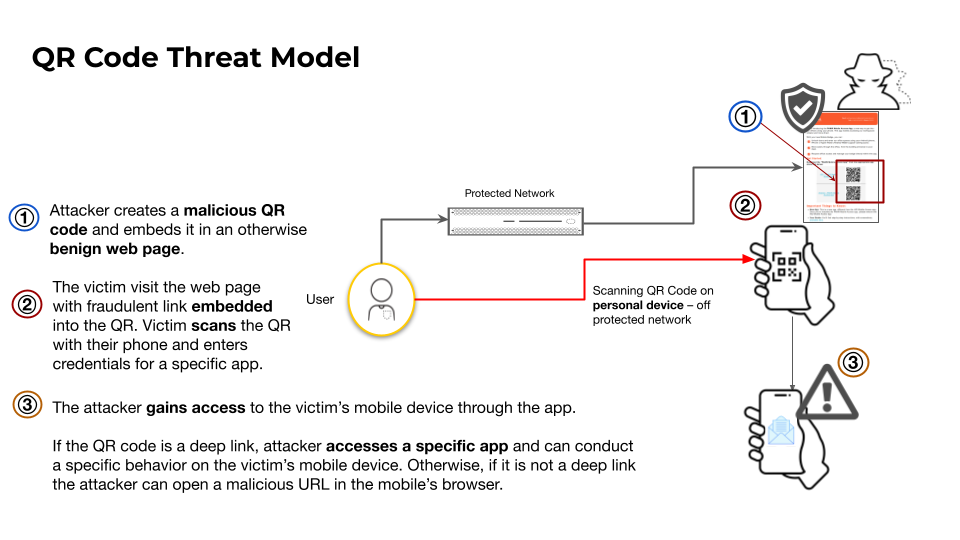
Key Points:
- Attackers embed malicious URLs behind QR codes to bypass traditional filters.
- Deep‑link techniques redirect users to credential‑stealing pages.
- Unit42 identified a surge in QR‑based campaigns across multiple regions.
- Recommended controls include QR scanning policies and URL reputation checks.
Description:
Palo Alto Networks’ Unit42 research reveals that threat actors are increasingly using QR codes as a delivery mechanism for phishing attacks. By encoding malicious URLs and deep links into QR images, they exploit the trust users place in physical signage and digital flyers, leading victims to credential‑theft sites without visible warning cues.
Why It Matters:
Enterprises must update mobile security policies to include QR code scanning restrictions and deploy URL reputation services that can inspect QR‑derived destinations. Failure to do so may result in credential compromise and lateral movement within corporate networks.
4️⃣ Community‑Driven Mentorship Shapes Cybersecurity Talent Pipelines

Key Points:
- Reddit thread consolidates mentorship resources for aspiring professionals.
- Participants share curated lists of newsletters, blogs, and open‑source tools.
- Discussion highlights the importance of continuous learning in a fast‑moving threat landscape.
- Mentors emphasize hands‑on experience with threat‑intel platforms and DFIR utilities.
Description:
The r/cybersecurity community’s Mentorship Monday thread serves as a peer‑driven knowledge hub, offering career advice, education pathways, and recommended tooling for newcomers and seasoned analysts alike. The conversation surfaces emerging learning platforms and practical guidance for navigating certifications and real‑world incident response.
Why It Matters:
Talent acquisition and retention remain critical for security teams. Leveraging community‑sourced mentorship programs can accelerate skill development, reduce onboarding time, and strengthen the overall security posture of organizations.
5️⃣ CrowdStrike Earns Gartner Customers’ Choice for User Authentication

