OpenClay Part II Unveils AI‑Driven Reverse Shells and Adaptive Worms
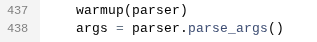
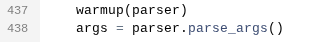
The latest OpenClaw analysis reveals that threat actors are now embedding reverse shells inside AI‑generated scripts, making the payloads appear as legitimate code snippets. These scripts are delivered via compromised supply‑chain packages and execute on target hosts without raising static‑analysis alarms. In parallel, the group has deployed “semantic worms” that mutate their code semantics on each iteration, evading signature‑based detection, while “cognitive rootkits” monitor system responses and adjust their behavior to remain stealthy.
For defenders, the takeaway is urgent: traditional signature and heuristic tools will miss these dynamically generated and self‑adapting components. Organizations must adopt behavior‑based monitoring, enforce strict code‑review pipelines for third‑party contributions, and deploy sandboxing that can detect anomalous outbound connections. Early detection of AI‑crafted reverse shells and adaptive malware is critical to prevent lateral movement and long‑term persistence.
Categories: Malware & Ransomware, AI Security & Threats, Threat Intelligence, #AI Security & Threats
Source: Read original article


Member discussion