Elevated Zero‑Day Risks and AI‑Powered Threats Demand Proactive Resilience
Good morning, March 9, 2026 – Here’s the latest executive intel for security leaders.
Today's headlines
- Zero‑day vulnerabilities continue to outmaneuver perimeter defenses.
- AI‑driven attack techniques broaden the threat surface across enterprises.
- Integrated threat intel platforms streamline SOC alert hygiene.
- IoT devices, especially IP cameras, become focal points in geopolitical conflicts.
- Mid‑market security platforms are finally delivering AI‑enhanced investigation capabilities.
1️⃣ GreyNoise Intelligence Now Integrated with CrowdStrike Falcon
Key Points:
- Real‑time blocklists automatically filter noisy internet scanners.
- Enriches incident investigations with context on malicious IP activity.
- Supports vulnerability prioritization by highlighting actively exploited CVEs.
- Accelerates threat‑hunting cycles with built‑in intel feeds.
Description:
GreyNoise has expanded its threat‑intelligence offering to the CrowdStrike Falcon platform, delivering configurable, real‑time blocklists and contextual data on malicious IPs directly within Falcon’s console. The integration aims to reduce false positives, improve SOC efficiency, and provide actionable insights for vulnerability management and threat hunting.
Why It Matters:
By embedding GreyNoise data into Falcon, organizations can cut through the noise of mass scanning activity, allowing analysts to focus on genuine threats. This directly supports risk reduction by preventing unnecessary alerts and speeds up response times, strengthening overall security posture.
2️⃣ Perimeter Firewalls Alone Can’t Stop Zero‑Day Exploits Like GoAnywhere MFT

Key Points:
- CVE‑2025‑10035 scored 10.0 CVSS, enabling remote code execution via deserialization.
- Threat actors bypassed traditional perimeter defenses to compromise the license servlet.
- CISA advises deeper defense‑in‑depth for widely deployed shared services.
Description:
The GoAnywhere MFT zero‑day vulnerability, CVE‑2025‑10035, was exploited by the Storm‑1175 actor group, demonstrating how high‑severity flaws can evade perimeter firewalls. The incident underscores the need for layered security controls beyond the network edge, as the exploit achieved full system compromise despite existing perimeter safeguards.
Why It Matters:
Enterprises relying solely on perimeter defenses risk catastrophic breach when critical applications contain undisclosed vulnerabilities. Implementing comprehensive detection, application‑level controls, and rapid patching processes is essential to mitigate exposure to such high‑impact zero‑days.
3️⃣ AI Assistants Redefine Attack Surfaces with Prompt Injection
Key Points:
- LLMs can be misled via crafted prompts in overlooked input fields.
- Introduces ‘AI fragility’ as a new pillar of defensive strategy.
- Attack surface expands as agents become embedded in workflows.
Description:
Researchers highlighted that adversaries are leveraging prompt injection techniques against AI assistants, tricking large language models into executing malicious actions. This new threat vector demands that organizations incorporate safeguards against AI fragility, complementing traditional confidentiality, integrity, and availability controls.
Why It Matters:
The burgeoning reliance on AI agents amplifies risk, as compromised prompts can lead to data exfiltration or system manipulation. Addressing AI‑specific vulnerabilities is critical to maintaining operational resilience in increasingly automated environments.
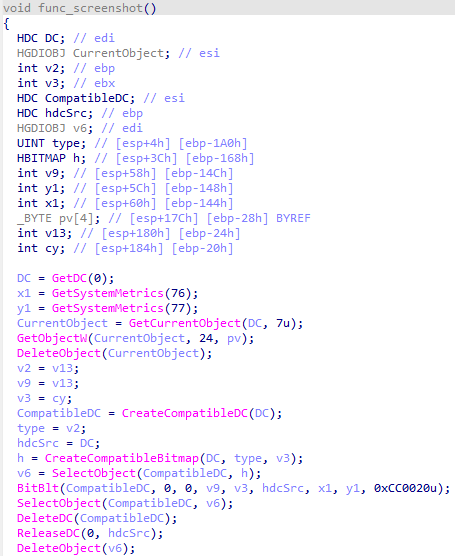
4️⃣ LummaStealer Resurfaces Paired with CastleLoader to Evade Detection
Key Points:
- Malware now mimics legitimate user behavior for initial access.
- Combines infostealer capabilities with sophisticated loader techniques.
