Microsoft Authenticator Leak Exposes MFA Codes Until App Update
A vulnerability was discovered in the Microsoft Authenticator mobile app that could unintentionally reveal the time‑based one‑time passwords
Critical Android Graphics Driver Flaw Lets Attackers Bypass Lock Screen in Seconds
Malwarebytes has identified a critical zero‑day vulnerability in Android’s graphics driver stack. By delivering a specially crafted image
IoT Devices Using Default Admin Logins Pose Critical Lateral Movement Risk
A recent SANS diary entry highlighted that a large number of Internet‑of‑Things devices are still deployed with administrative
GreyNoise Now Integrated Directly into CrowdStrike Falcon
GreyNoise intelligence has been embedded into the CrowdStrike Falcon platform, allowing analysts to overlay internet‑wide scanning data directly onto
GreyNoise + Google SecOps: Auto‑Block Noisy IPs in Cloud SCC
GreyNoise has launched a native integration with Google SecOps that pipes its noisy‑IP intelligence straight into the Cloud Security
AI‑driven attack automation escalates supply‑chain risk 🚀. Mobile OS and MFA flaws expose credential theft vectors 🔓.
Good morning, March 12 2026 – here’s the latest intelligence you need.
Today's headlines
* GreyNoise adds real‑time
Google’s Groundsource Uses Gemini to Turn Crisis News into Structured Threat Intel
Google Research unveiled Groundsource, a pipeline that leverages the Gemini large‑language model to ingest free‑form news articles about
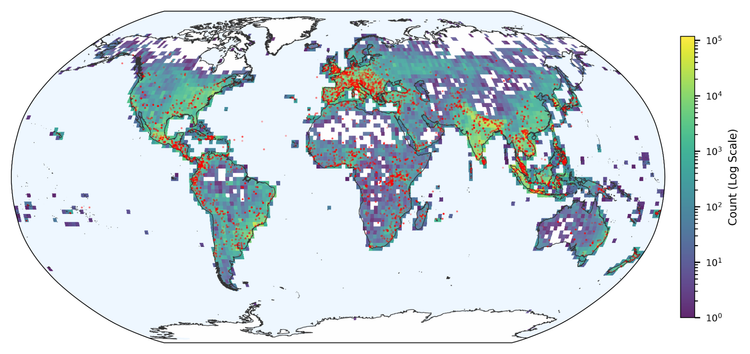
Surge in Legacy Brute‑Force and New Port‑Scan Tactics Spotted Globally
The March 12, 2026 ISC Stormcast report shows a sharp rise in brute‑force attempts targeting legacy services such as
Autonomous Attack Bots Learn to Exploit New Bugs Without Human Help
Researchers at a leading university published a paper on arXiv showing that autonomous cyber‑attack agents can generalize learned behaviors
OpenClaw AI Powers Adaptive Reverse Shells and Cognitive Rootkits
Researchers have confirmed that threat actors are weaponizing the OpenClaw AI framework to auto‑generate reverse shells and rootkits that