Storm‑1175 weaponizes GoAnywhere MFT zero‑day to slip past perimeter defenses
In September 2025 the threat group Storm‑1175 weaponized a critical zero‑day in GoAnywhere Managed File Transfer (CVE‑2025‑
OpenAI Codex Security Scans 1.2M Commits, Flags 10,561 Critical Bugs
OpenAI has released Codex Security, an AI‑driven agent that automatically reviewed more than 1.2 million recent code commits
GreyNoise Intel Now Natively Built into CrowdStrike Falcon
GreyNoise’s threat data has been directly integrated into the CrowdStrike Falcon platform, giving defenders access to real‑time, configurable
AI‑driven vulnerabilities expand attack surface 🚀. Zero‑day exploits pressure resilience 🛡️.
Good morning, March 8, 2026 – here are today’s top cyber and AI threat updates.
Today's headlines
* AI‑
Fake Google Meet Update Delivers Remote‑Access Malware to Victims
Attackers circulated a phishing campaign that mimics a legitimate Google Meet client update. Recipients receive an email with a bogus
ScanBox JavaScript Keylogger Hijacks News Sites in China‑Based Watering‑Hole Campaign
A China‑originated APT group identified as TA423 has been weaponizing the open‑source ScanBox JavaScript keylogger in a series
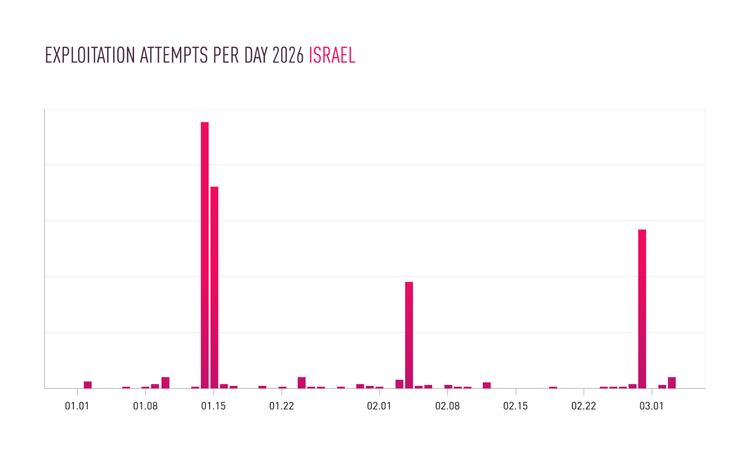
Iranian Threat Actors Hijack IP Cameras in Middle East to Fuel Ops
Check Point’s research team has documented a sharp increase in attacks linked to Iranian actors targeting unsecured IP cameras
Falcon SIEM Now Pulls Logs Directly from Sensors, Boosting Endpoint Visibility
CrowdStrike has added a sensor‑native log collection feature to its Falcon Next‑Gen SIEM. The new capability lets the
AI‑Powered Agents Speed Up State‑Sponsored Attack Chains
Recent research shows that nation‑state threat groups, notably North Korean actors, are deploying autonomous AI agents to automate the
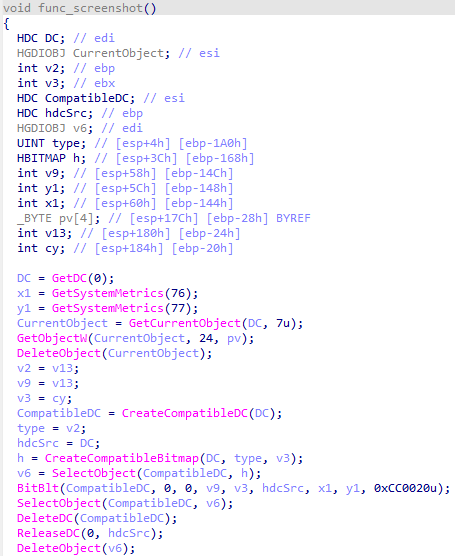
Resurrected LummaStealer Teams with CastleLoader to Target Enterprise Credentials
Bitdefender’s threat‑research team has identified a resurgence of the LummaStealer infostealer, now being bundled with the CastleLoader modular