- Comprehensive IoC list shared on GitHub for faster detection.
Description:
The LummaStealer infostealer, now coupled with the CastleLoader module, has evolved to better conceal its activities by blending with normal user actions. Analysts emphasize the importance of understanding the social‑engineering context and delivery mechanisms to detect and mitigate this threat effectively.
Why It Matters:
As attackers refine malware to appear benign, traditional signature‑based defenses lose efficacy. Security teams must leverage behavioral analytics and up‑to‑date IoCs to thwart these advanced credential‑theft campaigns.
5️⃣ Threat Actors Operationalize AI for Sophisticated Campaigns

Key Points:
- AI generates convincing phishing content and deepfake media.
- Automation accelerates credential‑stuffing and evasion techniques.
- Microsoft outlines AI‑aware defensive measures and tooling.
Description:
Microsoft’s security blog outlines how adversaries are integrating AI into their tradecraft, from automating phishing lure creation to deploying deepfake audio for social engineering. The post also details Microsoft’s suite of AI‑enhanced protection capabilities designed to counter these emerging tactics.
Why It Matters:
The fusion of AI with malicious operations magnifies attack scale and success rates, urging defenders to adopt AI‑driven detection and response tools to stay ahead of evolving tactics.
6️⃣ Falcon Next‑Gen SIEM Simplifies Sensor‑Native Log Collection
Key Points:
- Native log ingestion eliminates complex agent deployments.
- Accelerates onboarding, reducing time‑to‑value for SIEM deployments.
- Improves insider threat visibility through unified data sources.
Description:
CrowdStrike’s Falcon Next‑Gen SIEM now offers sensor‑native log collection, allowing organizations to ingest data directly from endpoints without additional agents. This streamlines deployment, reduces configuration errors, and enhances the overall efficiency of security operations.
Why It Matters:
Rapid, error‑free onboarding empowers SOCs to focus on threat analysis rather than infrastructure minutiae, boosting detection capabilities and compliance readiness across diverse environments.
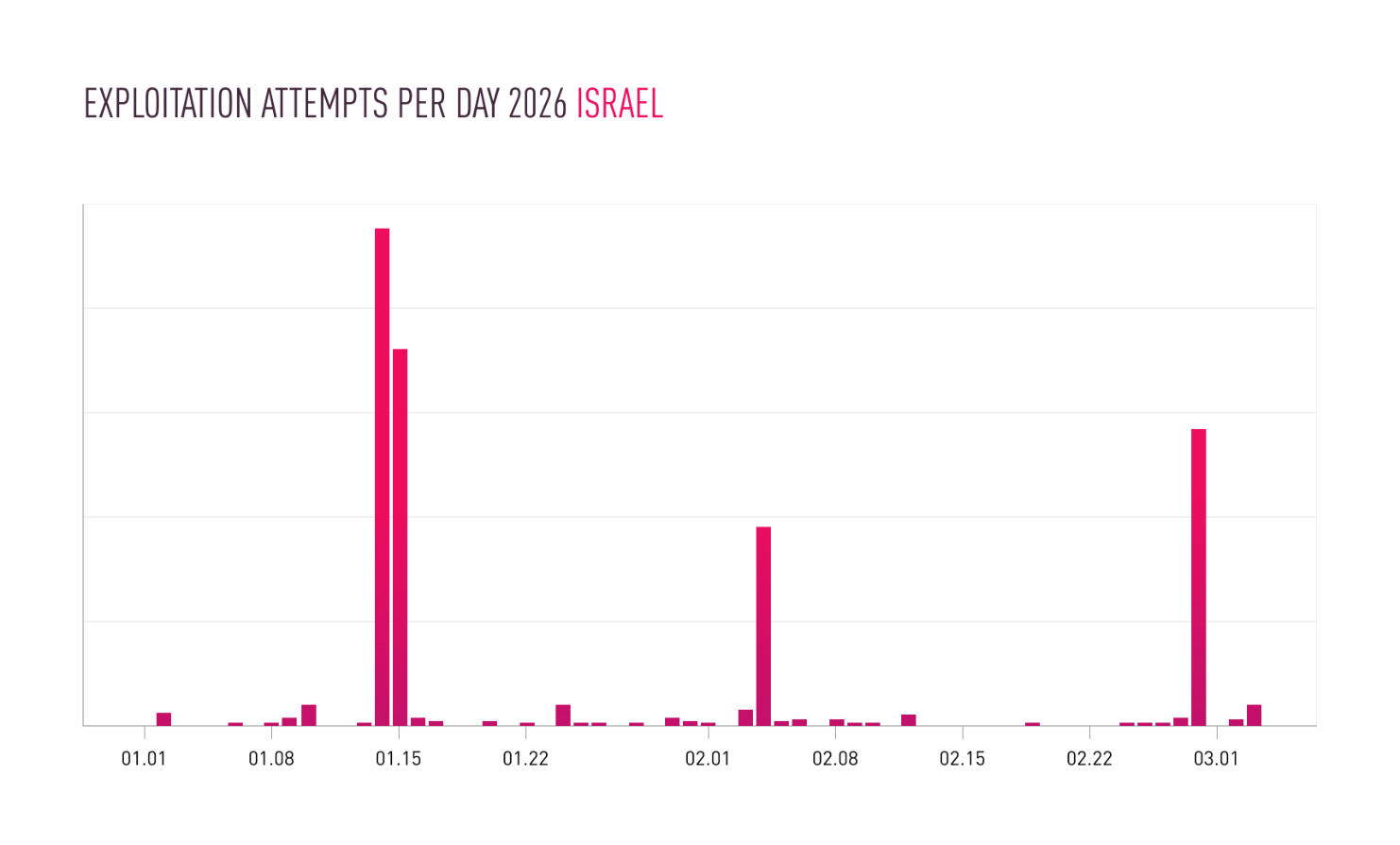
7️⃣ Iranian Campaign Targets IP Cameras Amid Middle‑East Conflict
Key Points:
- State‑linked actors exploit IoT cameras for reconnaissance and sabotage.
- Targeted devices integrate with kinetic operations on the ground.
- Recommendation to harden firmware and segment camera networks.
Description:
Checkpoint researchers observed an uptick in attacks against IP cameras in conflict zones, linking the activity to Iranian actors leveraging compromised video feeds for both intelligence gathering and coordinated physical attacks. The report underscores the strategic value of hardened IoT assets.
