OpenClaw AI Skills Hijacked for Covert Malware Delivery
Threat actors have begun abusing the OpenClaw AI automation platform by publishing deceptive “skills” that appear legitimate but are programmed
New Android Lock‑Screen Bypass Exploits Biometric Pathway, Gives Full Device Access
A recently disclosed Android flaw lets an attacker sidestep the lock screen by corrupting the biometric authentication flow. By injecting
Microsoft Authenticator Leak Lets Apps Sniff One‑Time Codes
Security researchers found that specific builds of Microsoft Authenticator unintentionally broadcast the generated one‑time password (OTP) to any app
Default IoT Admin Accounts: Silent Doorways for Immediate Compromise
IoT devices are shipped with factory‑set administrative usernames and passwords that are rarely changed during rollout. Attackers scanning a
CrowdStrike Falcon Integrates GreyNoise for Real‑Time Bad‑IP Context
CrowdStrike has announced a native integration of GreyNoise threat intelligence into the Falcon platform. The partnership streams GreyNoise’s “noisy
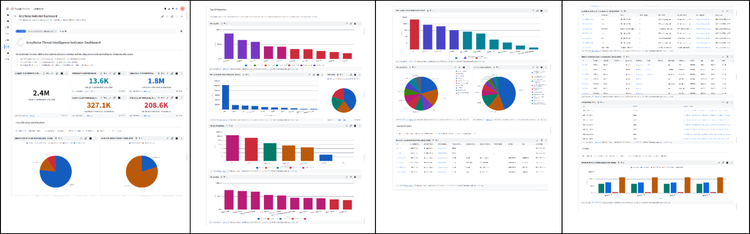
GreyNoise Integrates with Google SecOps for Real‑Time IP Threat Blocking
GreyNoise announced a native integration with Google SecOps, embedding its configurable blocklists and contextual IP intelligence directly into Google Cloud
Strategic Exposure to Emerging Threats & AI‑Driven Attack Vectors Demands Immediate Control
March 12, 2026 – Hello security leaders, here’s the latest risk intelligence.
Today's headlines
* GreyNoise integration streamlines Google
Gemini‑Powered Groundsource Turns News Into Real‑Time Threat Intel
Google Research launched Groundsource, a new service built on the Gemini large‑language model that automatically parses news articles into
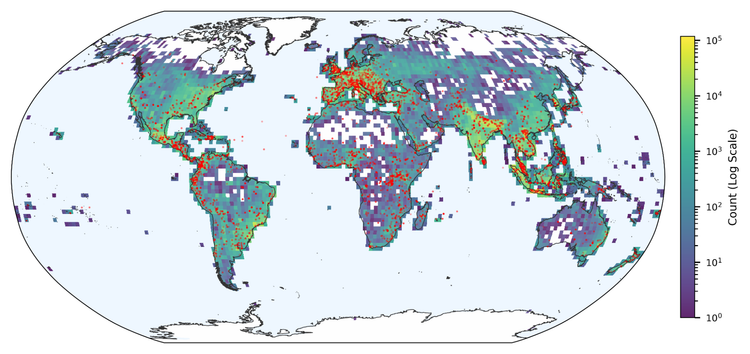
Spike in SSH Scans Signals Imminent Credential‑Theft Campaigns
The Internet Storm Center’s daily report shows a sharp increase in SSH scanning traffic over the past 48 hours,
AI Attack Bots Learn to Replicate Exploits Across Networks Without Human Guidance
A team of security researchers released a paper showing that autonomous cyber‑attack agents can abstract the techniques they learn