Elevated Threat Landscape Forces Executives to Tighten Perimeter Controls and Supply‑Chain Resilience
Good morning, March 3, 2026 – here’s the latest cyber risk intel for leaders.
Today's headlines
- SonicWall firewalls probed through commercial proxy networks.
- SloppyLemming deploys dual malware chains against South Asian governments.
- Zero‑day in GoAnywhere MFT highlights limits of perimeter firewalls.
- CrowdStrike receives NCSC CIR certification for incident response.
- LummaStealer resurfaces alongside the CastleLoader droppers.
1️⃣ SonicWall Firewall Reconnaissance Exploits Proxy Networks
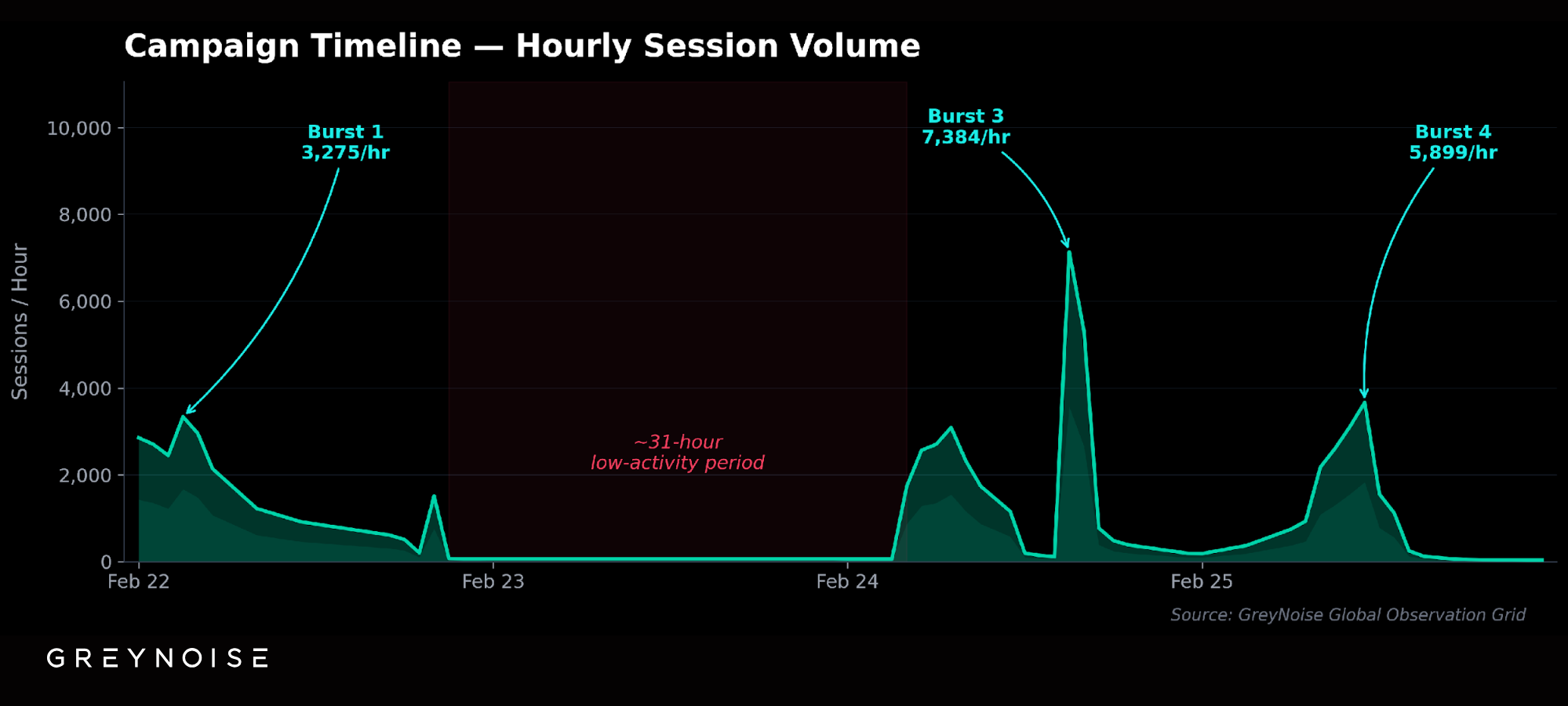
Key Points:
- Attackers leverage commercial open proxies to hide source IPs.
- Low‑and‑slow scanning evades typical IDS thresholds.
- Primary focus on SMBs with unsegmented SonicWall deployments.
- GreyNoise observed a rapid spike in proxy‑originated traffic.
- Recommendation: enforce strict outbound proxy filtering and monitor anomalous port scans.
