Critical RCE Exploits and AI‑Driven Fraud Threaten Enterprise Resilience 🚨. Elevate Detection and Trust Now 🔐
Good morning, February 16, 2026 – here are the top threats shaping your security agenda.
Today's headlines
- BeyondTrust RCE reconnaissance signals emerging privileged‑access risk
- Amaranth‑Dragon leverages new CVE for Southeast Asian espionage
- QR code phishing surges across mobile and web channels
- Romanian pipeline attack underscores OT vulnerability
- Lithuania launches AI‑driven anti‑fraud national initiative
1️⃣ BeyondTrust RCE Reconnaissance Signals Emerging Exploit Risk
Key Points:
- GreyNoise observed a sharp increase in scanning activity targeting BeyondTrust services
- CVE‑2026‑1731 enables unauthenticated remote code execution on privileged access management consoles
- Malicious IP clusters align with known exploit‑as‑a‑service operators
- Early detection allows organizations to prioritize patching before public exploitation
Description:
GreyNoise researchers reported that threat actors have begun active reconnaissance for the newly disclosed BeyondTrust remote code execution vulnerability (CVE‑2026‑1731). The scans focus on default ports and known deployment patterns, indicating preparation for widescale exploitation of privileged‑access tools that manage critical credentials across enterprises.
Why It Matters:
Compromise of BeyondTrust could give attackers unfettered access to privileged accounts, amplifying the impact of any breach. Early awareness enables security teams to enforce compensating controls, segment vulnerable assets, and accelerate patch deployment, reducing the window of opportunity for exploitation.
2️⃣ Amaranth‑Dragon Weaponizes CVE‑2025‑8088 for Targeted Espionage
Key Points:
- APT‑41 affiliated group Amaranth‑Dragon exploits CVE‑2025‑8088 in Microsoft Exchange
- Operation focuses on government agencies and telecom providers in Southeast Asia
- Zero‑day usage enables stealthy credential harvesting and lateral movement
- Campaign integrates custom malware with native Windows tools for persistence
Description:
Check Point research uncovered that the state‑linked group Amaranth‑Dragon is actively leveraging the recently disclosed CVE‑2025‑8088 vulnerability to infiltrate networks in Southeast Asia. By chaining the exploit with credential dumping tools, the actors achieve deep footholds within high‑value targets, facilitating long‑term espionage operations.
Why It Matters:
The exploitation of a fresh Microsoft vulnerability underscores the urgency for rapid patching and robust email gateway defenses. Organizations in the region must reassess their threat models, implement extended detection and response (XDR) capabilities, and monitor for the specific Indicators of Compromise (IOCs) associated with this campaign.
3️⃣ QR Code Phishing Expands Attack Surface on Mobile and Web
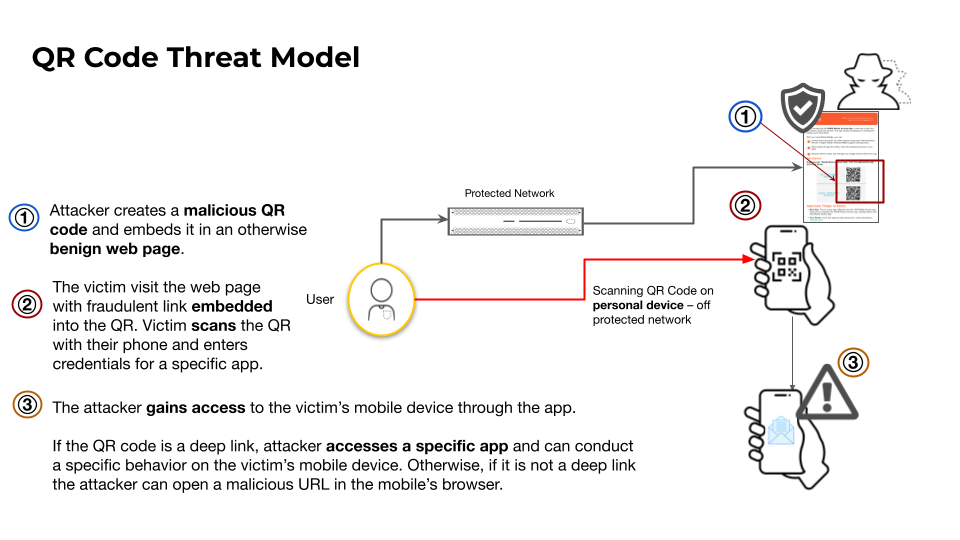
Key Points:
- Malicious QR codes redirect users to credential‑stealing landing pages
- Attack vectors include printed media, social media posts, and public displays
- Traditional email filters miss QR‑based threats, requiring specialized scanning
- Palo Alto Unit 42 observed a 42 % increase in QR‑driven phishing attempts YoY
Description:
Unit 42 detailed a growing trend where threat actors embed malicious URLs in QR codes to bypass conventional security controls. Victims scan the codes with mobile devices, unwittingly loading phishing sites that harvest credentials or deliver malware payloads, often leveraging deep‑linking techniques to exploit app vulnerabilities.
Why It Matters:
The proliferation of QR‑based phishing challenges existing security stacks that focus on email and URL filtering. Organizations should deploy QR‑code inspection tools, educate users about safe scanning practices, and incorporate QR‑related indicators into threat‑intel feeds to mitigate this emerging vector.
4️⃣ Romanian Oil Pipeline Operator Disrupted by Cyberattack

