Open S3 Bucket Exposes 2.5 Million Student Loan Records
A student loan servicing platform suffered a data breach when attackers discovered a publicly accessible Amazon S3 bucket that lacked
Cloud Imperium Data Breach Exposes Code, Credentials, and Million‑Player Data
Cloud Imperium, the UK‑based studio behind Star Citizen, quietly announced a security incident that gave attackers access to its
Samsung TV ACR Data Harvest Fixed After Texas Legal Push
Security researchers uncovered that Samsung Smart TVs were using the Automatic Content Recognition (ACR) feature to continuously capture and transmit
APT‑TA423 Uses ScanBox JavaScript Keylogger in News Site Watering‑Hole Attack
An APT group identified as TA423 weaponized the open‑source ScanBox reconnaissance tool and embedded it in compromised JavaScript on
Iran‑Aligned Threat Actors Intensify Phishing, Supply‑Chain, and Ransomware Campaigns in 2026
Palo Alto Networks’ Unit 42 observed a marked uptick in activity by Iranian state‑aligned groups throughout 2026. The actors
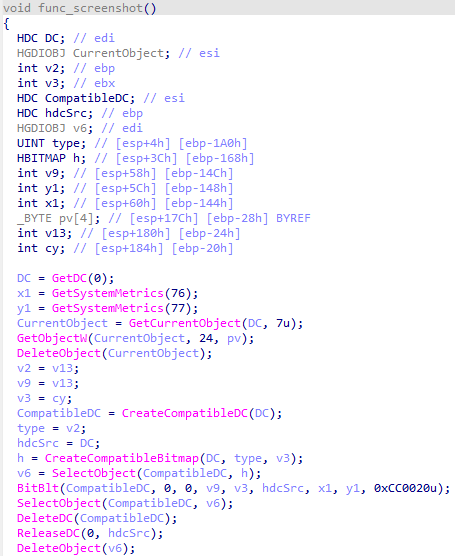
LummaStealer Returns, Teams with CastleLoader Dropper for Stealthy Access
Bitdefender’s threat‑research team has confirmed that the long‑dormant LummaStealer infostealer has resurfaced, now piggybacking on the CastleLoader
CrowdStrike Secures NCSC CIR Certification, Boosting IR Credibility
CrowdStrike announced that its incident response (IR) services have earned the UK National Cyber Security Centre’s Certified Incident Response
GoAnywhere MFT Zero‑Day Slips Past Firewalls, Lets Storm‑1175 Run Code
Microsoft Threat Intelligence disclosed that the Storm‑1175 threat group exploited CVE‑2025‑10035, a critical deserialization flaw in the
SloppyLemming Dual‑Chain Attack Targets Pakistan and Bangladesh Government Networks
The threat group identified as SloppyLemming conducted a coordinated campaign against ministries, law‑enforcement agencies, and critical infrastructure operators in
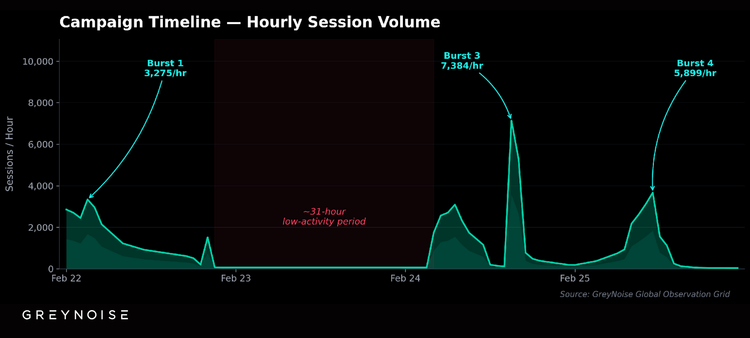
Proxy‑Chained Scans Target SonicWall Firewalls, Skipping Rate Limits
GreyNoise has identified an active reconnaissance campaign that leverages a chain of commercial proxy services to systematically probe SonicWall firewalls.