Description:
GreyNoise reported an active reconnaissance campaign that systematically scans SonicWall firewalls via a chain of commercial proxy services. The operation spreads its scans across multiple IP ranges to avoid triggering rate‑based defenses, targeting primarily small and mid‑size organizations that rely on default SonicWall configurations.
Why It Matters:
The use of reputable proxy infrastructure masks attacker origins, making traditional IP‑based blocking ineffective. Organizations that depend on SonicWall devices must augment perimeter defenses with outbound proxy controls and behavioural analytics to detect the subtle scanning patterns before exploitation.
2️⃣ SloppyLemming Dual‑Chain Campaign Strikes South Asian Governments
Key Points:
- Two separate malware chains deliver BurrowShell and a Rust‑based keylogger.
- Targets include ministries, energy operators, and critical infrastructure in Pakistan and Bangladesh.
- Campaign spanned January 2025 to January 2026, showing sustained activity.
- Attribution to the SloppyLemming threat cluster by Arctic Wolf.
- Indicators suggest use of spear‑phishing attachments with weaponized macros.
Description:
The SloppyLemming group executed a coordinated set of attacks against governmental and critical infrastructure entities in Pakistan and Bangladesh. By chaining distinct payloads—BurrowShell for persistence and a custom Rust keylogger for credential capture—the actors achieved deep infiltration across multiple sectors over a year‑long period.
Why It Matters:
Dual‑chain architectures increase detection difficulty, as defenders must identify both the initial loader and secondary malicious components. Nations and enterprises in high‑risk regions should prioritize advanced endpoint detection, threat‑intel sharing, and rapid patching of macro‑related vulnerabilities.
3️⃣ GoAnywhere MFT Zero‑Day Undermines Perimeter Firewall Assumptions

Key Points:
- CVE‑2025‑10035 is a deserialization flaw in GoAnywhere MFT's License Servlet.
- Exploited by Storm‑1175 on September 11, 2025, achieving remote code execution.
- CVSS score of 10.0 underscores the criticality of the vulnerability.
- Perimeter firewalls failed to block the exploit as traffic originated from legitimate IPs.
- CISA recommends immediate patching and network segmentation for MFT servers.
Description:
Microsoft Threat Intelligence disclosed that the Storm‑1175 group leveraged CVE‑2025‑10035, a critical deserialization vulnerability in GoAnywhere Managed File Transfer's license servlet, to execute arbitrary code. The exploit bypassed traditional perimeter defenses by using legitimate application traffic, highlighting the risk of relying solely on firewalls.
Why It Matters:
High‑value data transfer solutions are prime targets for nation‑state actors. Organizations must adopt a defense‑in‑depth strategy, including timely patch management, micro‑segmentation of MFT environments, and application‑layer monitoring to detect anomalous behavior.
4️⃣ CrowdStrike Gains NCSC CIR Certification Boosting IR Credibility

Key Points:
- Certification verifies adherence to UK NCSC Incident Response standards.
- Demonstrates capability to handle high‑severity, multi‑jurisdictional incidents.
- Includes validated processes for evidence handling, escalation, and reporting.
- Positions CrowdStrike as a preferred partner for regulated sectors.
- May influence procurement decisions for enterprises seeking vetted IR services.
Description:
CrowdStrike announced it has achieved the National Cyber Security Centre's Certified Incident Response (CIR) assurance, confirming that its incident response methodology meets rigorous UK government standards. The certification process evaluated the firm's detection, containment, eradication, and post‑incident analysis procedures.
Why It Matters:
For enterprises operating in highly regulated environments, third‑party IR certification reduces due‑diligence overhead and ensures a trusted response capability. The accolade also signals to board members that incident response investments are aligned with global best practices.
5️⃣ LummaStealer Resurfaces Paired with CastleLoader Droppers
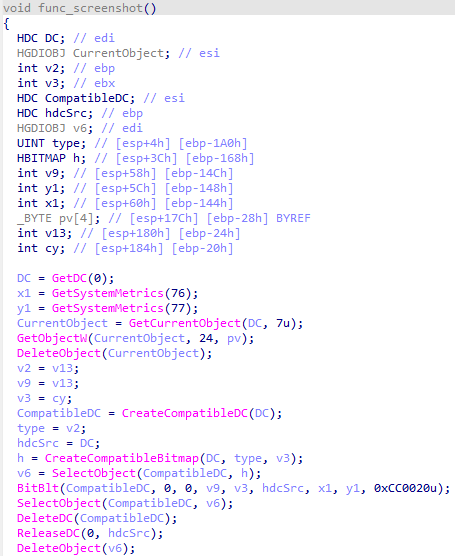
Key Points:
- LummaStealer now couples with CastleLoader to bypass initial‑access defenses.
