AI supply chain breaches erode trust. 🚀 Wiper malware resurfaces, targeting critical infrastructure.

Good morning, March 24, 2026 – here’s your executive briefing on the week’s top cyber and AI threats.
Today's headlines
- AI model supply chain backdoors discovered in LiteLLM packages.
- CanisterWorm wiper campaign targets Iranian critical infrastructure.
- FBI and CISA issue alerts on Signal and WhatsApp account hijacks.
- GreyNoise integration automates real‑time malicious IP blocking for Google SecOps.
- Student loan provider breach compromises 2.5 M personal records.
- New detection techniques uncover covert IP‑based KVM devices.
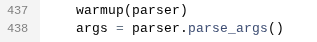
1️⃣ GreyNoise Boosts Google SecOps with Real‑Time Blocklists
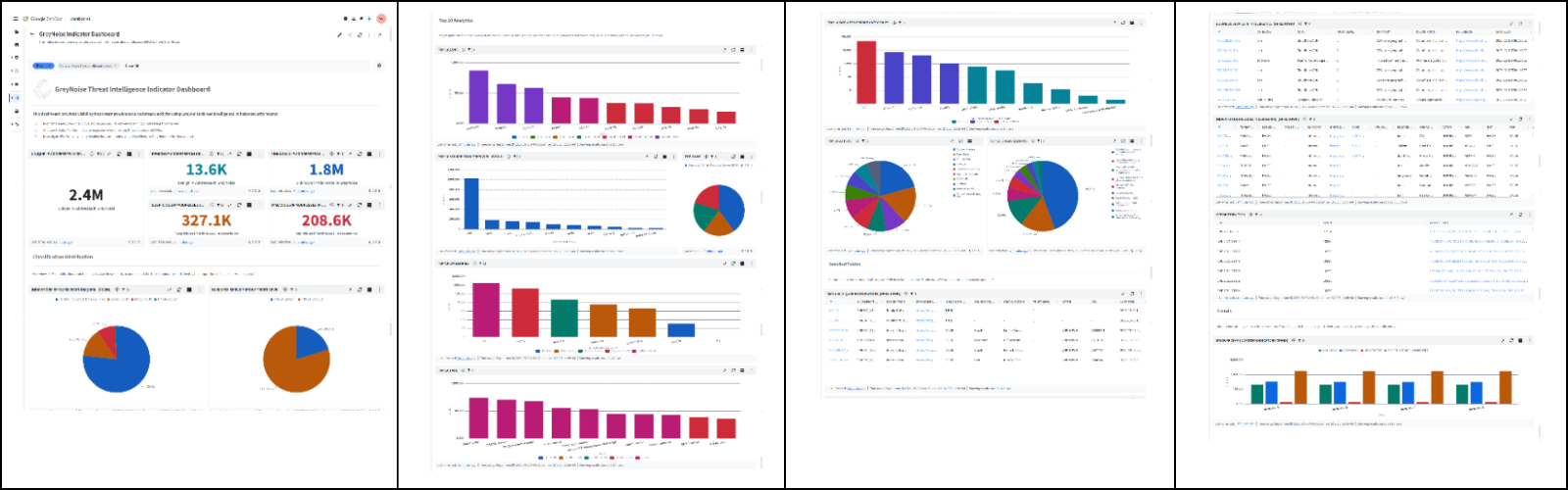
Key Points:
- Integration expands Google SecOps detection with GreyNoise data.
- Real‑time blocklists automatically block malicious IPs.
- Reduces alert fatigue by filtering noisy internet scans.
- Enhances threat‑hunting with enriched context.
- Improves overall SOC efficiency and response speed.
Description:
GreyNoise announced a new integration with Google SecOps that delivers fully configurable, real‑time blocklists directly into Google’s security operations workflow. The partnership enables security teams to automatically filter out low‑value traffic and focus on high‑risk indicators, streamlining incident investigation and threat‑hunting activities.
Why It Matters:
For CISOs, the ability to suppress mass‑scanner noise and prioritize genuine threats translates into faster detection and remediation, lowering exposure to active exploitation. The automation also reduces analyst workload, allowing resources to be reallocated to strategic initiatives and improving overall security posture.
2️⃣ TeamPCP Inserts Backdoors into LiteLLM via Compromised Trivy

