GreyNoise Adds Vendor CVE & Tag Spike Feeds for Rapid Threat Detection
GreyNoise has released two new event streams—Vendor CVE Spike and Tag Spike—that automatically flag sudden surges in Internet‑
Cyber Threats surge as AI tools expose data 🚨. New vendor CVE spikes and cloud actor tracking reshape defenses 🤖.
Hello, here is your Daily Cybersecurity & AI Threat Intelligence newsletter for 2026-02-10.
Today's headlines
* GreyNoise launches real‑
CrowdStrike Boosts Linux Web‑Shell Detection with Real‑Time AI Threat Hunting
CrowdStrike’s latest Falcon update adds dedicated modules that continuously monitor script execution on Linux hosts. By applying AI‑driven
Digital Parasites Keep Ransomware Inside Networks Longer, Extending Dwell Time
Picus Security’s Red Report, cited by The Hacker News, reveals a tactical evolution from flash‑in‑the‑pan ransomware
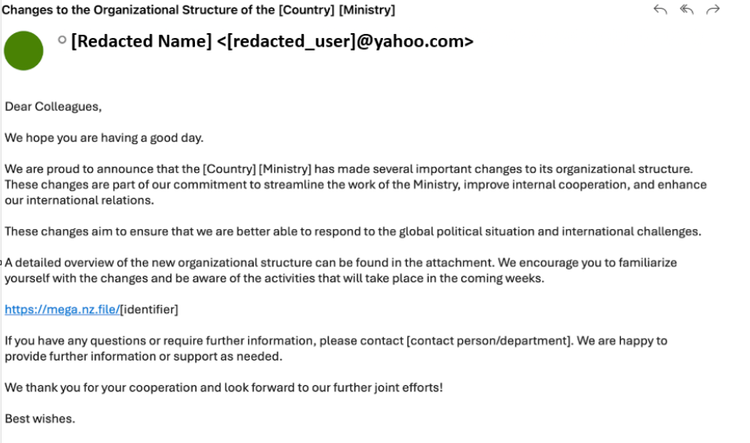
APT TA423 Watering‑Hole Injects ScanBox Keylogger into News Sites
A Chinese‑based threat group identified as APT TA423 has been running a watering‑hole campaign that compromises high‑traffic
CISA Flags Surge of Public Attack Tools Lowering Threat Actor Barriers
The Cybersecurity and Infrastructure Security Agency (CISA) released an advisory that catalogs dozens of freely available tools that have already
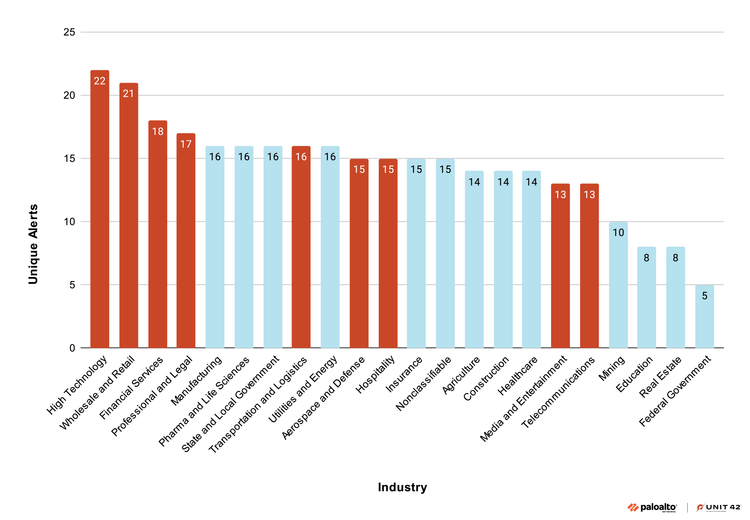
Native Cloud‑Logging Uncovers Scattered Spider and Halcyon Silk Typhoon Tactics
Unit 42 discovered that attackers are exploiting built‑in cloud‑logging services to hide their movements while still leaving forensic
Romanian Oil Pipeline Operator Conpet Disrupted by Cyber Intrusion
On 9 February, Check Point’s Threat Intelligence Report documented a successful cyber intrusion against Conpet, Romania’s national oil
Amaranth‑Dragon weaponizes CVE‑2025‑8088 against SE Asia enterprises
Checkpoint researchers have confirmed that the state‑aligned threat group Amaranth‑Dragon has added the newly disclosed CVE‑2025‑8088
Shadow Campaigns Exploit Zero‑Days to Hijack Global Critical Infrastructure
Unit 42 tracked the Shadow Campaigns group leveraging a blend of publicly known flaws and undisclosed zero‑day exploits to