AI supply‑chain breaches expand attack surface. 🚨 Russian actors hijack secure messaging. 🔐

Good morning, March 24, 2026 – here’s the latest strategic threat intel.
Today's headlines
- GreyNoise integration cuts false positives for Google SecOps.
- Supply‑chain backdoors found in popular LiteLLM AI library.
- CanisterWorm wiper campaign targets Iranian critical infrastructure.
- Russian hackers hijack Signal and WhatsApp accounts, prompting alerts.
- Student loan data breach exposes 2.5 M personal records.
1️⃣ GreyNoise bolsters Google SecOps with real‑time blocklists
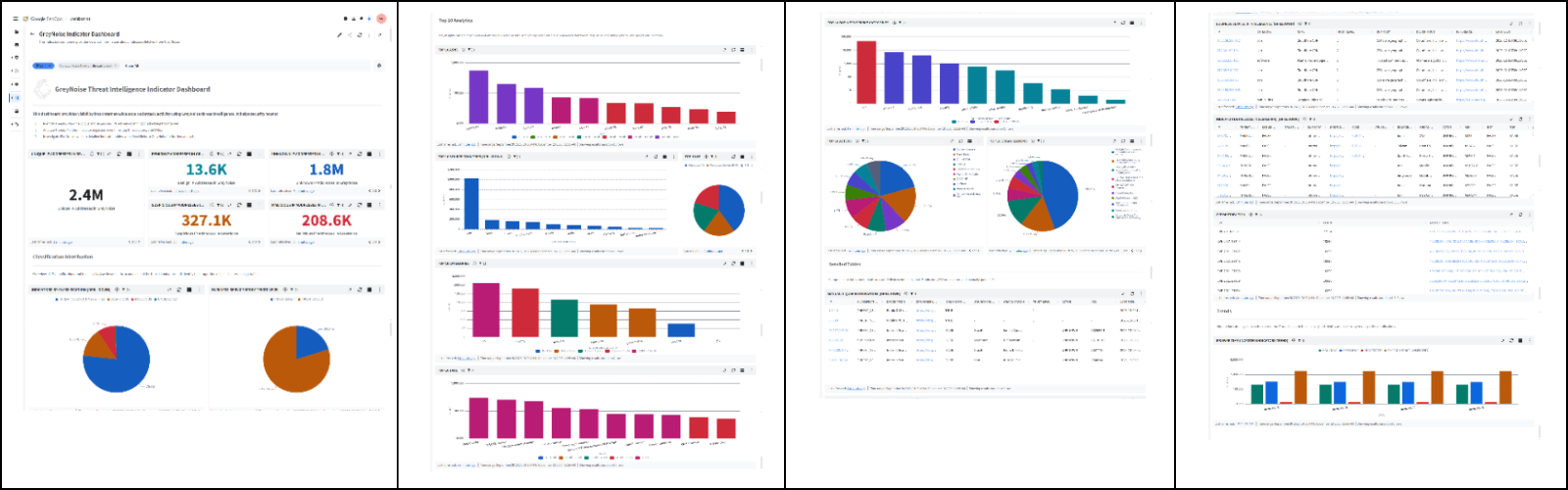
Key Points:
- Automated, configurable blocklists block malicious IPs instantly.
- Reduces noisy alerts from internet scanners by up to 80%.
- Adds context to incidents, speeding investigation timelines.
- Supports CVE early‑warning and active exploitation tracking.
Description:
GreyNoise announced native integrations with Google SecOps, delivering real‑time blocklists and enriched threat data directly into Google’s security platforms. The partnership enables security teams to filter low‑value noise, prioritize genuine threats, and accelerate response workflows across SIEM, SOAR and firewall tools.
Why It Matters:
For CISOs, the integration translates to measurable reductions in alert fatigue, faster containment of genuine threats, and clearer visibility into exploitation trends—key factors for maintaining operational resilience and protecting critical assets.
2️⃣ Supply‑chain backdoor discovered in LiteLLM CI/CD pipeline

