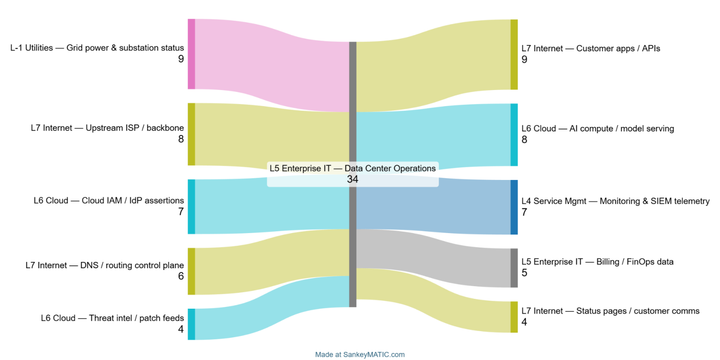
Edge‑Based OT Monitoring Gives Defenders Critical Seconds to Stop Attacks
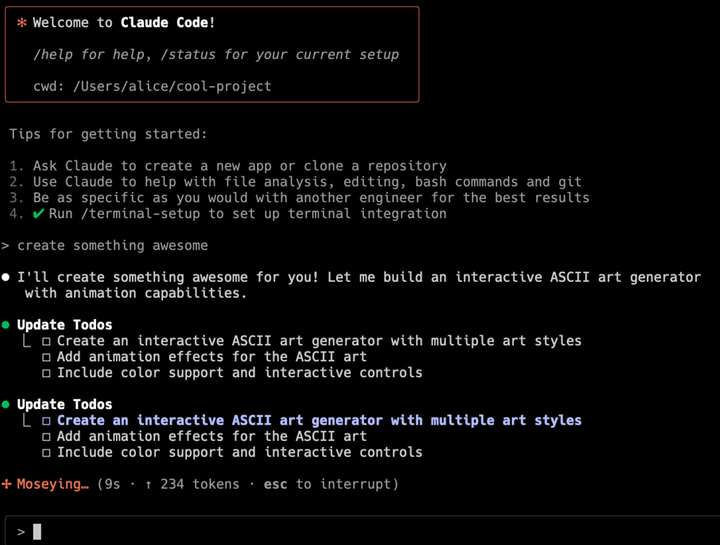
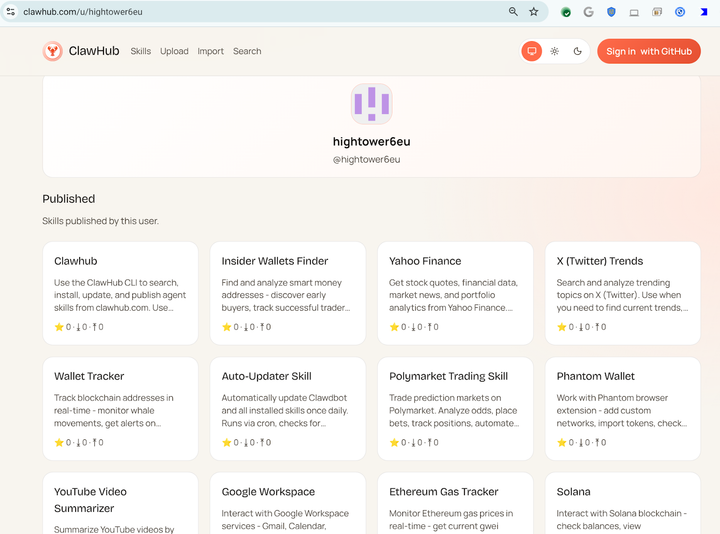
Unit42 demonstrated that shifting threat detection from central IT servers to the operational technology (OT) edge dramatically shortens the time it takes to spot malicious activity. By ingesting and analyzing sensor data, PLC logs, and network flows directly on gateways or edge appliances, anomalies are flagged in real time, before