- Malware mimics legitimate user behavior, increasing false‑positive rates.
- Distribution relies on malicious email attachments and compromised websites.
- Bitdefender published IoCs on GitHub for rapid detection.
- Emphasizes need for behavioral analytics alongside signature‑based tools.
Description:
Bitdefender researchers observed that the LummaStealer infostealer has re‑emerged, now leveraging the CastleLoader dropper to facilitate initial access. The combined payloads adopt sophisticated social engineering tactics, presenting as benign user actions to evade traditional detection mechanisms.
Why It Matters:
The evolution underscores the shifting landscape where credential‑stealing malware blends with legitimate activity patterns. Organizations should integrate user‑behavior analytics and continuously update detection signatures to mitigate the heightened risk.
6️⃣ Iranian Threat Actors Amplify Campaigns Amid Regional Tensions
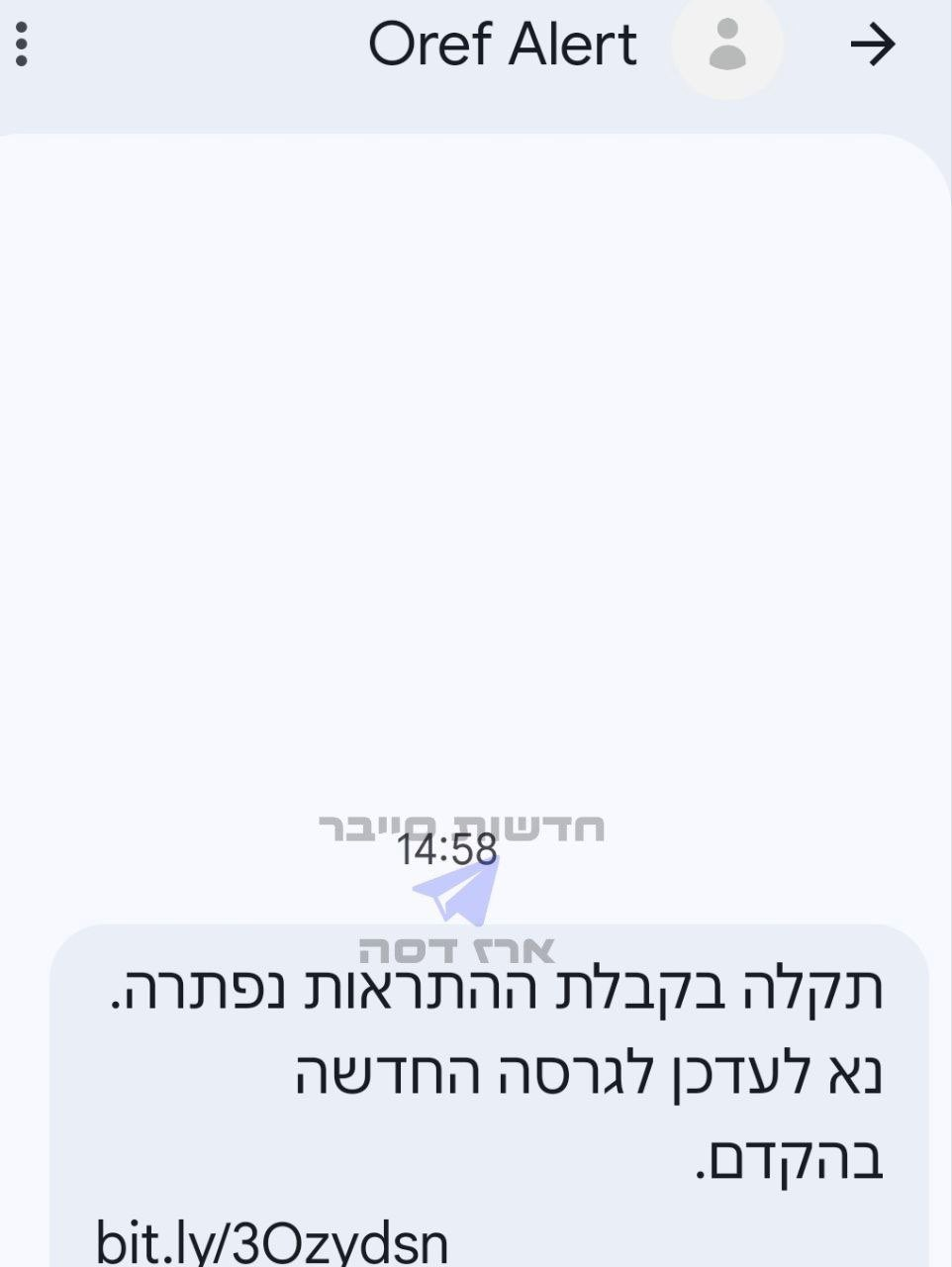
Key Points:
- Increase in phishing, ransomware, and data‑wiping operations linked to Iranian groups.