Key Points:
- LiteLLM versions 1.82.7–1.82.8 contain hidden backdoor code.
- Backdoor introduced through a compromised Trivy CI/CD pipeline.
- Enables remote code execution and data exfiltration.
- Highlights supply‑chain vulnerabilities in AI model deployments.
- Prompted emergency patches and security‑tool updates.
Description:
Security researchers discovered that TeamPCP inserted malicious backdoors into recent releases of the open‑source LiteLLM library. The compromise originated from a tampered Trivy container image used in CI/CD pipelines, allowing threat actors to execute arbitrary code when the library is imported by AI applications.
Why It Matters:
The incident underscores the critical risk of third‑party dependencies in AI development environments. Organizations must enforce strict SBOM verification, signed artifacts, and continuous monitoring of build pipelines to prevent similar supply‑chain attacks that could compromise confidential data or model integrity.
3️⃣ LiteLLM Compromise Confirmed by The Register After Trivy Attack
Key Points:
- Independent analysis validates the LiteLLM backdoor presence.
- Threat actors leveraged the backdoor for credential theft.
- Emphasizes need for SBOMs and artifact signing.
- Provides actionable response steps for affected deployments.
- Raises awareness of AI model supply‑chain threats.
Description:
The Register published a follow‑up investigation confirming the backdoor in LiteLLM introduced via a compromised Trivy image. The report details how attackers exploited the hidden code to harvest API keys and perform lateral movement within victim environments, confirming the severity of the supply‑chain breach.
Why It Matters:
For security leaders, this reinforces the necessity of rigorous provenance checks for AI libraries. Failure to verify component integrity can lead to undetected footholds, making it essential to embed validation controls into CI/CD pipelines and maintain continuous monitoring of AI workloads.
4️⃣ CanisterWorm Unleashes Wiper Targeting Iranian Critical Systems
Key Points:
- New wiper variant, CanisterWorm, designed to destroy data.
- Utilizes multi‑stage infection chain with file‑encryption payload.
- Attributed to an Iran‑backed threat group.
- Targets healthcare, energy, and industrial control systems.
- Immediate patching and backups recommended.
Description:
Krebs on Security reported that the CanisterWorm wiper has been observed targeting infrastructure in Iran. The malware follows a sophisticated multi‑stage infection process, ultimately wiping files and rendering systems inoperable. Indicators of compromise have been shared with national CERTs.
Why It Matters:
Wiper attacks can cause irreversible operational disruption, especially in critical sectors. CISOs must prioritize timely patching, verify backup integrity, and enhance network segmentation to limit the spread of destructive payloads.
5️⃣ OWASP Announces Retirement of Its Meetup Platform
Key Points:
- OWASP will shut down its legacy Meetup community site.
- Members are encouraged to migrate to Discord and other channels.
- Potential temporary loss of in‑person networking opportunities.
- Signals a shift in how open‑source security communities collaborate.
- Provides migration resources and timeline.
Description:
The OWASP Foundation announced the retirement of its proprietary Meetup platform, directing its global community to transition to modern collaboration tools such as Discord, Slack, and virtual conference platforms. The move aims to consolidate community engagement and reduce maintenance overhead.
Why It Matters:
Security practitioners rely on OWASP events for knowledge sharing and collaborative research. A smooth migration is essential to maintain the flow of best‑practice guidance and to avoid fragmentation of the community, which could impact coordinated vulnerability response efforts.
6️⃣ FBI & CISA Warn of Russian Hijacking of Signal & WhatsApp

