Elevated Attack Surface Drives Urgent Need for Integrated Detection, Resilience, and Governance

Good morning, March 23, 2026 – here’s today’s critical security intel.
Today's headlines
- GreyNoise integrates real‑time blocklists into Google SecOps to cut noise.
- Microsoft flags a massive IRS phishing campaign compromising 29,000 users.
- Interlock ransomware targets enterprise firewalls, leveraging novel C2 domains.
- Iran‑backed actors claim wiper attack on Medtech firm Stryker.
- Student loan provider breach exposes 2.5 million personal records.
1️⃣ GreyNoise bolsters Google SecOps with real‑time blocklists
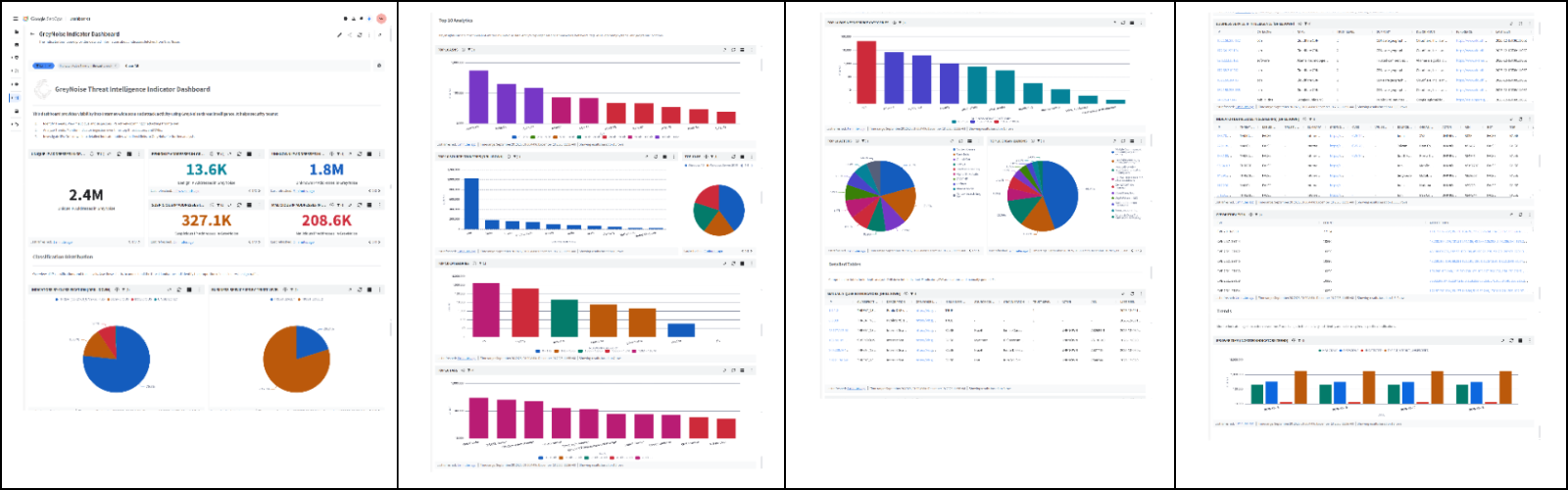
Key Points:
- Instant blocking of malicious IPs via configurable blocklists.
- Reduces false‑positive alerts from internet scanners.
- Enables faster threat‑hunting and incident context enrichment.
- Seamless integration with Google Cloud SIEM and SOAR platforms.
Description:
GreyNoise announced new integrations that feed fully configurable, real‑time blocklists directly into Google SecOps. The capability lets security teams immediately block malicious traffic, filter out noisy background scans, and enrich investigations with IP reputation data, improving SOC efficiency for organizations of any size.
Why It Matters:
By eliminating low‑value alerts and automating blocklist updates, enterprises can focus scarce analyst time on genuine threats, accelerating response cycles and lowering the risk of breach escalation. The integration also strengthens the security posture of Google Cloud customers, a key consideration for C‑suite risk managers.
2️⃣ Microsoft warns of IRS phishing hitting 29,000 users