Why It Matters:
Compromised cameras can reveal troop movements and critical infrastructure status, directly influencing battlefield outcomes. Organizations must prioritize IoT security to prevent adversaries from turning surveillance tools into offensive weapons.
8️⃣ New Wi‑Fi Attack Bypasses WPA3 Handshake
Key Points:
- Novel handshake manipulation circumvents WPA3 authentication.
- Requires firmware updates on affected access points.
- Enterprise networks urged to patch immediately.
Description:
Bruce Schneier’s blog details a newly discovered attack that manipulates the WPA3 handshake, allowing attackers to derive session keys and intercept traffic. The vulnerability affects several popular access point models, prompting urgent vendor patches.
Why It Matters:
Wi‑Fi remains a primary vector for lateral movement; a WPA3 bypass reopens doors previously thought secured. Timely remediation is essential to maintain confidentiality and integrity of wireless communications.
9️⃣ Mid‑Market Platforms Deliver AI‑Powered SOC Capabilities

Key Points:
- AI-driven triage reduces alert fatigue for lean security teams.
- Risk scoring extends beyond CVSS to contextual impact.
- Cost‑effective solutions now feasible for mid‑size enterprises.
Description:
The Hacker News explores how emerging security platforms are finally providing AI‑enhanced investigation tools tailored for mid‑market organizations. These solutions move beyond traditional CVSS metrics, offering contextual risk assessments that align with limited staffing resources.
Why It Matters:
Mid‑market firms often lack deep security expertise; AI‑augmented platforms level the playing field, enabling faster, more accurate threat detection and response, thereby strengthening overall resilience.
🔟 Weekly Security Roundup Highlights Rising Ransomware & Supply‑Chain Threats
Key Points:
- Notable increase in ransomware targeting healthcare providers.
- Supply‑chain attacks exploit trusted software updates.
- Regulatory bodies released new guidance on incident reporting.
Description:
Malwarebytes’ weekly recap (Mar 2‑8) spotlights a surge in ransomware incidents, especially against medical facilities, as well as several high‑profile supply‑chain compromises. The summary also notes new policy recommendations from regulators aimed at improving breach disclosure practices.
Why It Matters:
Understanding current attack trends and compliance expectations helps organizations prioritize defenses, allocate resources effectively, and avoid costly regulatory penalties.
Stay vigilant and keep your defenses ahead of emerging threats.
Member discussion