Key Points:
- Russian threat actors using SIM‑swap techniques to compromise accounts.
- Targeted journalists, activists, and government officials.
- Advisory recommends enabling multi‑factor authentication and app‑based verification.
- Highlights vulnerability of encrypted messaging platforms to social engineering.
- Joint agency effort improves rapid dissemination of mitigation steps.
Description:
The FBI and CISA issued a joint advisory warning that Russian cyber‑espionage groups are hijacking Signal and WhatsApp accounts through sophisticated SIM‑swap attacks. The agencies provide detailed indicators of compromise and mitigation recommendations.
Why It Matters:
Compromised encrypted communications undermine confidentiality for high‑value targets. Organizations must enforce strict identity verification, educate users about SIM‑swap threats, and monitor for anomalous login activity to preserve secure channels.
7️⃣ Student Loan Data Breach Exposes 2.5 Million Records

Key Points:
- Leak stemmed from misconfigured cloud storage bucket.
- Personal, financial, and loan data of 2.5 M individuals exposed.
- Regulators may impose fines for inadequate data protection.
- Recommendations include encryption at rest and stricter access controls.
- Affected individuals should monitor credit reports for fraud.
Description:
ThreatPost reported a breach affecting a major student loan servicer, where a publicly accessible cloud bucket exposed the personal and financial details of approximately 2.5 million borrowers. The data included Social Security numbers, loan balances, and contact information.
Why It Matters:
Breaches of this scale can lead to identity theft and significant compliance penalties under data‑privacy regulations. Enterprises must enforce robust cloud configuration management, conduct regular audits, and ensure encryption to protect sensitive consumer data.
8️⃣ SANS Diary Details Methods to Detect IP‑Based KVM Appliances

Key Points:
- IP‑KVM devices can be leveraged for covert remote access.
- Detection relies on anomalous TCP/UDP port activity and traffic patterns.
- Provides scripts and rule‑sets for IDS/IPS integration.
- Recommends network segmentation and strict access controls for management interfaces.
- Raises awareness of physical‑to‑network attack vectors.
Description:
The SANS Internet Storm Center diary entry outlines techniques for identifying IP‑based KVM (Keyboard‑Video‑Mouse) switches that may be used by threat actors to gain stealthy remote access. The author shares detection signatures and best‑practice hardening steps.
Why It Matters:
KVM compromises blur the line between physical and network security, presenting a hidden attack surface. Implementing the recommended detection rules and segmentation helps prevent unauthorized control of critical infrastructure.
9️⃣ VirusTotal Explores Reverse Shells, Semantic Worms, Cognitive Rootkits
Key Points:
- Research shows AI‑generated malware can craft adaptive reverse shells.
- Semantic worms use language models to evade signature detection.
- Cognitive rootkits adjust behavior based on environment analysis.
- Emphasizes need for behavioral analytics and sandboxing.
- Calls for industry collaboration on AI‑driven threat intelligence.
Description:
VirusTotal’s research blog published a deep dive into advanced AI‑assisted malware techniques, including reverse shells hidden within natural‑language code, semantic worms that rewrite themselves, and cognitive rootkits that learn from their host environment.
Why It Matters:
The emergence of AI‑enhanced malware raises the bar for detection. Security teams must invest in behavioral monitoring, AI‑aware threat hunting, and collaborative intel sharing to counter these dynamic threats.
🔟 GitHub Project ‘Atomic Display Switching’ Highlights Supply‑Chain Leak Risks
Key Points:
- Open‑source tool enables rapid display output switching for debugging.
- If compromised, can capture screen contents and exfiltrate data.
- Demonstrates supply‑chain risk of unvetted third‑party code.
- Recommends code signing, dependency scanning, and runtime integrity checks.
- Advocates for strict governance of dev‑tool ecosystems.
Description:
A GitHub repository providing an atomic display‑flow CLI tool was flagged for potential misuse after security analysis revealed that a malicious fork could silently capture and transmit screen data. The project highlights how even benign utilities can become attack vectors when supply‑chain integrity is weak.
Why It Matters:
Enterprises must extend their software‑bill‑of‑materials (SBOM) practices to include developer utilities and CLI tools. Enforcing signed releases and continuous dependency scanning reduces the risk of covert data leakage through compromised open‑source projects.
Stay vigilant and prioritize strategic controls.

Member discussion