Key Points:
- Phishing emails impersonating the IRS reached over 29,000 victims.
- Malware delivered through unauthorized remote‑management tools (RMM).
- Payload capable of credential theft and lateral movement.
- Microsoft urges audits for rogue RMM services and MFA enforcement.
Description:
Microsoft’s security team disclosed a large‑scale phishing campaign that spoofed the Internal Revenue Service, tricking recipients into downloading a malicious RMM payload. The campaign compromised roughly 29,000 users, installing malware that harvested credentials and opened pathways for further intrusion across corporate networks.
Why It Matters:
Financial institutions and any organization handling sensitive taxpayer data face heightened regulatory exposure. Prompt detection of unauthorized RMM activity and mandatory multi‑factor authentication are essential controls to prevent credential‑based lateral attacks and protect compliance posture.
3️⃣ OWASP retires its Meetup platform
Key Points:
- Official shutdown of the OWASP Meetup community site.
- Transition to new collaboration channels announced.
- Continued focus on open‑source security standards and education.
- Call for community participation in alternative forums.
Description:
The OWASP Foundation announced the retirement of its long‑standing Meetup platform, citing the need to consolidate community engagement into more modern communication tools. The organization will shift discussions to platforms such as Discord and GitHub Discussions while maintaining its mission to promote secure software development.
Why It Matters:
OWASP’s guidance underpins many enterprise security programs. Maintaining an active, accessible community ensures rapid dissemination of vulnerability intelligence and best‑practice updates, which are critical for maintaining compliance and mitigating emerging threats.
4️⃣ Malwarebytes weekly roundup highlights emerging malware trends
Key Points:
- Spike in credential‑stealing malware targeting remote workers.
- New variants of trojanized browsers observed.
- Comparative analysis of endpoint solutions’ detection rates.
- Recommendations for layered anti‑malware defenses.
Description:
Malwarebytes released its weekly security summary covering March 16‑22, noting a rise in credential‑stealing tools aimed at remote work environments and the appearance of modified browser payloads. The report also compared detection effectiveness across leading endpoint products, offering actionable guidance for hardening endpoints.
Why It Matters:
Enterprises with distributed workforces must adapt defenses to the evolving threat landscape. Understanding gaps in current endpoint products helps security leaders prioritize investments and reinforce breach‑prevention controls.
5️⃣ Iran‑backed hackers claim wiper attack on Stryker
Key Points:
- Wiper malware allegedly deployed against Medtech leader Stryker.
- Targeted disruption of medical device operations.
- Geopolitical motive linked to regional tensions.
- Calls for improved segmentation and backup verification.
Description:
KrebsOnSecurity reported that a group identified as Iran‑backed has claimed responsibility for a wiper malware campaign against Stryker, a major medical‑technology company. The attack aimed to erase critical data on manufacturing and device management systems, potentially jeopardizing patient safety.
Why It Matters:
Healthcare providers and their suppliers face heightened risk from nation‑state actors seeking strategic disruption. Robust network segmentation, immutable backups, and incident‑response readiness are vital to protect life‑critical operations and maintain regulatory compliance.
6️⃣ Amazon uncovers Interlock ransomware targeting firewalls
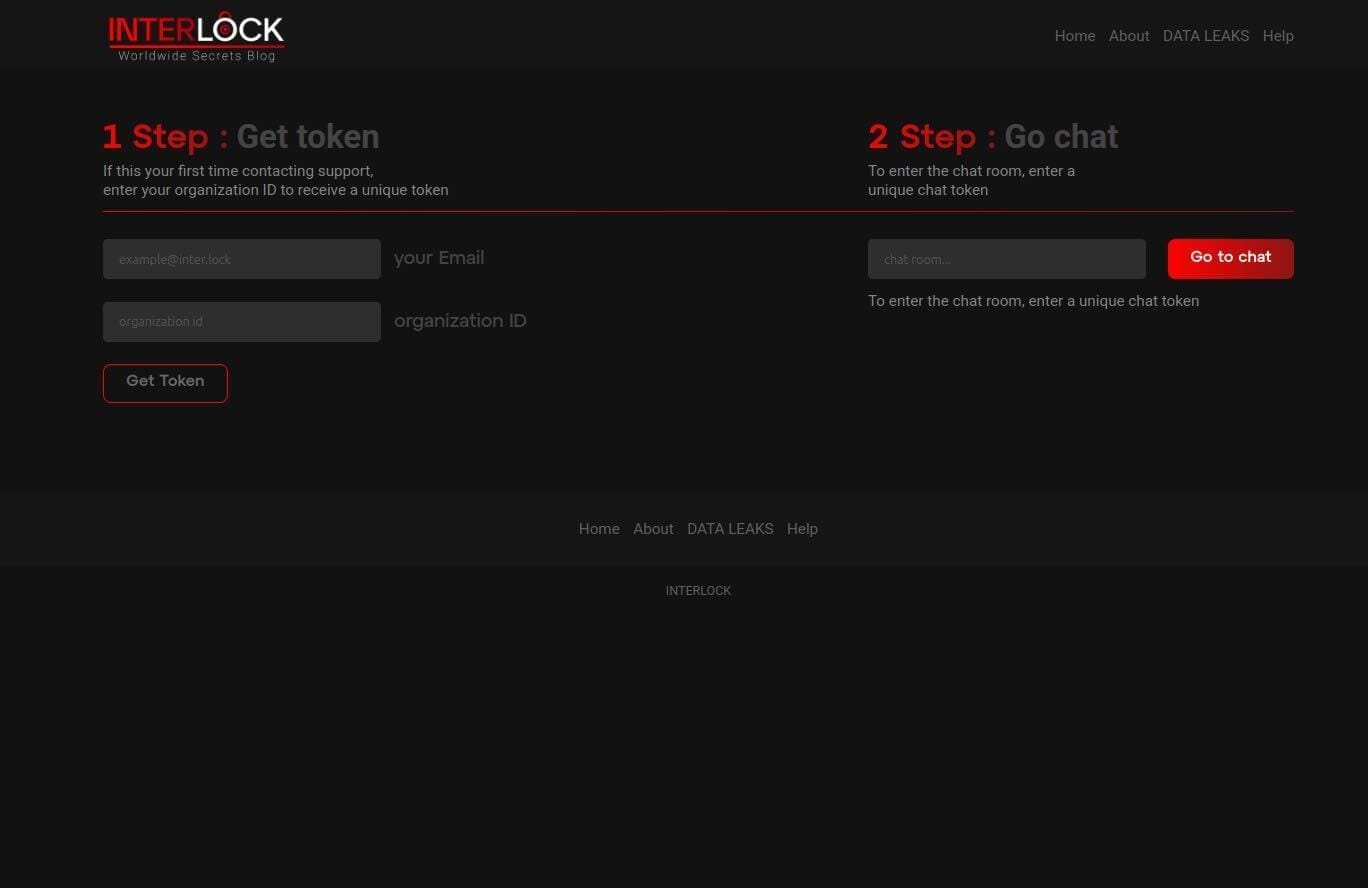
Key Points:
- Interlock ransomware exploits misconfigured enterprise firewalls.
- Campaign utilizes multiple C2 domains observed March 2026.
- Payload encrypts critical data and demands cryptocurrency ransom.
- Recommendations include patching, strict firewall rules, and network monitoring.
Description:
AWS security researchers identified the Interlock ransomware campaign, which specifically scans for and compromises inadequately secured enterprise firewalls. The operation employs a set of active C2 domains and delivers encryption payloads that halt business operations, followed by ransom demands.
Why It Matters:
Compromised firewalls provide attackers with persistent network footholds, amplifying impact across the attack chain. Timely patching and hardened firewall configurations are essential to mitigate ransomware risk and preserve business continuity.
7️⃣ Student loan breach exposes 2.5 M records

