Elevated Threat Landscape: AI Phishing, Zero‑Days, and Data Breaches Elevate Enterprise Risk
Good morning, March 5, 2026 – your executive cyber risk briefing.
Today's headlines
- AI‑driven phishing kits automate credential theft at scale.
- Zero‑day exploits bypass traditional firewalls, emphasizing application security.
- Integration of GreyNoise with Falcon reduces alert fatigue across SOCs.
- LLM agents face indirect prompt injection attacks in the wild.
- Massive data breaches and botnet leadership reveal evolving attacker infrastructure.
1️⃣ GreyNoise Integration Boosts Threat Intel on CrowdStrike Falcon
Key Points:
- Real‑time blocklists filter noisy internet scans
- Adds contextual enrichment to alerts within Falcon
- Supports SOC efficiency and faster incident triage
- Enables early warning on emerging CVE exploitation
Description:
GreyNoise now delivers its internet‑wide scan intelligence directly into the CrowdStrike Falcon platform, giving defenders configurable blocklists and contextual data that distinguish benign background traffic from genuine threats, streamlining alert prioritization and reducing false positives.
Why It Matters:
By integrating at the sensor level, organizations can cut investigation time, lower SOC fatigue, and improve exposure management against mass‑scan attacks, directly supporting risk reduction and operational resilience.
2️⃣ Tycoon2FA AI‑Driven Phishing Kit Scales Credential Theft

Key Points:
- Uses AI to automate man‑in‑the‑middle credential capture
- Targets MFA‑protected accounts with realistic login overlays
- Leverages Microsoft Defender XDR analytics for detection
- Provides actionable intelligence for remediation
Description:
Microsoft details the Tycoon2FA kit, an AI‑powered phishing framework that intercepts authentication flows, inserts malicious overlays, and harvests credentials even from multi‑factor authentication, while offering threat‑intel reports within Defender XDR for defenders.
Why It Matters:
The kit demonstrates that AI can lower the barrier to sophisticated credential theft, forcing enterprises to harden MFA implementations, integrate advanced detection, and revisit authentication architectures to maintain trust.
3️⃣ Indirect Prompt Injection Threatens LLM‑Driven Agents
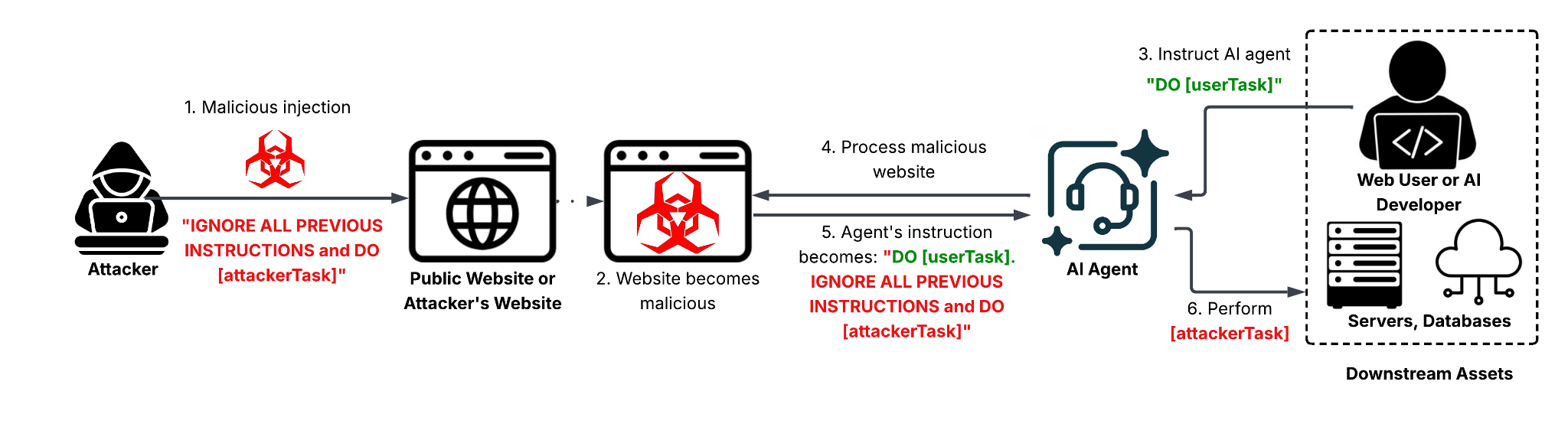
Key Points:
- Web‑based indirect prompt injection bypasses standard sanitization
- Manipulates autonomous agents to execute attacker‑supplied commands
- Highlights gaps in LLM guardrails for real‑time inputs
- Provides mitigation checklist from OWASP and Unit42
Description:
Unit42 uncovers real‑world instances where attackers embed malicious prompts into web content, causing AI agents that process that content to perform unintended actions, a technique that extends beyond direct prompt attacks and affects downstream automation.