Key Points:
- Backdoors injected into LiteLLM versions 1.82.7‑1.82.8.
- Compromise traced to malicious Trivy CI/CD scans.
- Affected deployments can exfiltrate data and execute arbitrary code.
- Vendor issued emergency patches and remediation guidance.
Description:
Research revealed that the TeamPCP group injected persistent backdoors into the open‑source LiteLLM library during CI/CD processes, leveraging a compromised Trivy scanner. The malicious code activates when the library processes LLM requests, providing attackers with stealthy command‑and‑control capabilities.
Why It Matters:
Enterprises that embed AI models into production pipelines now face a heightened supply‑chain risk. Immediate patching and verification of CI/CD integrity are essential to prevent lateral movement and data leakage.
3️⃣ LiteLLM supply‑chain breach confirmed by independent analysis
Key Points:
- Independent security firm validates backdoor presence.
- Attack vector mirrors the Trivy CI/CD compromise.
- Potential impact spans cloud‑native AI services.
- Recommendations include rolling back to safe versions and scanning for indicators of compromise.
Description:
The Register’s investigation corroborated earlier reports, confirming that LiteLLM versions 1.82.7‑1.82.8 contain malicious payloads inserted via a compromised Trivy scan. The analysis details the backdoor’s behavior, including credential harvesting and remote shell execution within AI workloads.
Why It Matters:
The confirmation stresses the urgency for organizations to audit AI‑related dependencies, enforce strict code‑review policies, and monitor runtime environments for anomalous activity, thereby reducing exposure to supply‑chain attacks.
4️⃣ CanisterWorm deploys destructive wiper against Iranian infrastructure
Key Points:
- Wiper malware overwrites critical system files.
- Targets government and energy sectors in Iran.
- Utilizes novel anti‑analysis techniques to evade detection.
- Attribution points to a state‑sponsored group.
Description:
KrebsOnSecurity reported the activation of the CanisterWorm wiper, a destructive payload that encrypts and erases data on infected hosts across Iranian ministries and energy providers. The malware employs advanced evasion methods, including environment checks and delayed execution, to prolong its impact.
Why It Matters:
The campaign underscores the growing use of wiper tools for geopolitical disruption. Organizations operating in high‑risk regions must bolster endpoint protection, enforce strict backup routines, and monitor for Indicators of Compromise associated with CanisterWorm.
5️⃣ OWASP phases out Meetup, shifts community engagement
Key Points:
- Official retirement of the OWASP Meetup platform.
- Community to migrate events to alternative channels.
- Potential impact on knowledge‑sharing and vulnerability coordination.
- OWASP urges members to adopt centralized communication hubs.
Description:
The OWASP Foundation announced the decommissioning of its Meetup site, directing members to consolidate discussions onto its main website and partner platforms. The move aims to streamline event management and improve security of community communications.
Why It Matters:
Security professionals rely on OWASP forums for timely vulnerability disclosures and best‑practice exchange. Transitioning to more secure, centrally managed channels reduces the risk of phishing or misinformation within the global security community.
6️⃣ Russian actors target Signal and WhatsApp accounts

Key Points:
- FBI and CISA issue joint advisory on messaging hijacks.
- Actors use SIM‑swap and social engineering to seize accounts.
- Compromised accounts used for espionage and disinformation.
- Recommendations include multi‑factor authentication and carrier alerts.
Description:
Malwarebytes reports that U.S. agencies warned of Russian‑linked groups hijacking accounts on encrypted messaging services such as Signal and WhatsApp. The attackers employ SIM‑swap attacks and phishing to gain control, then exploit the trusted channels for covert communications.
Why It Matters:
Secure messaging is a cornerstone of confidential corporate communication. Organizations must enforce MFA, educate users on SIM‑swap risks, and monitor for anomalous login activity to safeguard sensitive information.
7️⃣ Massive student loan data breach exposes 2.5 M borrowers

Key Points:
- Exfiltration of personal and financial data of 2.5 million borrowers.
- Data includes Social Security numbers, loan balances, and contact info.
- Breach attributed to a misconfigured cloud storage bucket.
- Affected institution offers free credit monitoring to victims.
Description:
ThreatPost detailed a breach at a major student loan servicer where a misconfigured cloud bucket allowed unauthorized access to a database containing detailed borrower information. The incident was discovered after suspicious activity alerts from a third‑party security vendor.
Why It Matters:
The exposure of sensitive financial data heightens identity theft risk and regulatory liability. Financial services leaders must audit cloud configurations, enforce least‑privilege access, and implement continuous monitoring to prevent similar incidents.
8️⃣ New SANS analysis reveals stealthy IP‑KVM exploitation

Key Points:
- IP‑based KVM devices used as pivot points in targeted attacks.
- Detection signatures developed for unusual TCP/UDP port activity.
- Recommendations include network segmentation and firmware updates.
- Case studies show attackers bypassing traditional perimeter controls.
Description:
A SANS diary entry highlighted recent threat actor campaigns leveraging Internet‑connected KVM switches to gain low‑level access to internal networks. The analysis provides detection guidance based on anomalous port scans and traffic patterns associated with these devices.
Why It Matters:
IP‑KVMs represent a blind spot in many perimeter defenses. Enterprises should inventory such hardware, isolate them from critical segments, and apply strict access controls to diminish the attack surface.
9️⃣ OpenClaw AI agents automate reverse‑shell deployment
Key Points:
- OpenClaw framework enables AI‑driven malware generation.
- Demonstrated ability to craft context‑aware reverse shells.
- Uses semantic worm techniques to adapt to target environments.
- Highlights need for AI‑focused detection capabilities.
Description:
VirusTotal’s blog explored the second part of the OpenClaw series, showcasing how AI agents can automatically generate and deploy reverse shells, adjust payloads based on system topology, and evade conventional sandboxing. The research underscores a shift toward cognitive rootkits.
Why It Matters:
Traditional signature‑based defenses may struggle against AI‑generated threats. Security teams must invest in behavioral analytics and threat‑intel sharing to recognize patterns indicative of autonomous malware activity.
🔟 Open‑source display tool raises supply‑chain security questions
Key Points:
- Utility automates display switching on Linux systems.
- Relies on external scripts that could be tampered with.
- Potential for malicious code injection via compromised dependencies.
- Advises strict code review and signed releases.
Description:
The GitHub repository for "displayflowcli" provides a command‑line tool for managing multiple monitors. While useful for DevOps automation, the project’s reliance on third‑party scripts and minimal verification mechanisms raises concerns about supply‑chain integrity in CI/CD pipelines.
Why It Matters:
Adopting open‑source automation tools without rigorous vetting can introduce hidden backdoors. Organizations should enforce dependency scanning and enforce signed releases to mitigate the risk of compromised tooling.
Stay vigilant and prioritize remediation.

Member discussion