- Targets include energy, finance, and government sectors worldwide.
- Actors exploit geopolitical events to launch disinformation‑laden attacks.
- Recommendations include updating business continuity plans and rapid breach validation.
- Monitoring of Iranian threat feeds is advised for early warning.
Description:
Palo Alto Networks' Unit 42 threat brief details a surge in cyber activity attributed to Iranian state‑aligned actors throughout 2026. Campaigns feature sophisticated phishing, supply‑chain infiltration, and ransomware deployments, often timed with regional geopolitical developments.
Why It Matters:
The heightened activity raises the probability of collateral damage to multinational supply chains. Enterprises should reinforce incident response playbooks, validate threat intelligence continuously, and prepare for potential false‑flag claims that could impact reputation.
7️⃣ ScanBox Keylogger Deployed via APT‑TA423 Watering‑Hole Campaign

Key Points:
- APT‑TA423 compromised legitimate news sites to deliver ScanBox JavaScript.
- ScanBox collects system information and forwards to command‑and‑control servers.
- Victims include Australian NGOs and offshore energy firms in the South China Sea.
- Attack vector relies on trusted domain reputation to bypass security filters.
- Mitigation: block known ScanBox domains and enforce script‑allowlist policies.
Description:
ThreatPost reported that an advanced persistent threat group, identified as APT‑TA423, executed a watering‑hole campaign targeting news outlets. The compromised sites served the ScanBox reconnaissance tool, a JavaScript keylogger designed to harvest credentials and system details from unsuspecting visitors.
Why It Matters:
Watering‑hole attacks exploit the trust placed in legitimate domains, making traditional URL filtering insufficient. Organizations should implement strict content security policies, monitor outbound traffic for ScanBox signatures, and educate users about the risks of credential reuse across domains.
8️⃣ Samsung TV ACR Exploit Mitigated After Texas Consumer Action

Key Points:
- Automatic Content Recognition (ACR) feature was transmitting viewing data without consent.
- Texas Attorney General led a settlement requiring Samsung to provide disable instructions.
- Firmware update released to permanently block ACR data transmission.
- Privacy advocates warn similar smart‑TV telemetry could affect other manufacturers.
- Recommendation: audit IoT devices for hidden telemetry and enforce network segmentation.
Description:
Malwarebytes detailed Samsung's response to privacy concerns after it was discovered that Samsung Smart TVs were collecting viewing data via the Automatic Content Recognition feature. Following legal pressure in Texas, Samsung issued a firmware patch and a guide for consumers to disable ACR globally.
Why It Matters:
The incident highlights the broader risk of covert data collection by consumer IoT devices, which can be leveraged for profiling or espionage. Enterprises deploying smart TVs should assess telemetry settings, apply firmware updates promptly, and isolate such devices from sensitive networks.
9️⃣ Cloud Imperium Admits Data Breach Impacting Game Studios

Key Points:
- breach exposed internal source code and employee credentials.
- Approximately 1.2 million user accounts potentially affected.
- Company issued statement acknowledging the incident and launching forensic review.
- Industry reaction includes calls for stronger supply‑chain security in gaming.
- Recommended actions: force password resets and monitor for credential‑stuffing attempts.
Description:
The Register reported that Cloud Imperium, a British game development studio, quietly disclosed a data breach that compromised source code repositories and employee login details. The breach may have also exposed personal data for over a million players.
Why It Matters:
Compromise of development assets poses a risk of malicious code insertion into future game releases, threatening both brand reputation and player security. Studios must enforce zero‑trust principles, secure CI/CD pipelines, and regularly audit access controls.
🔟 Student Loan Database Leak Reveals 2.5 Million Personal Records

Key Points:
- Data leak includes names, Social Security numbers, and loan balances.
- Attackers accessed the database through a misconfigured AWS S3 bucket.
- Potential for identity theft and fraudulent loan applications.
- Federal agencies advised victims to monitor credit reports.
- Mitigation: enforce strict cloud storage permissions and conduct regular audits.
Description:
ThreatPost uncovered that a student loan servicing platform suffered a breach exposing the personal information of approximately 2.5 million borrowers. The attackers exploited a publicly accessible S3 bucket that lacked proper access controls, extracting sensitive data.
Why It Matters:
The breach underscores the criticality of cloud‑configuration hygiene for institutions handling financial data. Organizations must implement least‑privilege policies, continuous monitoring of cloud assets, and rapid incident response to mitigate fallout from large‑scale data exposures.
Stay vigilant and keep your defenses aligned with emerging threats.
Member discussion