Elevating Enterprise Resilience Amid Escalating Supply‑Chain, Ransomware, and Botnet Threats 🚀

Good morning, March 23 2026 – here’s the latest cyber risk intel you need to act on.
Today's headlines
- GreyNoise integrates with Google SecOps to cut noise and block attackers in real time.
- Critical supply‑chain backdoor discovered in the Trivy vulnerability scanner.
- Interlock ransomware campaign targets enterprise firewalls, prompting new AWS guidance.
- Federal takedown disrupts large IoT botnets responsible for massive DDoS attacks.
- Cloudflare introduces account‑abuse protection to thwart automated credential abuse.
1️⃣ GreyNoise + Google SecOps: Real‑time Threat Blocking
Key Points:
- Fully configurable blocklists automatically block malicious IPs.
- Enhances SOC efficiency by filtering noisy internet scans.
- Provides contextual enrichment for incident investigations.
- Supports integration with SIEM, SOAR, TIP, and firewalls.
Description:
GreyNoise announced new integrations with Google SecOps, delivering real‑time, fully configurable blocklists that automatically block malicious traffic. The partnership aims to reduce alert fatigue, speed incident triage, and empower threat‑hunting teams with enriched context across SIEM, SOAR, TIP, and firewall solutions.
Why It Matters:
For CISOs, the integration translates to fewer false‑positive alerts, faster investigation cycles, and stronger perimeter defenses without additional staffing, directly improving the organization’s security posture and operational resilience.
2️⃣ Trivy Supply‑Chain Backdoor Exposes CI/CD Pipelines

Key Points:
- Attackers inserted credential‑stealing malware into official Trivy releases.
- Compromised GitHub Actions propagated a self‑replicating worm (CanisterWorm).
- Thousands of CI/CD workflows were affected, exposing secrets and build artifacts.
- Patch and secret rotation urgently recommended.
Description:
The widely used Trivy vulnerability scanner was backdoored, allowing attackers to inject malicious code into official releases and associated GitHub Actions. The breach triggered a cascade of supply‑chain compromises, with the self‑propagating CanisterWorm spreading across CI/CD pipelines that failed to rotate secrets promptly.
Why It Matters:
Supply‑chain attacks directly threaten software integrity and can compromise the entire development lifecycle. Organizations must enforce strict version controls, rapid patching, and secret‑management policies to prevent similar breaches.
3️⃣ OWASP Retires Meetup Platform, Shifts Focus to Vulnerability Intelligence
Key Points:
- OWASP announces retirement of its community Meetup platform.
- Strategic pivot toward a unified global vulnerability intelligence framework.
- Encourages continued collaboration via OWASP AI Exchange and Open‑Source projects.
- Calls for community input on new intelligence-sharing mechanisms.
Description:
OWASP disclosed that it will sunset its Meetup platform, redirecting resources to develop a comprehensive vulnerability intelligence ecosystem. The organization highlighted upcoming initiatives such as the OWASP AI Exchange and a unified framework for global vulnerability data sharing.
Why It Matters:
A consolidated intelligence platform promises faster, more actionable threat data for security teams, reducing reliance on fragmented community channels and enhancing coordinated defense efforts.
4️⃣ Advanced Flow Enhances Android Sideloading Security
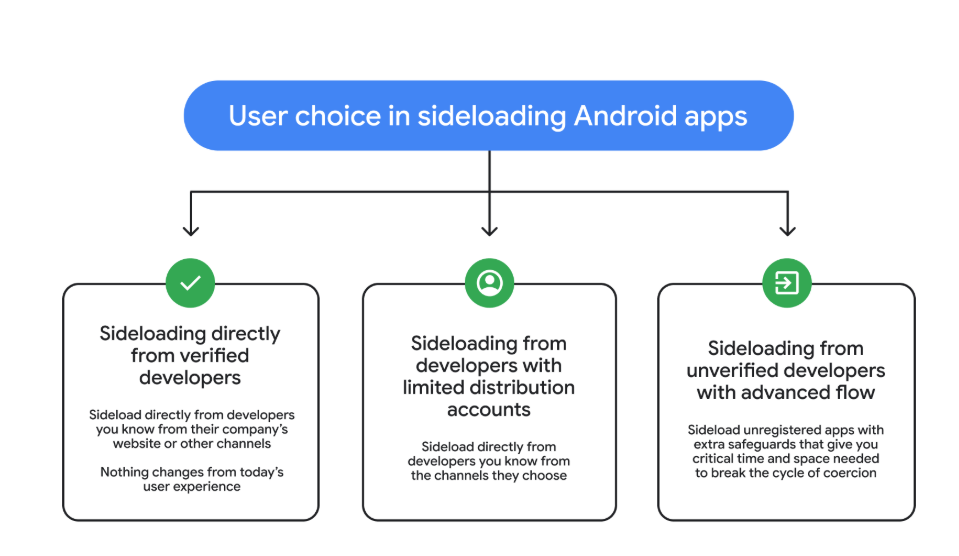
Key Points:
- Introduces runtime verification of app signatures during sideload.
