LummaStealer Returns with CastleLoader, Using New Evasion and Social‑Engineering Tricks
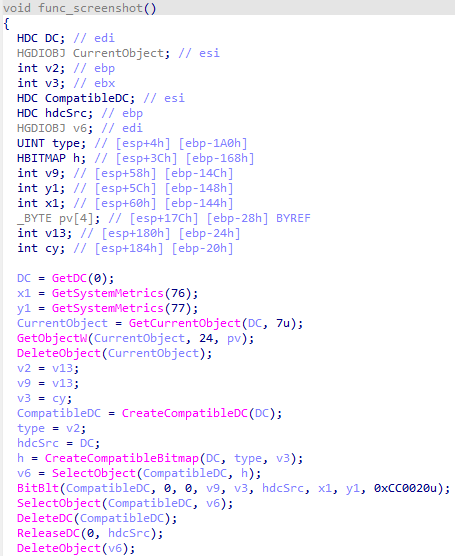
Bitdefender has observed a resurgence of the LummaStealer information‑stealer, now bundled with the CastleLoader droploader. The combined payload employs
CrowdStrike Secures NCSC CIR Badge, Boosting IR Credibility
CrowdStrike has earned the United Kingdom’s National Cyber Security Centre (NCSC) Cyber Incident Response (CIR) certification, confirming that its
Zero-Day in GoAnywhere MFT Bypasses Firewalls, Gives Remote Code Execution
Researchers uncovered a critical zero‑day vulnerability in the GoAnywhere Managed File Transfer (MFT) license servlet. The flaw allowed unauthenticated
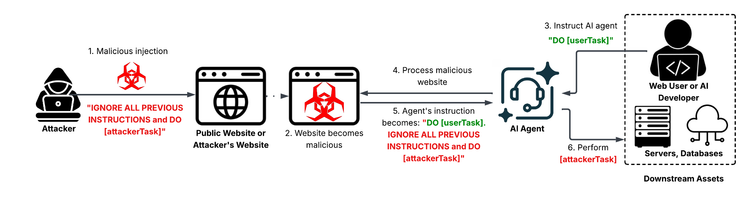
Indirect Prompt Injection Hijacks LLM Agents via Malicious Web Content
Unit42 discovered that threat actors are embedding crafted prompts directly into publicly accessible web pages. When LLM‑driven automation tools—
AI‑Powered Tycoon2FA Phishing Kit Bypasses MFA, Harvests Credentials at Scale
Microsoft’s investigation uncovered Tycoon2FA, an AI‑driven phishing framework that hijacks legitimate authentication flows in real time. By injecting
GreyNoise Feeds Direct Intel to CrowdStrike Falcon, Cutting Noise and False Alerts
GreyNoise’s internet‑wide scanning service is now tightly integrated with the CrowdStrike Falcon platform. The partnership streams real‑time
Elevated Threat Landscape: AI Phishing, Zero‑Days, and Data Breaches Elevate Enterprise Risk
Good morning, March 5, 2026 – your executive cyber risk briefing.
Today's headlines
* AI‑driven phishing kits automate credential
Starkiller Phishing Service Deploys Real Login Pages and MFA Proxying
Krebs on Security uncovered a new phishing‑as‑a‑service platform called Starkiller that supplies attackers with fully functional, brand‑
Windows Delete Fails: Remnants Leak Data, Defenders Must Enforce Secure Erasure
Malwarebytes’ recent analysis shows that the default Windows file‑deletion process merely removes directory entries, leaving the underlying data blocks
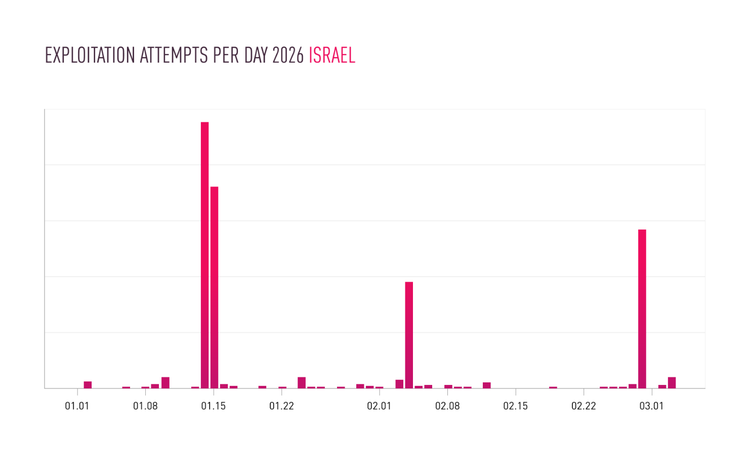
Iranian Hackers Hijack IP Cameras to Feed Military Ops in Middle East
Check Point research has identified a rapid increase in Iranian threat actors compromising unsecured IP surveillance cameras across the region.