Key Points:
- Recognition based on performance, customer satisfaction, and innovation.
- Validates CrowdStrike’s identity protection and passwordless capabilities.
- Influences procurement decisions for enterprises seeking resilient authentication.
- Highlights a market shift toward integrated XDR and IAM solutions.
Description:
CrowdStrike was announced as a Gartner Customers’ Choice in the 2026 Peer Insights Voice of the Customer for User Authentication. The award reflects the platform’s ability to combine endpoint detection and response with advanced authentication controls, including adaptive MFA and password‑less login flows.
Why It Matters:
For CISOs evaluating authentication stacks, the accolade signals a mature, interoperable solution that can reduce credential‑theft risk while simplifying management. Adoption may also streamline compliance reporting for frameworks that mandate strong authentication.
6️⃣ Falcon Fusion SOAR Accelerates SOC Automation at Scale
Key Points:
- Integrated playbooks reduce mean time to respond by up to 45%.
- Supports automated enrichment, triage, and containment workflows.
- Cloud‑native architecture simplifies deployment across hybrid environments.
- Real‑world case study shows 30% alert fatigue reduction.
Description:
CrowdStrike’s Falcon Fusion SOAR platform enables security operations centers to orchestrate automated response actions across endpoints, cloud workloads, and third‑party tools. The blog outlines how pre‑built playbooks and custom scripting can streamline incident handling from detection to remediation.
Why It Matters:
Automation reduces analyst burnout and improves response consistency, essential for organizations facing high alert volumes. Scaling SOAR capabilities can translate into measurable risk reduction and operational cost savings.
7️⃣ VMware vDefend Advances Zero‑Trust Lateral Security for Private Clouds

Key Points:
- vDefend provides continuous micro‑segmentation and lateral movement detection.
- Leverages AI to model normal workload communication patterns.
- Seamless integration with existing VMware Cloud Foundation stacks.
- Enables compliance with emerging zero‑trust mandates.
Description:
VMware’s vDefend solution extends zero‑trust principles to private cloud environments by continuously monitoring workload interactions and automatically enforcing micro‑segmentation policies. AI‑driven analytics identify anomalous lateral traffic that may indicate compromised assets.
Why It Matters:
As enterprises migrate workloads to private clouds, traditional perimeter defenses become insufficient. vDefend offers a practical path to enforce zero‑trust controls, limiting blast radius of potential breaches.
8️⃣ Microsoft Patch Tuesday Unveils Six Actively Exploited Zero‑Days

Key Points:
- CVE‑2026‑21510 bypasses Windows Shell protections with a single click.
- CVE‑2026‑21513 targets the MSHTML engine; CVE‑2026‑21514 affects Microsoft Word.
- Exploits observed in the wild before patch release.
- Enterprises urged to apply updates immediately and monitor for IOCs.
Description:
Krebs on Security reported that Microsoft’s February 2026 Patch Tuesday addressed more than 50 vulnerabilities, including six zero‑day flaws already seen in active attacks. Notably, CVE‑2026‑21510 enables attackers to execute code via a crafted hyperlink without user consent.
Why It Matters:
The presence of exploited zero‑days heightens urgency for rapid patch deployment and threat‑intel monitoring. Organizations lagging in patch management face elevated risk of ransomware and data exfiltration.
9️⃣ AI Recommendation Poisoning Manipulates Microsoft Chatbot Outputs

Key Points:
- Attack uses “Summarize with AI” buttons to inject biased prompts.
- Technique mirrors classic search‑engine poisoning but targets LLMs.
- Demonstrated ability to alter chatbot recommendations for commercial gain.
- Mitigation includes input validation and monitoring of AI‑generated content.
Description:
Microsoft’s Defender Security Research team disclosed a novel “AI Recommendation Poisoning” method where malicious actors embed specially crafted prompts behind “Summarize with AI” buttons on websites. The poisoned prompts steer large language model chatbots toward favorable, yet deceptive, answers.
Why It Matters:
Enterprises deploying AI‑driven assistants must safeguard against prompt injection, as compromised responses can influence user decisions, promote malicious services, or leak sensitive information. Robust prompt sanitization and continuous model monitoring are critical controls.
🔟 Student Loan Data Breach Exposes 2.5 Million Records

Key Points:
- Breach compromised personal and financial data of loan borrowers.
- Attack traced to a third‑party service provider vulnerability.
- Regulatory fallout includes potential GDPR and U.S. state investigations.
- Recommended actions: credit monitoring, credential resets, and vendor security reviews.
Description:
Threatpost reported a breach affecting a major student loan servicer, exposing approximately 2.5 million individuals’ records, including Social Security numbers, loan balances, and contact information. The intrusion originated from a compromised third‑party API used for loan verification.
Why It Matters:
Financial data breaches increase identity theft risk and attract regulatory penalties. Organizations handling sensitive consumer data must enforce strict third‑party risk assessment and implement real‑time anomaly detection to mitigate similar incidents.
Stay vigilant and prioritize the controls that protect your most critical assets.
Member discussion