Elevated AI‑Driven Threat Landscape Demands Strategic Risk Controls and Resilience
Hello, March 8 2026 – here are today’s top cyber and AI threat intelligence highlights.
Today's headlines
- GreyNoise intelligence now embedded in CrowdStrike Falcon for real‑time threat blocking.
- OpenAI’s Codex Security AI uncovers over ten thousand high‑severity code flaws.
- GoAnywhere MFT zero‑day exploit exposes limits of perimeter‑only defenses.
- Anthropic’s Claude model discovers 22 new Firefox vulnerabilities.
- State‑backed actors leverage AI agents to automate attack infrastructure.
1️⃣ GreyNoise Intelligence Now Integrated into CrowdStrike Falcon Platform
Key Points:
- Real‑time, fully configurable blocklists block malicious IPs instantly.
- Compromised asset detection alerts when assets contact hostile hosts.
- Vulnerability prioritization ties exploitation trends to CVE risk scores.
- SOC efficiency improves by filtering noisy internet‑scanner traffic.
- Enriched threat hunting with contextual data accelerates investigations.
Description:
GreyNoise announced that its threat‑intelligence services are now natively available within the CrowdStrike Falcon platform, providing customers with automated blocklists, compromised asset detection, and vulnerability insights directly at the endpoint and cloud levels.
Why It Matters:
By embedding GreyNoise, organizations can reduce false positives, speed up incident response, and enhance proactive defenses—critical for reducing exposure in increasingly noisy threat environments, especially for midsize enterprises lacking extensive SOC resources.
2️⃣ OpenAI Codex Security Scans 1.2 M Commits, Flags 10,561 Critical Flaws

Key Points:
- AI‑powered Codex agent analyzes 1.2 million code commits.
- Identifies 10,561 high‑severity vulnerabilities missed by traditional tools.
- Available in research preview for ChatGPT Pro, Enterprise, Business, and Edu.
- Provides fix suggestions to reduce developer noise.
- Free usage for the first month to encourage broad adoption.
Description:
OpenAI introduced Codex Security, an AI‑driven assistant that scans code repositories to detect, validate, and propose remediation for complex vulnerabilities, offering the service as a free one‑month preview to eligible ChatGPT customers.
Why It Matters:
The tool promises to elevate software security hygiene across development pipelines, helping organizations remediate critical bugs faster and lowering the risk of supply‑chain attacks that exploit software flaws.
3️⃣ GoAnywhere MFT Zero‑Day Exploited, Highlighting Firewall Limits

Key Points:
- Storm‑1175 leveraged CVE‑2025‑10035, a deserialization flaw with CVSS 10.0.
- Attack bypassed traditional perimeter firewalls to compromise file transfers.
- CISA warns such high‑impact vulnerabilities may be weaponized for months.
- Demonstrates need for application‑layer monitoring and zero‑trust controls.
- Incident caused significant data exfiltration across multiple enterprises.
Description:
Research revealed that the GoAnywhere Managed File Transfer (MFT) product was exploited via a critical zero‑day vulnerability, allowing attackers to execute arbitrary code and evade perimeter defenses, underscoring gaps in traditional firewall‑centric security models.
Why It Matters:
Enterprises must adopt deeper inspection, micro‑segmentation, and continuous vulnerability monitoring to protect critical data movement services against sophisticated, stealthy exploits.
4️⃣ Anthropic’s Claude Opus 4.6 Uncovers 22 Firefox Bugs

Key Points:
- AI model identified 22 new security issues in Firefox, 14 high severity.
- Vulnerabilities span memory corruption, sandbox escape, and privacy leaks.
- All findings were patched in Firefox 148 released in January 2026.
- Demonstrates AI’s growing role in rapid vulnerability discovery.
- Collaboration between Anthropic and Mozilla accelerates remediation.
Description:
Anthropic leveraged its Claude Opus 4.6 large language model to discover 22 previously unknown vulnerabilities in the Firefox browser, prompting a swift patch rollout by Mozilla.
Why It Matters:
The success showcases how generative AI can augment traditional security testing, enabling faster identification and mitigation of flaws that could otherwise be exploited at scale.
5️⃣ LummaStealer Resurfaces Paired with CastleLoader Malware
Key Points:
- LummaStealer now distributed alongside CastleLoader, a new loader platform.
- Malware mimics legitimate user behavior to evade behavior‑based detections.
- Comprehensive IoC list published on GitHub for rapid hunting.
- Highlights evolution of infostealer tactics toward multi‑stage infection.
- Emphasizes need for context‑aware monitoring of credential‑related activity.
Description:
Bitdefender researchers observed that the LummaStealer infostealer has been revived and is being delivered together with the CastleLoader framework, employing sophisticated social‑engineering and stealth techniques to exfiltrate credentials.
Why It Matters:
Security teams must adapt detection strategies to identify low‑and‑slow credential theft that blends with normal user actions, reinforcing the importance of endpoint behavior analytics.
6️⃣ AI Agents Accelerate Attack Infrastructure for State Actors