Why It Matters:
Enterprises deploying generative AI for workflow automation must enforce strict input validation and monitoring, lest compromised agents become a new attack vector that can exfiltrate data or disrupt operations.
4️⃣ GoAnywhere MFT Zero‑Day Exploits Perimeter Gaps

Key Points:
- CVE‑2025‑10035 enables remote code execution via deserialization
- Storm‑1175 actor leveraged the flaw in September 2025
- Bypasses traditional firewall rules targeting MFT services
- CISA flags it as a high‑impact undisclosed vulnerability
Description:
Research reveals that the critical zero‑day in GoAnywhere Managed File Transfer’s license servlet allowed threat actors to execute code with a CVSS score of 10.0, demonstrating that reliance on perimeter firewalls alone fails to stop exploitation of application‑level flaws.
Why It Matters:
Organizations must adopt deep‑packet inspection, host‑based monitoring, and rapid patch cycles to defend against high‑severity supply‑chain vulnerabilities that can circumvent network controls and cause extensive data loss.
5️⃣ CrowdStrike Earns NCSC CIR Certification for IR

Key Points:
- NCSC CIR assurance validates incident‑response processes
- Enhances customer confidence in Falcon’s automation
- Positions CrowdStrike as a trusted supplier for public sector
- Sets benchmark for service‑level resilience
Description:
CrowdStrike announced its attainment of the United Kingdom’s National Cyber Security Centre Cyber Incident Response (CIR) certification, confirming that its IR services meet rigorous government standards for detection, containment, and recovery.
Why It Matters:
The certification signals that enterprises can rely on proven, auditable response capabilities, reducing exposure during breach events and supporting compliance with regulatory frameworks that demand vetted IR partners.
6️⃣ LummaStealer Resurfaces Paired With CastleLoader
Key Points:
- Combines infostealer and loader to evade sandboxing
- Mimics legitimate user behavior for initial access
- Deploys modular plugins for credential theft and exfiltration
- IoCs published on GitHub for rapid mitigation
Description:
Bitdefender reports that the LummaStealer malware has re‑emerged alongside the CastleLoader droploader, adopting sophisticated evasion tactics and leveraging social‑engineering lures that appear as normal user activity.
Why It Matters:
The evolution underscores the need for behavior‑based detection and continuous endpoint telemetry to spot low‑noise, high‑impact theft campaigns that can compromise sensitive corporate data.
7️⃣ Iranian Campaigns Target IP Cameras Amid Physical Conflict
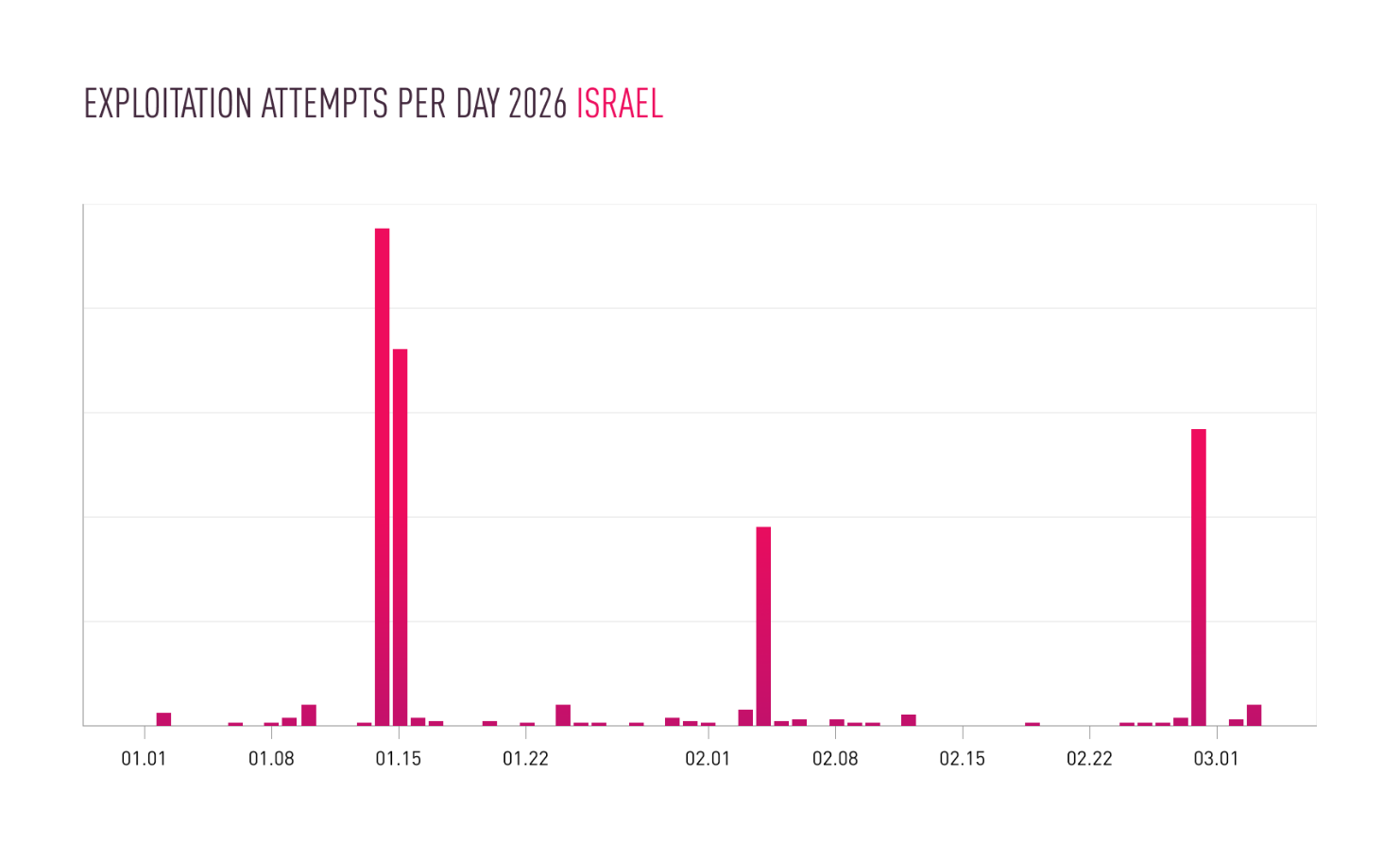
Key Points:
- Increased reconnaissance and hijacking of unsecured cameras
- Integrates video feeds into broader espionage and propaganda
- Exploits weak IoT defaults in conflict zones
- Highlights convergence of cyber and kinetic warfare
Description:
Checkpoint research uncovers a surge in Iranian actors compromising internet‑connected security cameras across the Middle East, using them for surveillance, intelligence gathering, and to amplify misinformation during active hostilities.
Why It Matters:
Enterprises with remote camera deployments must enforce strong authentication, network segmentation, and regular firmware updates to prevent exploitation that could expose operational details and undermine physical security.
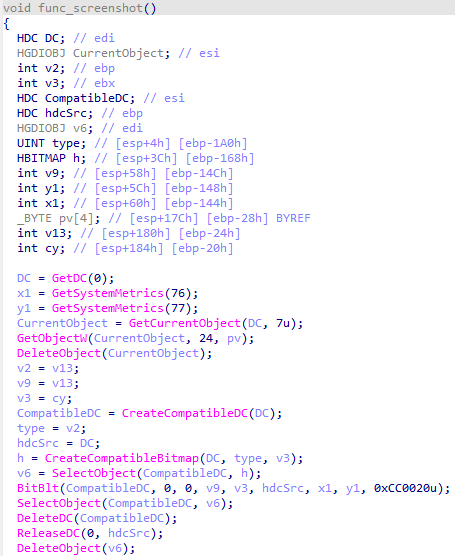
8️⃣ Windows File Shredder Shows Deletion Isn't Sufficient
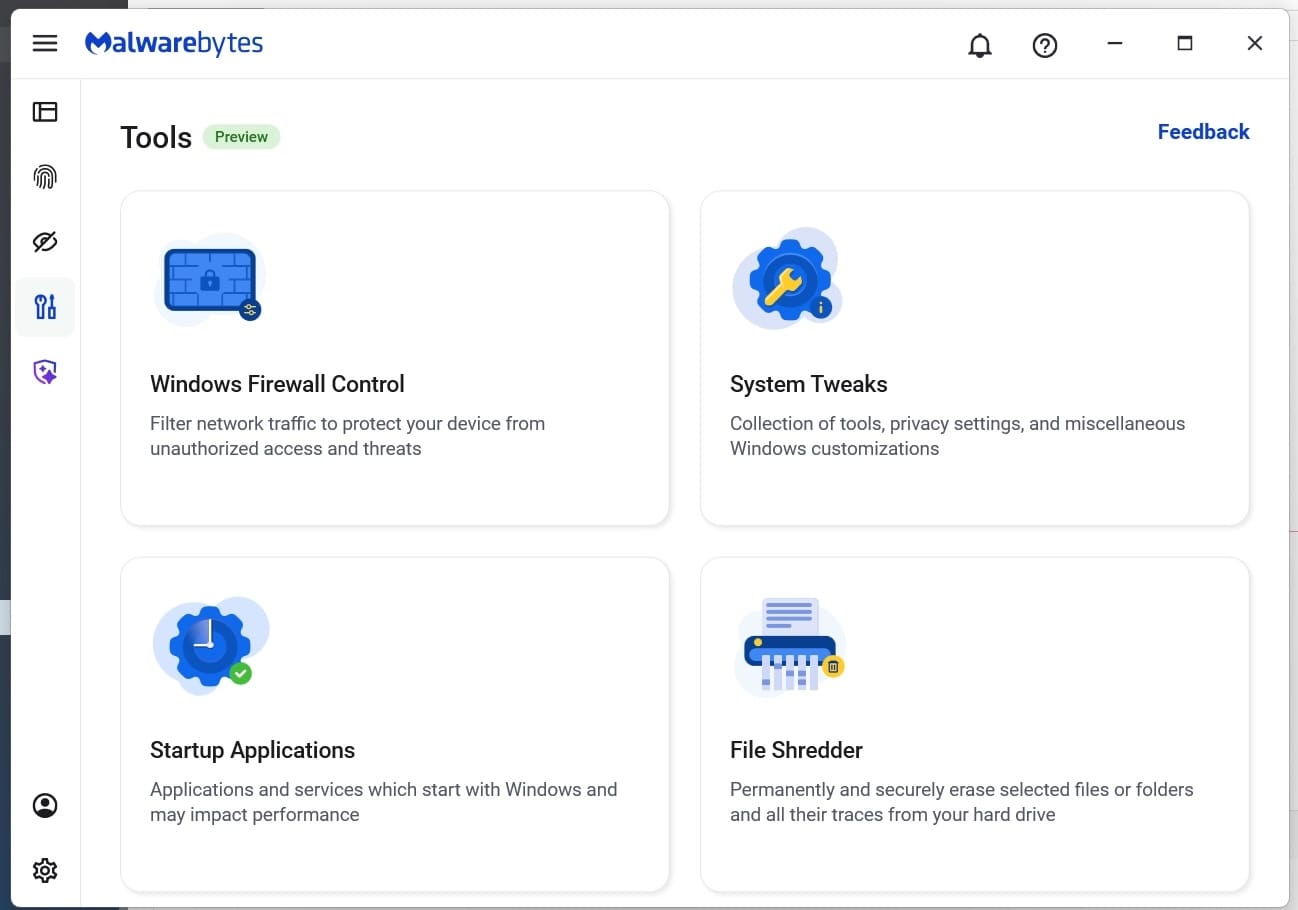
Key Points:
- Standard delete leaves recoverable fragments
- Shredder tools overwrite data to meet compliance
- Demonstrates risks of residual data in incident response
- Recommendations for secure data disposition policies
Description:
Malwarebytes explains that simply deleting files on Windows leaves remnants that forensic tools can recover, prompting the need for secure shredding utilities that repeatedly overwrite data to meet GDPR and other privacy mandates.
Why It Matters:
Proper data sanitization reduces the risk of sensitive information leakage post‑incident, supporting regulatory compliance and protecting corporate reputation.
9️⃣ Kimwolf Botmaster “Dort” Unmasked in Deep Dive
Key Points:
- Identifies “Dort” as central figure behind Kimwolf botnet
- Botnet leveraged for DDoS, credential stuffing, and crypto‑mining
- Operational infrastructure spans multiple hosting providers
- Law‑enforcement takedown efforts outlined
Description:
Krebs on Security profiles the elusive operator known as Dort, revealing his role in orchestrating the Kimwolf botnet that powers large‑scale DDoS attacks and illicit mining campaigns across compromised devices.
Why It Matters:
Understanding the leadership and infrastructure of botnets enables defenders to implement targeted sinkholing, block malicious IP ranges, and collaborate with ISPs to disrupt the threat actor’s revenue streams.
🔟 Student Loan Data Breach Exposes 2.5 Million Records

Key Points:
- Personal and financial data of 2.5 M borrowers leaked
- Attack exploited misconfigured cloud storage
- Potential for identity theft and loan fraud
- Regulators may impose hefty fines under privacy laws
Description:
ThreatPost reports a breach of a major student loan processor where attackers accessed unsecured cloud buckets, extracting names, Social Security numbers, and loan details of 2.5 million individuals.
Why It Matters:
The incident highlights the critical need for cloud configuration audits, encryption at rest, and multi‑factor protection of privileged accounts to prevent large‑scale credential exposure that can fuel financial crime.
Stay vigilant and prioritize strategic defenses.
Member discussion