Claude Code Flaw Lets Attackers Run Code and Steal API Tokens via Malicious Projects
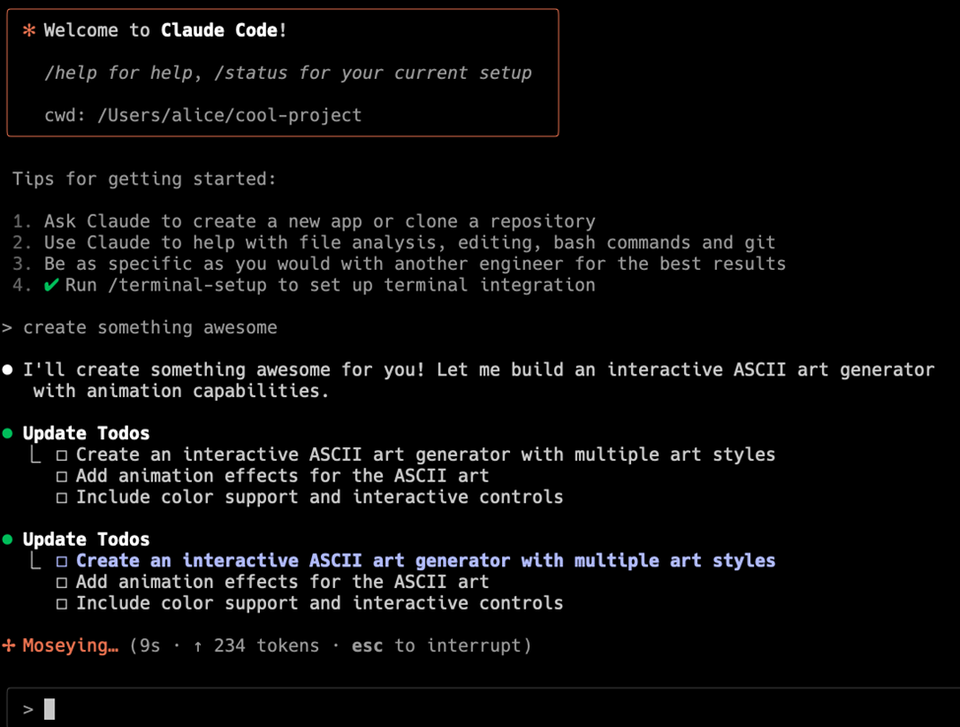
Check Point researchers identified two critical bugs in Anthropic’s Claude Code AI‑assisted coding assistant. The vulnerabilities are triggered when a developer opens a project file that contains specially crafted payloads. One flaw enables remote code execution on the host machine, while the other silently harvests the user’s Anthropic API credentials, sending them to an attacker‑controlled server.
The issue creates a high‑impact supply‑chain risk for any organization that integrates Claude Code into its development workflow. Compromised credentials can be used to access other Claude services, and the executed payloads can install backdoors, exfiltrate source code, or pivot to broader network assets. Defenders should treat Claude Code files as untrusted, enforce strict sandboxing or disable the extension, monitor for anomalous API calls, and apply any vendor patches as soon as they are released.
Categories: Vulnerabilities & Exploits, AI Security & Threats
Source: Read original article



Member discussion