Claude AI Project Files Weaponized for Remote Code Execution and Token Theft
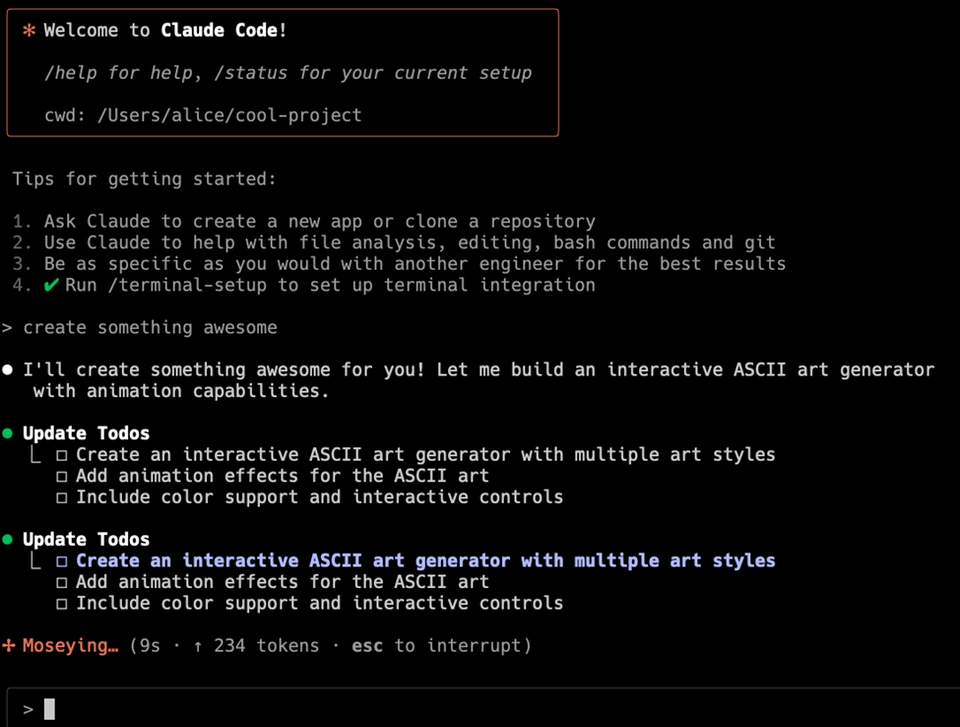
Threat actors are targeting Claude AI code project files, inserting malicious payloads that execute arbitrary commands on vulnerable hosts and silently harvest stored API tokens. By embedding the malicious code directly into the project’s source files, the attackers ensure the payload runs during normal build or deployment processes, effectively bypassing traditional security gates that focus on binary or container artifacts.
The compromise gives attackers remote code execution capabilities and access to privileged credentials, enabling further lateral movement and data exfiltration across the victim’s environment. Defenders must tighten CI/CD pipeline security—implement strict code‑review policies, enforce signed commits, and monitor for anomalous token usage—to detect and block these covert modifications before they reach production.
Categories: Malware & Ransomware, Vulnerabilities & Exploits, AI Security & Threats
Source: Read original article




Member discussion