Key Points:
- Conpet's IT systems were disabled, taking its public website offline
- Preliminary analysis suggests ransomware or sabotage targeting OT networks
- Critical infrastructure interruption highlights gaps in segmentation and monitoring
- Incident prompted national cybersecurity authority to issue emergency advisories
Description:
The 9 February Threat Intelligence Report from Check Point highlighted a cyber incident against Conpet, Romania’s national oil pipeline operator. Attackers compromised corporate IT assets, leading to a complete service outage and raising concerns about potential spill‑over into operational technology (OT) environments.
Why It Matters:
Infrastructure operators must treat OT environments as high‑value targets and enforce strict network segmentation, continuous monitoring, and incident‑response readiness. The event serves as a reminder that ransomware groups are increasingly probing for pathways into critical services.
5️⃣ Lithuania Rolls Out AI‑Driven Anti‑Fraud Initiative

Key Points:
- Government‑funded program targets AI‑generated cyber fraud across e‑services
- Focus areas include e‑signatures, digital health records, and online banking
- Collaboration between regulators, academia, and private sector firms
- Pilot deployments of AI analytics aim to detect deep‑fake scams in real time
Description:
Lithuania has launched a nationwide effort to combat AI‑enhanced cyber fraud, recognizing that deep‑fake and synthetic media are increasingly used to deceive citizens and compromise digital services. The initiative combines regulatory frameworks with advanced AI detection tools to safeguard e‑government platforms.
Why It Matters:
The rise of AI‑powered fraud mandates proactive defenses that combine technology, policy, and education. Lithuania’s approach illustrates how early investment in AI detection can preserve trust in digital public services and reduce financial loss.
6️⃣ Weekly Recap: Outlook Add‑Ins Hijack, Wormable Botnet, AI‑Generated Malware

Key Points:
- Compromised Outlook add‑ins used to deliver credential‑stealing malware
- New wormable botnet targeting unpatched IoT devices resurfaces
- Zero‑day patches released for three critical CVEs in major platforms
- AI‑assisted malware evades traditional signature detection
- Threat actors blend legacy exploits with modern cloud abuse techniques
Description:
The weekly recap from The Hacker News outlines a mixed landscape where old‑school botnet tactics intersect with AI‑enhanced malware and supply‑chain abuse. Notable incidents include malicious Outlook add‑ins that hijack email flows and a wormable botnet exploiting IoT firmware weaknesses.
Why It Matters:
Enterprises must adopt a layered defense strategy that includes timely patch management, AI‑driven threat detection, and strict controls over third‑party add‑ins. The convergence of legacy and novel techniques expands the attack surface, demanding continuous vigilance.
7️⃣ CrowdStrike Recognized as Customer’s Choice for User Authentication