- Blocks unauthorized code injection and malicious payloads.
- Integrates with existing Android security frameworks for seamless adoption.
- Reduces attack surface for credential‑stealing and ransomware apps.
Description:
Malwarebytes unveiled Advanced Flow, a new technology designed to make Android sideloading safer by performing real‑time verification of application signatures and blocking unauthorized code execution. The solution works alongside native Android security layers to mitigate malicious sideloaded apps.
Why It Matters:
Enterprises managing Android fleets can now enforce stricter controls on third‑party app installations, limiting exposure to mobile ransomware and credential‑theft campaigns that often bypass traditional app store checks.
5️⃣ FBI‑Led Operation Takes Down Massive IoT Botnets
Key Points:
- Coordinated takedown of botnets comprising millions of compromised IoT devices.
- Disruption halted ongoing DDoS campaigns targeting critical infrastructure.
- Authorities seized command‑and‑control servers across multiple jurisdictions.
- Guidance issued for hardening IoT devices against future recruitment.
Description:
Federal law enforcement agencies announced the successful disruption of several large‑scale IoT botnets responsible for recent high‑volume DDoS attacks. The operation involved takedown of C2 servers and remediation steps for affected device manufacturers.
Why It Matters:
The takedown underscores the persistent risk posed by insecure IoT devices and highlights the need for proactive vulnerability management, network segmentation, and continuous monitoring to prevent botnet enlistment.
6️⃣ Interlock Ransomware Targets Enterprise Firewalls, AWS Warns
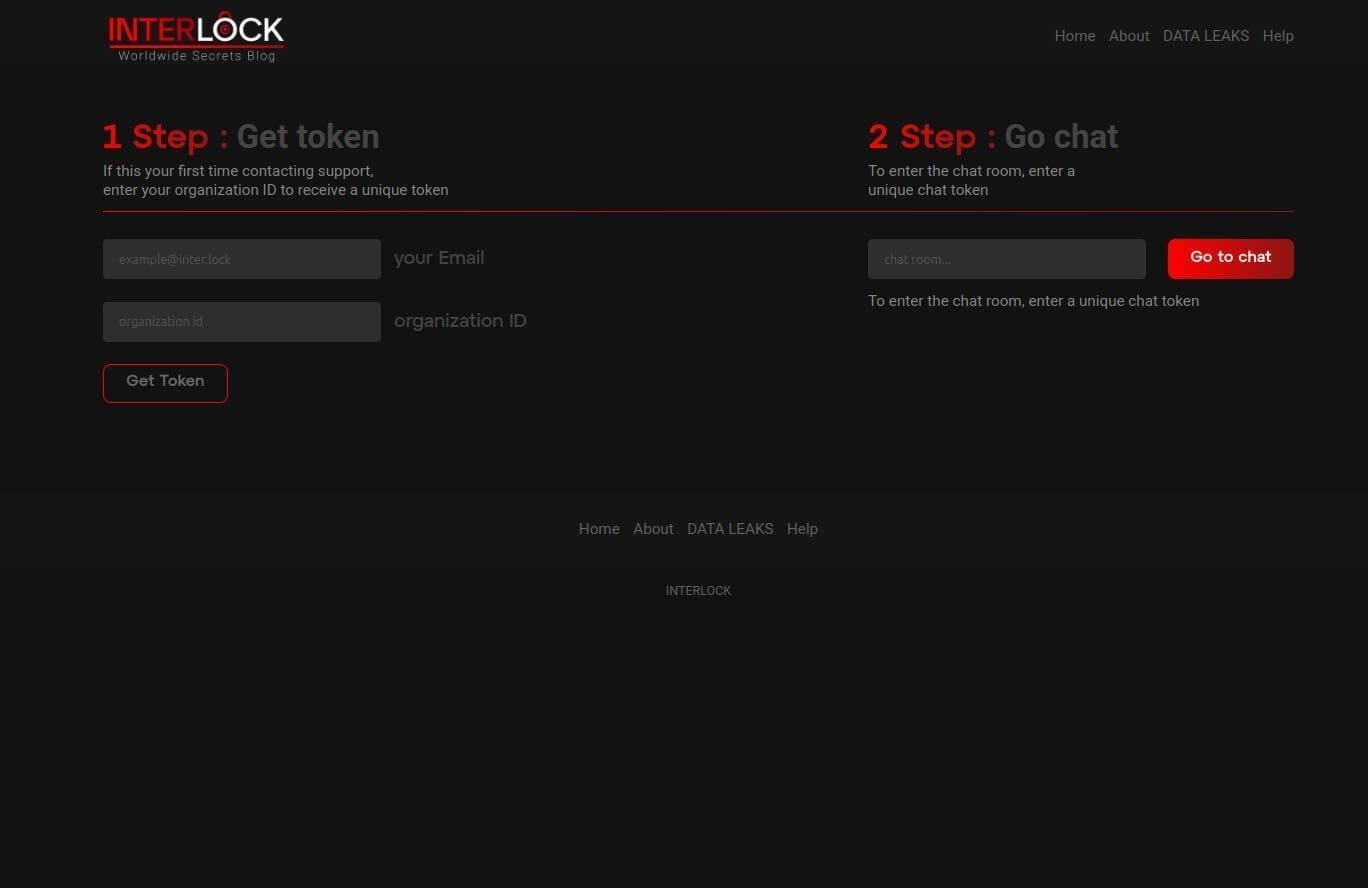
Key Points:
- New ransomware strain, Interlock, exploits firewall management interfaces.
