Chrome Extension Hijack Exploits New Gemini Panel, Threatening Sessions and Prompt Data
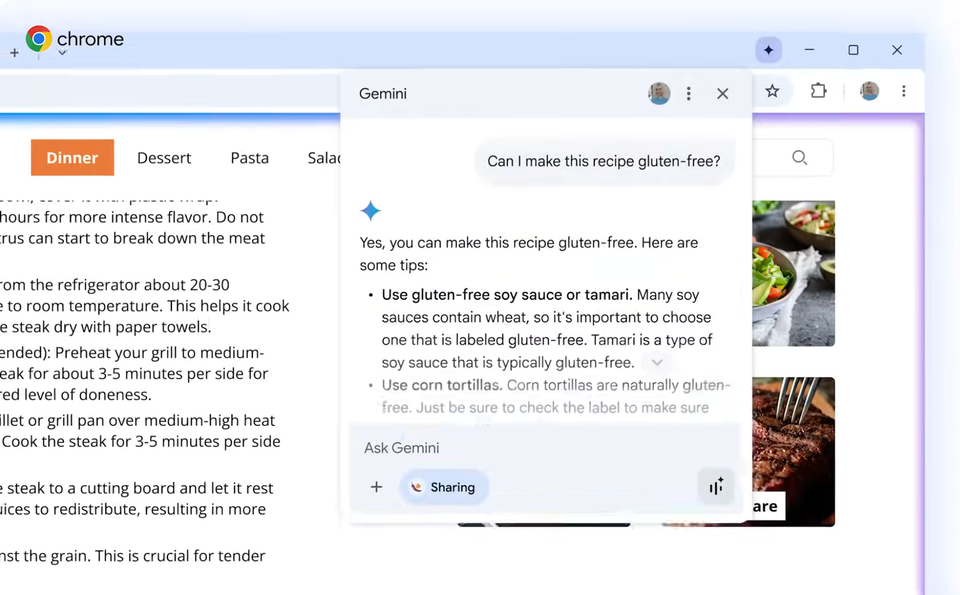
Palo Alto Networks discovered that malicious Chrome extensions can intercept and manipulate the newly added Gemini panel. By injecting script into the panel’s UI, the extensions can hijack active user sessions, capture authentication tokens, and siphon AI model prompts entered by the user. The flaw arises from insufficient isolation between third‑party extensions and the Gemini interface, allowing code execution with the same privileges as the browser.
The breach can lead to full session takeover, credential theft, and exposure of proprietary or sensitive prompts used with Gemini’s AI services. Defenders must prioritize extension vetting, enforce strict allow‑lists, and monitor for anomalous network traffic from browsers. Prompt patching of Chrome, applying CSP policies, and employing behavioral analytics can mitigate the risk of this emerging attack vector.
Categories: Vulnerabilities & Exploits, AI Security & Threats, Identity & Access Management
Source: Read original article




Member discussion