Key Points:
- Large language models automate script generation for reconnaissance and exploitation.
- North Korean groups reported using AI agents to manage botnets.
- Reduces required skill level for setting up sophisticated attack pipelines.
- AI‑driven tooling speeds up credential dumping, phishing payload creation.
- Raises concern over rapid scaling of cyber‑espionage campaigns.
Description:
A recent analysis details how threat actors, including North Korean groups, are employing AI agents to handle repetitive, labor‑intensive tasks in their attack lifecycle, from infrastructure deployment to payload customization.
Why It Matters:
The democratization of advanced tooling expands the threat surface, compelling defenders to prioritize AI‑specific detection capabilities and harden supply‑chain processes.
7️⃣ Falcon Next‑Gen SIEM Introduces Sensor‑Native Log Collection
Key Points:
- Sensors collect logs directly from endpoints, eliminating manual agent setup.
- Streamlines onboarding process, cutting deployment time by up to 70%.
- Provides unified visibility across cloud and on‑prem environments.
- Enhances real‑time threat detection with enriched context.
- Supports integration with existing SOAR and analytics tools.
Description:
CrowdStrike unveiled a new capability in its Falcon Next‑Gen SIEM that enables sensor‑native log collection, simplifying the onboarding experience for security teams and delivering immediate visibility into endpoint activity.
Why It Matters:
Faster deployment translates to quicker threat detection and response, allowing organizations to maintain continuous monitoring without the overhead of traditional log‑forwarding agents.
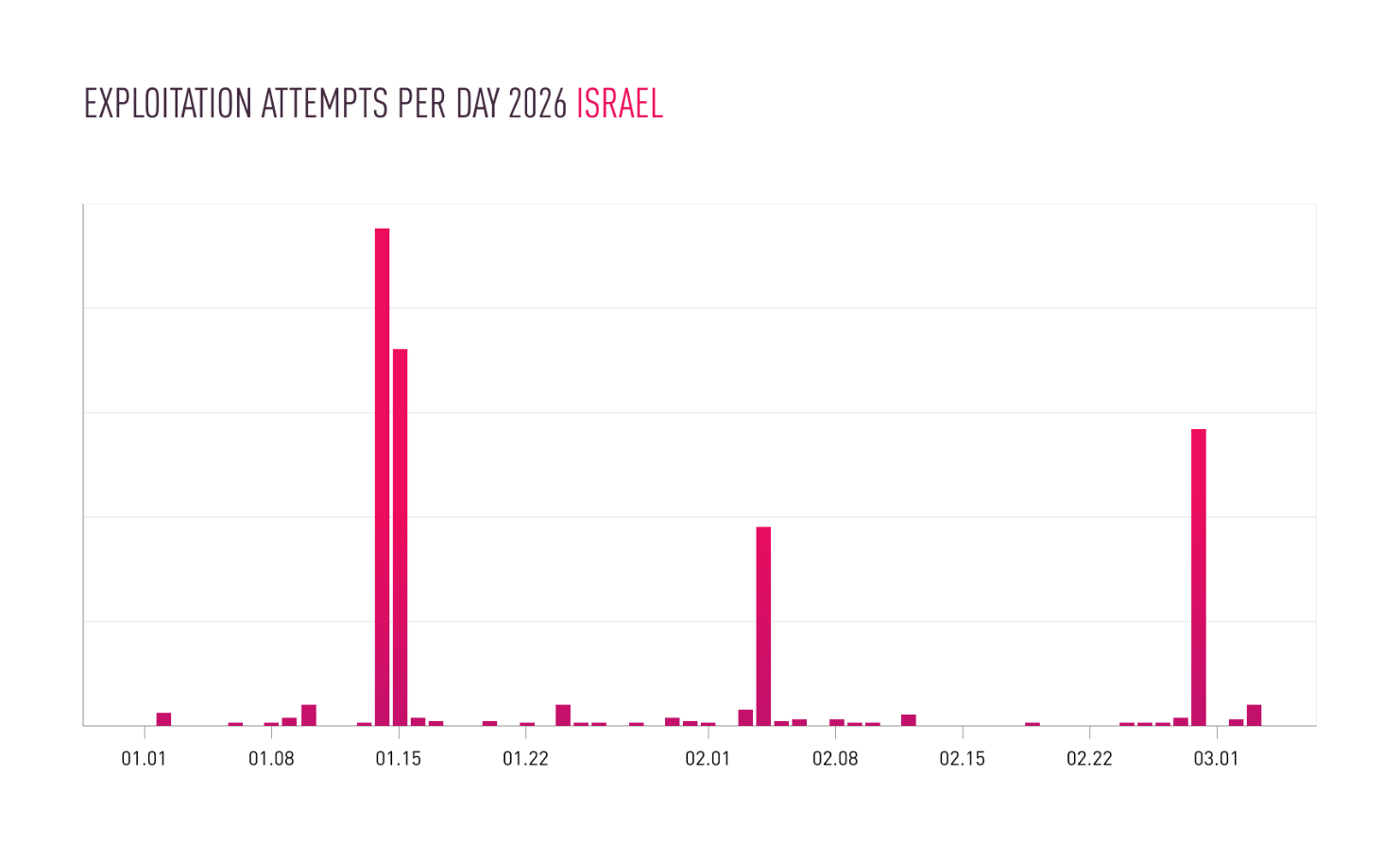
8️⃣ Iranian Campaign Exploits IP Cameras Amid Middle‑East Conflict
Key Points:
- Increase in attacks on IP cameras coinciding with regional military operations.
- Threat actors leverage default credentials and outdated firmware.
- Compromised cameras used for surveillance and as footholds for lateral movement.
- Highlights convergence of physical warfare and cyber targeting of IoT.
- Recommendations include network segmentation and regular firmware updates.
Description:
Check Point research identified a surge in Iranian‑linked attacks against IP cameras in the Middle East, leveraging insecure devices to gather intelligence and support kinetic operations.
Why It Matters:
The campaign underscores the strategic risk posed by unsecured IoT devices in conflict zones, urging organizations to enforce robust IoT security controls to prevent espionage and sabotage.
9️⃣ ScanBox JavaScript Keylogger Deployed via Watering‑Hole Campaigns