- Observed C2 domains and malicious payloads active March 2026.
- Recommendations include network segmentation, MFA, and firewall firmware updates.
- AWS provides detection signatures for integration with GuardDuty.
Description:
Amazon Web Services’ threat intelligence team identified the Interlock ransomware campaign, which specifically targets enterprise firewalls to gain network persistence before encrypting data. The blog outlines observed C2 infrastructure and remediation steps.
Why It Matters:
Firewalls are critical control points; compromise can lead to lateral movement and data encryption across the enterprise. Immediate hardening and monitoring are essential to thwart this emerging ransomware vector.
7️⃣ Student Loan Data Breach Impacts 2.5 M Borrowers

Key Points:
- Unauthorized access exposed personal and financial data of 2.5 million individuals.
- Compromised fields include Social Security numbers, loan balances, and contact details.
- Incident attributed to a misconfigured cloud storage bucket.
- Recommendations emphasize encryption at rest and strict access controls.
Description:
A major student loan servicing platform suffered a breach that exposed the records of 2.5 million borrowers. The leak resulted from a cloud storage bucket left publicly accessible, revealing sensitive personal and financial information.
Why It Matters:
The breach highlights the consequences of improper cloud configurations and the importance of data‑centric security controls for organizations handling regulated personal data.
8️⃣ OpenClaw AI Agents Deploy Semantic Worms, Reverse Shells
Key Points:
- OpenClaw AI agents automate infection chaining with semantic worms.
- Demonstrated capability to spawn reverse shells and cognitive rootkits.
- Uses advanced language models to adapt payloads to target environments.
- Calls for enhanced AI‑focused detection and sandboxing strategies.
Description:
VirusTotal’s research blog detailed how OpenClaw AI agents can generate semantic worms and cognitive rootkits that automatically adapt to target systems, establishing reverse shells for persistent control. The study emphasizes the emerging risk of AI‑driven malware automation.
Why It Matters:
Traditional signature‑based defenses may struggle against rapidly mutating AI‑generated threats, urging security teams to adopt behavioral analytics and AI‑aware detection frameworks.
9️⃣ ISC Stormcast Highlights Surge in Scanning Activity
Key Points:
- Significant increase in SSH/Telnet scanning observed across multiple regions.
- Daily port‑scan volume rose 27 % compared to the previous week.
- Threat actors appear to be probing for vulnerable IoT and legacy systems.
- Recommendation: enforce strong authentication and monitor inbound scan traffic.
Description:
The Internet Storm Center’s Stormcast podcast for March 23 2026 reported a notable uptick in scanning activity targeting SSH and Telnet services, indicating heightened reconnaissance efforts by threat actors seeking vulnerable IoT and legacy devices.
Why It Matters:
Elevated scanning activity often precedes larger intrusion campaigns; early detection and mitigation can reduce exposure to credential‑stuffing and unauthorized access attempts.
🔟 Cloudflare Launches Account Abuse Protection
Key Points:
- Introduces email risk tiers (low, medium, high) for account creation.
- Combines behavioral analysis with infrastructure reputation scoring.
- Allows customers to set custom thresholds for friction versus security.
- Aims to block automated fraud and credential‑stuffing attacks.
Description:
Cloudflare unveiled its Account Abuse Protection service, which evaluates email address risk using pattern analysis and infrastructure data. The solution provides configurable risk tiers that enable clients to enforce appropriate friction during account creation, reducing automated abuse.
Why It Matters:
By filtering out high‑risk registrations, organizations can diminish the success rate of credential‑stuffing attacks and protect downstream services from abuse, enhancing overall trust and resilience.
Stay vigilant and keep your defenses adaptive.

Member discussion