OWASP Sunset's Meetup Platform, Shifts Event Coordination to Secure Alternatives
The OWASP Foundation announced that its long‑used Meetup.com group will be decommissioned by the end of Q2 2024.
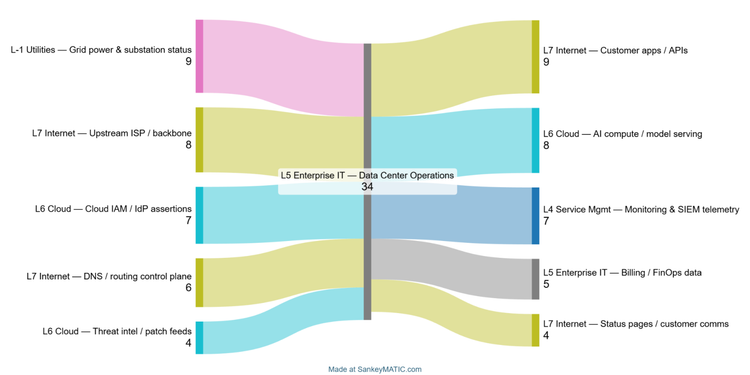
CLAIR Model Empowers Defenders to Map and Mitigate Infrastructure Cascade Risks
The SANS diary recently unveiled the CLAIR (Critical Infrastructure Interdependency) model, a systems‑of‑systems framework that charts how the
AI‑Powered Scans Target Misconfigured FortiGate Firewalls Across Enterprises
A threat group is leveraging AI‑enhanced tools to automatically discover internet‑exposed FortiGate appliances. The bots probe for default
Check Point Explains How CTEM Outshines Classic Vulnerability Management
During a recent Reddit AMA, Check Point security experts broke down their Cyber Threat Exposure Management (CTEM) framework. They highlighted
2️⃣ GreyNoise State of the Edge Report Highlights Attack Hotspots
The 2026 GreyNoise State of the Edge report analyzes billions of internet‑wide observations, revealing where adversary activity clusters and
BeyondTrust RCE Probe Surge Signals Early Exploit Activity
GreyNoise telemetry has identified a sharp increase in reconnaissance traffic aimed at the newly disclosed CVE‑2026‑1731 remote code
AI‑augmented attacks and new RCE exploit pressure defenses 🛡️. Infrastructure interdependency and regulation intensify 📈.
February 25, 2026 – Daily briefing for security leaders.
Today's headlines
* BeyondTrust RCE vulnerability shows early exploitation activity.
* AI‑
Manual Data‑Handoffs Threaten National‑Security Networks via Stolen Media
The CYBER360 study, cited by The Hacker News, found that a large share of national‑security agencies still move sensitive
Unpatched Web Flaw Lets Hackers Steal Data of 2.5M Student Loan Borrowers
A threat‑actor group compromised a leading student loan servicer by exploiting a known but unpatched web application vulnerability. The
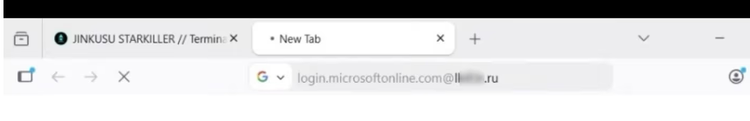
Starkiller Phishing Service Mirrors Real Logins, Skips MFA and Harvests Tokens
KrebsOnSecurity exposed a new phishing‑as‑a‑service platform dubbed “Starkiller” that routes victims through live, unmodified login pages of