Key Points:
- Gartner Peer Insights awards CrowdStrike top rating for user authentication solutions
- Recognition reflects strong performance in MFA and password‑less technologies
- Six zero‑day vulnerabilities patched in the latest release, enhancing security posture
- Customer feedback highlights ease of integration with zero‑trust frameworks
Description:
CrowdStrike earned the Gartner Peer Insights “Customer’s Choice” accolade for its user authentication portfolio, underscoring its leadership in identity security. The company also reported the remediation of six zero‑day flaws in its recent update cycle, reinforcing its commitment to secure authentication.
Why It Matters:
Identity remains a critical attack vector; validated authentication solutions reduce credential‑stuffing and phishing success rates. Organizations aiming for zero‑trust can leverage CrowdStrike’s proven tools to strengthen access controls and streamline compliance.
8️⃣ Scaling SOC Automation with Falcon Fusion SOAR
Key Points:
- Falcon Fusion provides pre‑built playbooks for common incident types
- Integration with SIEM, TIP, and endpoint platforms accelerates triage
- Automation can cut mean time to response (MTTR) by up to 70 %
- Customizable workflows support both cloud‑native and on‑prem environments
Description:
CrowdStrike’s Falcon Fusion SOAR solution enables security operations centers to automate repetitive tasks, orchestrate cross‑tool responses, and standardize incident handling. The platform offers a library of ready‑to‑deploy playbooks that align with MITRE ATT&CK techniques.
Why It Matters:
SOC teams face alert fatigue and resource constraints. Deploying Falcon Fusion helps maximize analyst efficiency, ensuring rapid containment of threats while freeing personnel to focus on high‑impact investigations.
9️⃣ VMware Advances Zero‑Trust Private Cloud with vDefend Lateral Security

Key Points:
- vDefend adds real‑time lateral movement detection to private cloud workloads
- Built on VMware NSX, it enforces micro‑segmentation policies automatically
- Integrates with existing SIEMs and threat‑intel feeds for enriched alerts
- Designed to protect multi‑cloud and hybrid environments from supply‑chain attacks
Description:
VMware’s vDefend solution extends zero‑trust principles to private cloud environments by providing continuous monitoring of east‑west traffic and automated containment of suspicious lateral movements. The service leverages NSX micro‑segmentation to enforce granular policies without manual rule creation.
Why It Matters:
As enterprises shift workloads to private clouds, traditional perimeter defenses become insufficient. vDefend offers visibility and control over internal traffic, mitigating the risk of credential‑based lateral attacks that can compromise critical applications.
🔟 Password Managers Face New Trust Challenges After Vulnerability Study

Key Points:
- Independent research uncovered critical flaws in several popular password managers
- Vulnerabilities could allow attackers to extract stored credentials if exploited
- Vendor responses include prompt patches and third‑party security audits
- Study warns of potential supply‑chain attacks leveraging password‑manager weaknesses
Description:
A recent investigation published by The Register highlighted serious security weaknesses in multiple widely used password‑manager applications. The flaws, if weaponized, could enable threat actors to harvest stored passwords and other sensitive data, undermining a core security control.
Why It Matters:
Password managers are foundational to credential hygiene. Organizations must ensure that selected solutions undergo rigorous third‑party assessments, maintain up‑to‑date patches, and consider additional layers such as hardware‑based MFA to mitigate residual risk.
Stay vigilant and prioritize mitigation to safeguard your enterprise.
Member discussion