Key Points:
- APT TA423 used compromised Australian news sites as bait.
- Injected ScanBox JavaScript collects keystrokes and system info.
- Targets include energy firms and other critical infrastructure operators.
- Tool enables stealthy reconnaissance before delivering ransomware.
- Mitigation advises strict content‑security policies and web filtering.
Description:
ThreatPost reported that the China‑based APT group TA423 conducted watering‑hole attacks, embedding the ScanBox JavaScript keylogger into popular news websites to harvest credentials from visitors.
Why It Matters:
The incident highlights the persistent threat of supply‑chain compromises and the need for rigorous web‑traffic inspection to safeguard high‑value sectors.
🔟 Fake Google Meet Update Grants Attackers PC Control
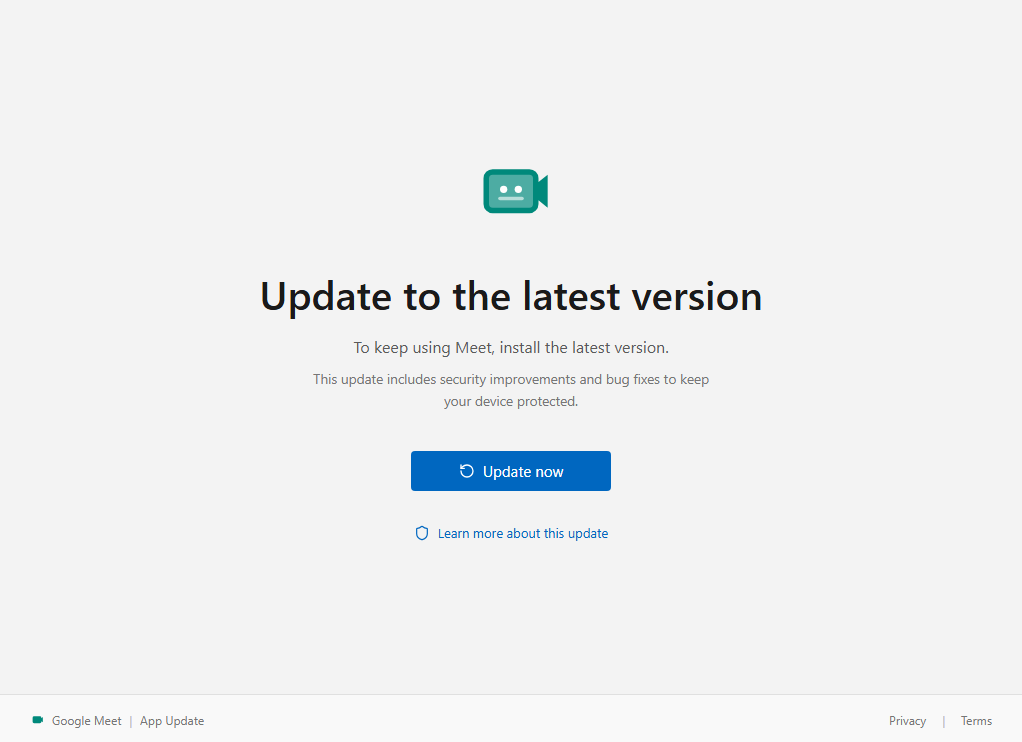
Key Points:
- Malicious installer mimics Google Meet update prompt.
- One‑click execution installs remote access trojan on Windows machines.
- Campaign distributed via phishing emails and compromised software bundles.
- Rapid spread due to brand trust and lack of user awareness.
- Recommendations include verifying update sources and employing application whitelisting.
Description:
Malwarebytes uncovered a campaign where attackers disguise a remote‑access payload as a Google Meet update, tricking users into granting full control over their computers.
Why It Matters:
The scheme exploits brand trust to achieve footholds, emphasizing the importance of user education and strict update verification to prevent credential theft and data exfiltration.
Stay vigilant and integrate AI‑enhanced defenses to protect your organization.
Member discussion