Elevating Threat Detection and Resilience Amid Advanced AI Exploits and Supply‑Chain Risks

Good morning, March 12, 2026. Here’s the latest cyber and AI threat intel.
Today's headlines
- GreyNoise integration streamlines noisy‑IP filtering in Google SecOps
- CISO guide to scaling phishing detection with AI‑driven automation
- Iran‑backed wiper campaign targets medtech giant Stryker
- Cloudflare deploys AI‑based account abuse protection across its platform
- Critical Android lock‑screen bypass disclosed, patch pending
1️⃣ GreyNoise integrates with Google SecOps to sharpen detection
Key Points:
- Configurable real‑time blocklists block malicious IPs instantly
- Enriches incident context, reducing investigation time
- Filters out low‑priority alerts from mass internet scanners
- Improves SOC efficiency for small and mid‑sized enterprises
Description:
GreyNoise launched an integration with Google SecOps, allowing security teams to pull noisy‑IP intelligence directly into Google’s security tools for automated enrichment, blocking, and reporting.
Why It Matters:
By minimizing false positives and automating blocklist enforcement, organizations can accelerate response times, lower exposure to attacker infrastructure, and preserve analyst capacity for higher‑value work.
2️⃣ Scale phishing detection with AI‑driven triage

Key Points:
- Three‑step framework: data collection, AI enrichment, continuous tuning
- Automation reduces manual review overhead
- Highlights limits of traditional CVSS scoring for phishing risk
- Tailors approach for lean security teams
Description:
The Hacker News article outlines a practical three‑step method for CISOs to expand phishing detection capabilities using AI analytics, automated enrichment, and ongoing tuning to keep pace with evolving email threats.
Why It Matters:
Phishing remains the leading entry vector; adopting an AI‑enabled, scalable process helps leaders allocate resources efficiently, improve detection rates, and diminish the likelihood of credential‑based breaches.
3️⃣ Iran‑backed wiper attack hits medtech giant
Key Points:
- Stryker targeted with destructive wiper malware
- Attack attributed to state‑sponsored Iranian group
- Potential shutdown of medical device production lines
- Highlights geopolitical motivations in cyber‑espionage
Description:
Krebs on Security reports that an alleged Iran‑backed threat actor deployed a wiper against Stryker, aiming to erase data and impair manufacturing operations within the medical technology sector.
Why It Matters:
Disruption of medical‑technology supply chains can affect patient care and regulatory compliance; robust backup, segmentation, and incident response are critical to mitigate such high‑impact attacks.
4️⃣ OWASP retires Meetup platform
Key Points:
- Official shutdown of OWASP’s community Meetup site
- Members encouraged to migrate to Discord, GitHub, and other channels
- Aims to modernize collaboration for secure‑software initiatives
- Potential temporary impact on vulnerability discussion continuity
Description:
OWASP announced the retirement of its long‑standing Meetup platform, directing the community to transition discussions and event coordination to newer collaboration tools that better support secure software development efforts.
Why It Matters:
Central venues for sharing vulnerability intelligence are essential for coordinated defense; the move underscores the need for adaptable community infrastructure while offering more integrated, real‑time communication options.
5️⃣ Cloudflare launches account abuse protection

Key Points:
- AI builds API call graphs to spot abnormal usage
- Detects both bot‑driven and human‑initiated fraudulent activity
- Integrates across Cloudflare services for unified protection
- Reduces risk of credential stuffing and account takeover
Description:
Cloudflare introduced Account Abuse Protection, an AI‑driven system that models API call patterns to identify and block fraudulent behavior targeting customer accounts across its network.
Why It Matters:
With account takeover attacks on the rise, early detection and automated blocking protect user trust, limit data exposure, and decrease downstream breach impact for SaaS providers.
6️⃣ New Android lock‑screen bypass discovered

