Meta on Trial: Platform Safety Scrutinized Over Child Exploitation Allegations
A federal jury is hearing a lawsuit that accuses Meta’s family of apps—particularly Facebook and Instagram—of facilitating
VMware vDefend Lateral Security Boosts Zero‑Trust in Private Clouds
VMware has introduced vDefend Lateral Security, an AI‑driven module that monitors and validates every inter‑workload communication within private
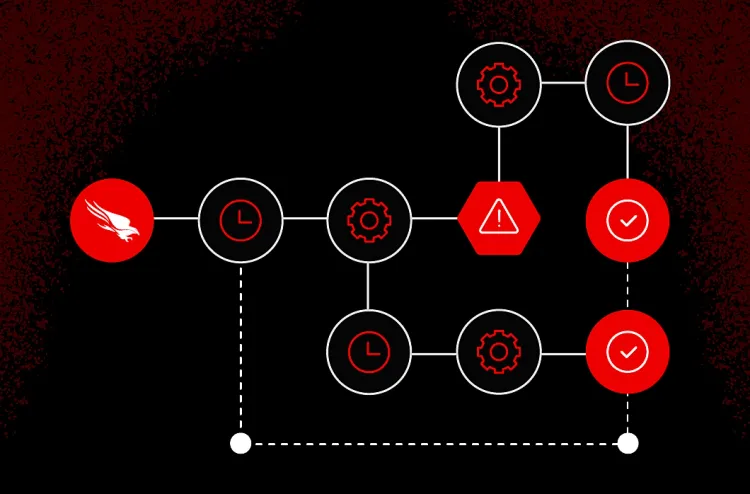
Falcon Fusion SOAR Accelerates SOC Automation and Cuts Response Time
CrowdStrike unveiled Falcon Fusion SOAR, a low‑code platform that lets security operations centers stitch together alerts from disparate security
CrowdStrike’s Human‑AI Loop Accelerates Zero‑Day Detection and Response
CrowdStrike disclosed a “human‑AI feedback loop” in which threat analysts continuously inject contextual insights—such as tactics, techniques, and
Nation‑State Hijacks Notepad++ Updates, Threatening Developer Supply Chains
Palo Alto Networks’ Unit 42 uncovered a supply‑chain attack on the popular Notepad++ editor, where a nation‑state actor
Conpet Oil Pipeline Hit by Cyberattack, Exposing Energy Critical Infrastructure Gaps
Romania’s national oil pipeline operator, Conpet, suffered a cyber intrusion that crippled its internal IT environment and rendered its
AI‑Driven Prompt RCE and 0‑Click Claude Exploit Spark New Threat Wave
The latest ThreatsDay Bulletin reports a coordinated surge of AI‑powered attacks. Researchers uncovered a prompt‑injection remote code execution
Amaranth-Dragon Leverages CVE‑2025‑8088 to Target Southeast Asian Networks
Checkpoint researchers have linked the state‑aligned threat group Amaranth‑Dragon to active exploitation of the newly disclosed CVE‑2025‑
Advanced APT weaponization escalates espionage risks across Southeast Asia 🚀. Simultaneously, AI‑driven and supply‑chain attacks strain enterprise resilience 🛡️.
Good morning, February 12, 2026. Below are the critical threats demanding executive attention this week.
Today's headlines
* APT
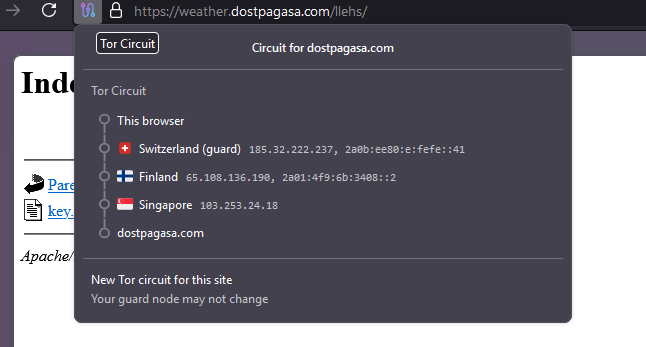
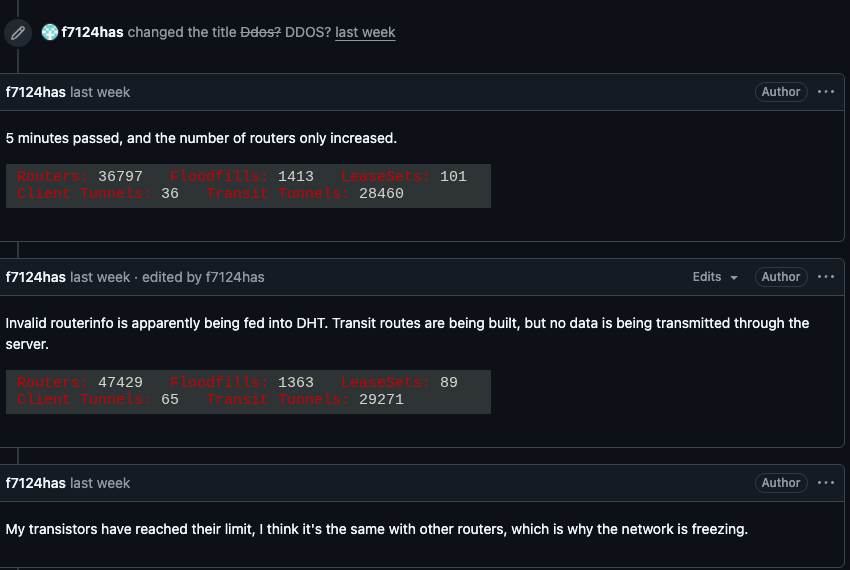
Kimwolf Botnet Weaponizes I2P, Flooding Anonymity Network with Massive Traffic
The Kimwolf botnet has begun abusing the I2P anonymity network’s open routing architecture to inject a torrent of unwanted