Ransomware Spike Hits Hospitals, Supply‑Chain Breaches Escalate, New Disclosure Rules Arrive
During the week of March 2‑8, Malwarebytes recorded a sharp uptick in ransomware activity, with attackers focusing on medical
Ransomware Targets Hospitals, Supply‑Chain Breaches Spike – New Regulator Guidance
Malwarebytes’ weekly recap for March 2‑8 shows a sharp rise in ransomware activity, with attackers focusing on medical facilities
AI‑Boosted SOC Tools Now Affordable for Mid‑Market Teams
Emerging security platforms are rolling out AI‑enhanced investigation capabilities specifically designed for mid‑market organizations. Unlike legacy solutions that
WPA3 Handshake Flaw Lets Attackers Sniff Wi‑Fi Traffic
Security researchers have uncovered a new attack that subverts the WPA3 Simultaneous Authentication of Equals (SAE) handshake. By injecting crafted
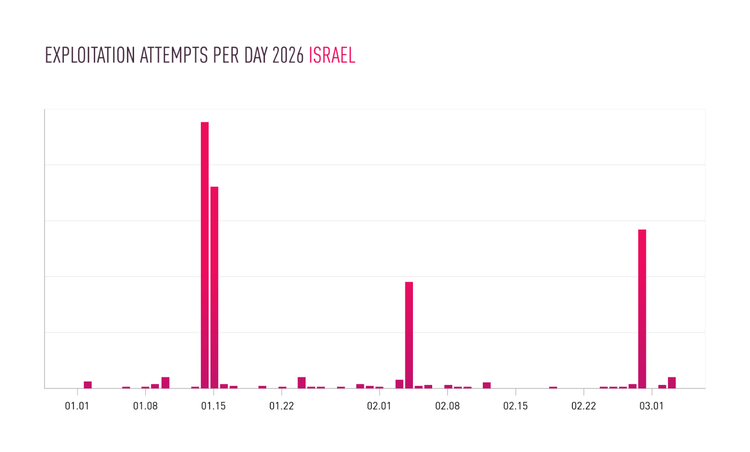
Iranian Hackers Exploit IP Cameras in Middle‑East Conflict for Espionage and Attacks
Checkpoint researchers have documented a sharp rise in compromise attempts against Internet‑protocol cameras deployed in active conflict zones across
Falcon SIEM Now Pulls Logs Directly from Endpoints
CrowdStrike has upgraded Falcon Next‑Gen SIEM to support sensor‑native log collection. The platform can now harvest event data
AI‑Powered Threat Actors Upgrade Phishing and Deepfake Social Engineering
Microsoft’s security blog reports that adversaries are now embedding generative AI into their attack workflows. The technology is being
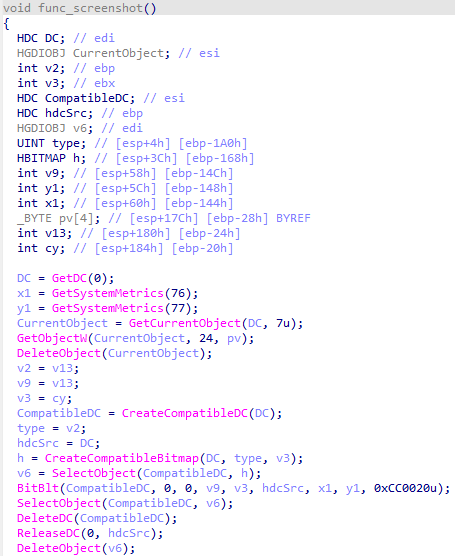
LummaStealer Teams with CastleLoader to Mask Activity as Normal User Behavior
The LummaStealer infostealer has been observed integrating the CastleLoader dropper, creating a hybrid payload that blends malicious actions with typical
Prompt Injection Turns AI Assistants Into New Attack Surface
Researchers have demonstrated that threat actors can craft malicious prompts that coax large language models into performing unintended actions, such
Zero‑Day GoAnywhere MFT Bypasses Perimeter Firewalls, Highlights Need for Defense‑in‑Depth
The threat group Storm‑1175 weaponized CVE‑2025‑10035, a remote‑code‑execution flaw in the GoAnywhere Managed File Transfer