Key Points:
- Exploits race condition to bypass lock screen in <60 seconds
- Affects devices using specific chipset firmware
- Requires minimal user interaction to trigger
- Manufacturers working on patch rollout
Description:
Malwarebytes reported a critical Android vulnerability that allows an attacker to bypass the lock screen by exploiting a timing flaw, granting full device access in under a minute.
Why It Matters:
Mobile devices are integral to corporate BYOD strategies; unpatched phones could become entry points for data theft or credential harvesting, emphasizing the need for rapid patch management.
7️⃣ AWS introduces AMI Lineage for image lifecycle
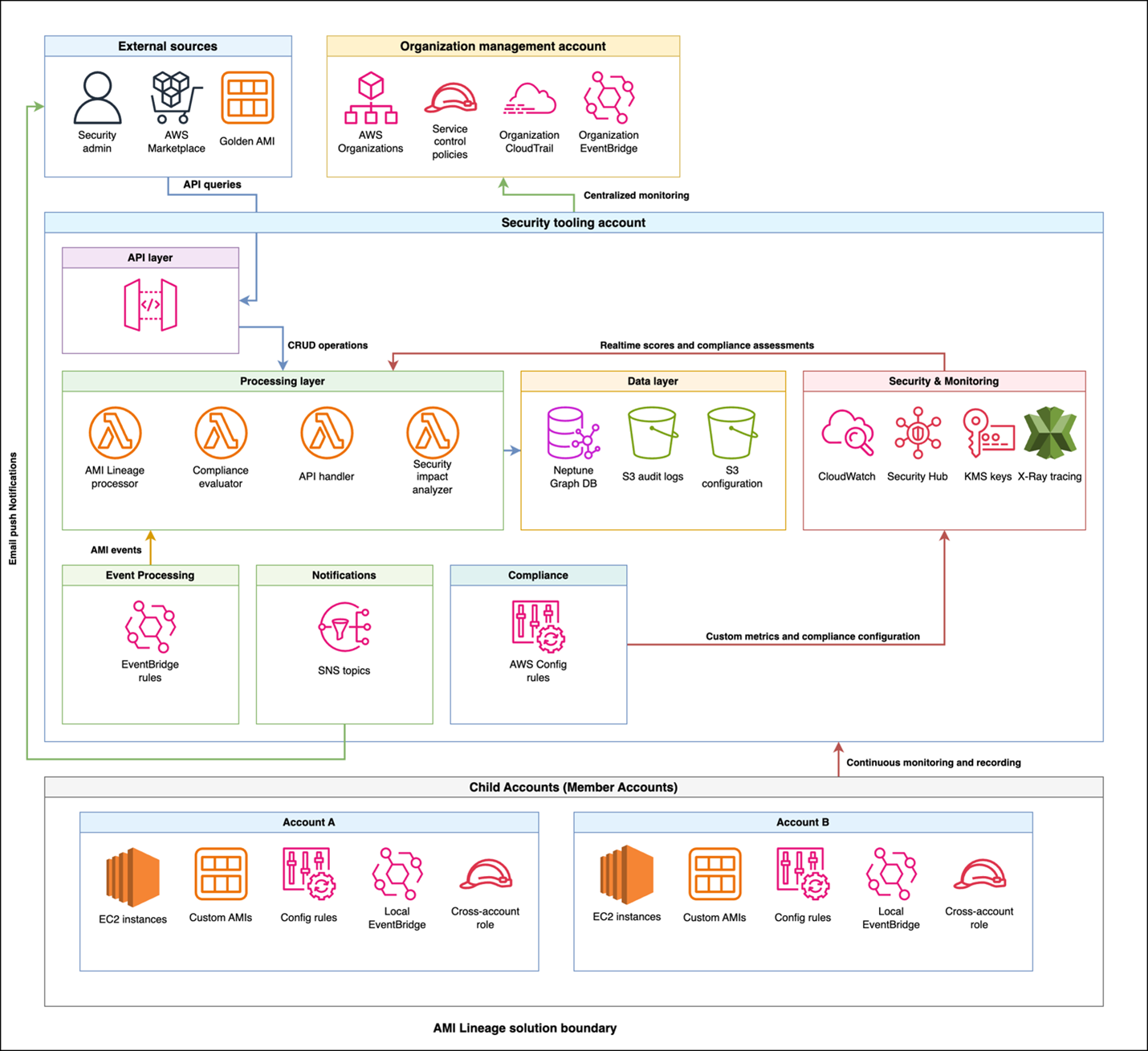
Key Points:
- Tracks creation, modification, and approval of AMIs
- Provides compliance dashboards and real‑time security metrics
- Automates remediation logging and audit‑trail generation
- Supports rapid decision‑making on image deployment
Description:
AWS published guidance on using AMI Lineage to manage the full lifecycle of Amazon Machine Images, delivering visibility into compliance status, workflow approvals, and automated audit records for security teams.
Why It Matters:
Ensuring only vetted, secure images reach production reduces the risk of vulnerable or malicious AMIs compromising cloud workloads, strengthening overall cloud security posture.
8️⃣ Student loan breach exposes 2.5 M records

Key Points:
- Personal and financial data of 2.5 million borrowers leaked
- Root cause: misconfigured cloud storage bucket
- Triggers regulator scrutiny of education‑finance providers
- Highlights third‑party and cloud‑config risk
Description:
ThreatPost detailed a breach at a major student‑loan servicer where insecure cloud storage exposed the records of 2.5 million borrowers, prompting investigations by consumer‑privacy regulators.
Why It Matters:
Education‑finance data is highly sensitive; the incident stresses the importance of rigorous vendor risk management, cloud‑configuration hygiene, and rapid breach‑response capabilities.
9️⃣ OpenClaw AI agents evolve with semantic worms
Key Points:
- Shows AI‑generated reverse shells and semantic worms
- Introduces cognitive rootkits that adapt to defenses
- Demonstrates fully automated infection chains
- Highlights emerging AI‑enabled malware sophistication
Description:
VirusTotal’s blog post examines the second part of the OpenClaw series, revealing how AI agents can create sophisticated infection mechanisms such as semantic worms and cognitive rootkits to evade traditional detection.
Why It Matters:
As attackers harness AI to automate weaponization, defenders must upgrade detection to identify behavioral anomalies and AI‑generated code, otherwise modern malware may slip past conventional defenses.
🔟 Autonomous cyber‑attack agents evaluated for generalization

Key Points:
- Academic study of AI agents’ ability to generalize attacks
- Proposes metrics for robustness across diverse environments
- Experiments on simulated networks reveal transferability
- Raises ethical concerns about weaponized autonomous AI
Description:
An arXiv pre‑print investigates how autonomous cyber‑attack agents can generalize across different network contexts, offering evaluation frameworks and discussing implications for future AI‑driven threats.
Why It Matters:
Understanding the generalization capabilities of AI attackers helps defenders design resilient controls and informs policy decisions on regulating autonomous offensive technologies.
Stay vigilant and keep your defenses ahead of emerging threats.
Member discussion