Key Points:
- Data breach at major student‑loan servicer reveals 2.5 million records.
- Exposed information includes SSNs, DOBs, and loan details.
- Incident attributed to a misconfigured cloud storage bucket.
- Advisories recommend monitoring for identity theft and tightening cloud configs.
Description:
ThreatPost detailed a breach affecting a large student‑loan provider, where an improperly secured cloud storage bucket leaked personal and financial data of approximately 2.5 million borrowers. The compromise stemmed from inadequate access controls on the storage service.
Why It Matters:
The breach elevates identity‑theft risk for millions of borrowers and triggers regulatory scrutiny under data‑protection statutes. Organizations must enforce strict cloud‑access governance and conduct continuous configuration audits to avoid similar exposures.
8️⃣ VirusTotal blog warns of AI‑driven automation to infection
Key Points:
- Demonstrates reverse shells and semantic worms generated by AI agents.
- Introduces cognitive rootkits capable of evading behavioral analytics.
- Highlights need for AI‑aware detection strategies.
- Suggests integration of AI behavior baselines into security tooling.
Description:
VirusTotal’s research blog released Part II of a series on how automation can evolve into sophisticated infection techniques. The write‑up showcases AI‑generated reverse shells, semantic worms, and cognitive rootkits that adapt to defensive measures, underscoring a new class of intelligent malware.
Why It Matters:
Security teams must anticipate adversaries leveraging AI to craft adaptive threats that bypass traditional signatures. Embedding AI behavior analytics into detection pipelines is crucial for early identification of these emerging attack vectors.
9️⃣ ISC Stormcast podcast discusses surge in SSH/Telnet scanning
Key Points:
- Observes increased scanning of SSH and Telnet ports across IPv4 space.
- Links activity to credential‑stuffing and botnet reconnaissance.
- Provides mitigation tactics such as rate‑limiting and key‑based auth.
- Notes correlation with recent ransomware campaigns.
Description:
The Internet Storm Center’s Stormcast episode for March 23 highlighted a notable rise in unsolicited SSH and Telnet scanning, driven by automated bots seeking weak credentials. The discussion connected this activity to the early stages of ransomware infection chains and offered defensive recommendations.
Why It Matters:
Unsecured remote‑login services remain a low‑hanging fruit for attackers. Implementing strict access controls and monitoring can thwart initial footholds, reducing the likelihood of ransomware proliferation within enterprise networks.
🔟 Smashing Security exposes CEO Apple ID deep‑fake scam

Key Points:
- Sophisticated social‑engineering campaign used AI‑generated voice to hijack Apple ID.
- Targeted a technology CEO, compromising personal and corporate accounts.
- MFA bypass achieved through credential‑replay and SIM‑swap tactics.
- Emphasizes need for hardware‑based security keys and user training.
Description:
Smashing Security reported a near‑successful scam that leveraged a deep‑fake voice to convince a tech CEO to surrender Apple ID credentials. The attackers combined AI‑generated audio with a SIM‑swap to bypass two‑factor authentication, highlighting the evolving threat of AI‑aided social engineering.
Why It Matters:
Executive accounts are high‑value targets; their compromise can lead to supply‑chain attacks and data exfiltration. Deploying hardware security keys and educating leaders on deep‑fake detection are critical steps to safeguard privileged identities.
Stay vigilant and keep your defenses resilient.

Member discussion