CrowdStrike Tops Gartner Peer Insights for Cloud‑Native Authentication
CrowdStrike has been named a Customers’ Choice in the 2026 Gartner Peer Insights for User Authentication. The accolade reflects strong
Outlook Add‑In Hijacks Fuel AI‑Generated Malware in Blended Threat Campaigns
A wave of Outlook add‑in hijacks has been observed, with threat actors compromising legitimate Office Store extensions to inject
Lithuania Launches National AI‑Fraud Defense Initiative to Shield E‑Signatures & Health Data
Lithuania’s government has unveiled a €20 million, three‑year program aimed at countering AI‑driven cyber fraud. The effort
Romanian Oil Pipeline Outage Exposes Critical Energy Cyber Weaknesses
On February 9, Check Point’s threat report documented a cyber intrusion against Conpet, Romania’s national oil pipeline operator.
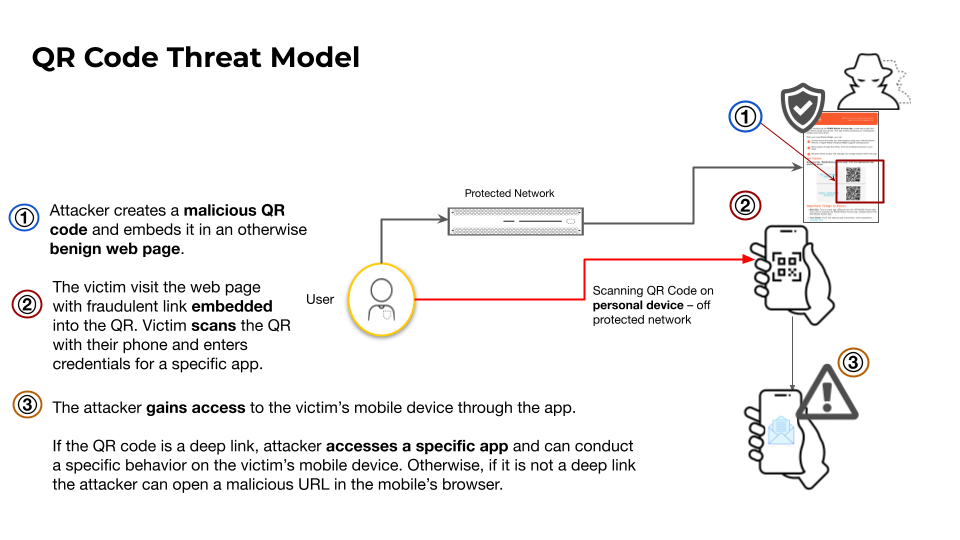
QR Code Phishing Turns Smartphones Into New Attack Vectors
Researchers observed threat actors embedding malicious URLs in QR codes that, when scanned, direct victims to credential‑harvesting webpages or
Amaranth‑Dragon Exploits CVE‑2025‑8088 in SE Asian Supply‑Chain Attack
Check Point researchers identified that the APT‑41 affiliated group, operating under the name Amaranth‑Dragon, weaponized the recently disclosed
Spike in Scans Targets New BeyondTrust RCE Vulnerability, Threat Actors Reconnaissance Rising
GreyNoise has observed a sharp increase in scanning traffic aimed at the newly disclosed CVE‑2026‑1731 remote code execution
RCE exploits and AI fraud heighten risk 🚨. Zero‑day and supply‑chain attacks test resilience 🛡️.
Hello, February 16, 2026 – here's the latest threat intelligence you need to act on. Stay ahead of emerging
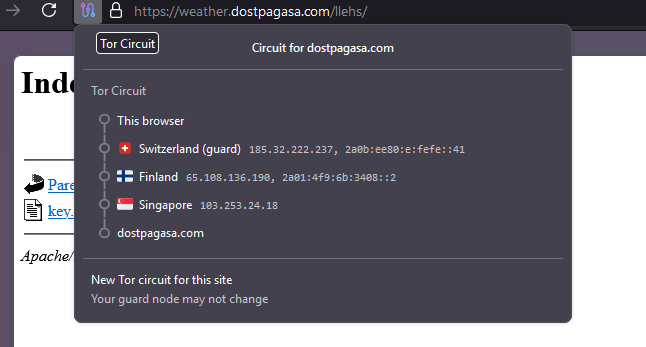
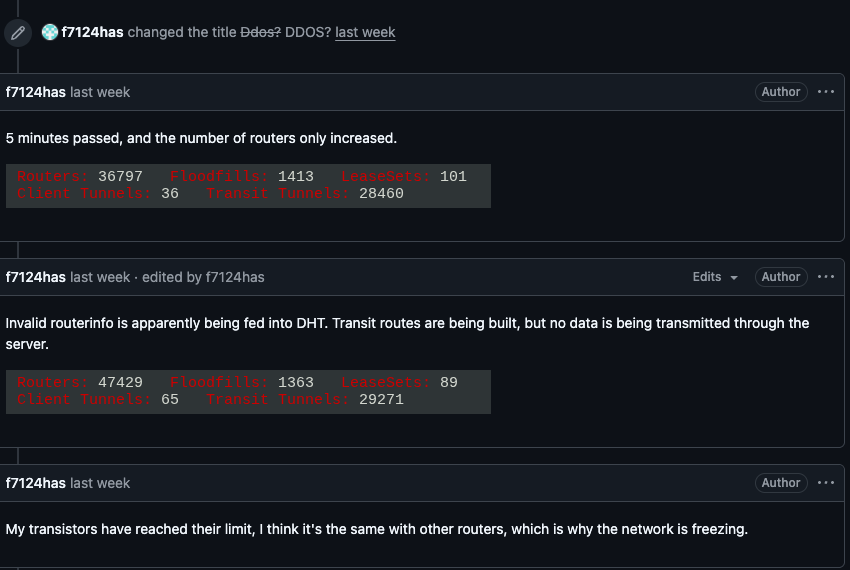
Kimwolf Botnet Hijacks I2P, Boosting Stealthy DDoS Threats
The Kimwolf botnet has started routing its command‑and‑control (C2) traffic through the I2P anonymity network. By embedding its
AI-Driven Zero Trust Cuts Manual Policy Work, Boosts Defender Efficiency
VMware’s latest blog details a new AI engine that ingests user and device behavior, contextual threat intelligence, and existing