AI‑driven vulnerabilities expand attack surface 🚀. Zero‑day exploits pressure resilience 🛡️.
Good morning, March 8, 2026 – here are today’s top cyber and AI threat updates.
Today's headlines
- AI‑driven tools expose high‑severity code flaws and browser bugs.
- Zero‑day exploits bypass traditional perimeters, urging zero‑trust adoption.
- Threat actors leverage AI agents for automated infrastructure management.
- IoT camera targeting in conflict zones merges cyber and kinetic threats.
- New deception campaigns use fake updates and watering‑hole sites to steal credentials.
1️⃣ GreyNoise intelligence now embedded in CrowdStrike Falcon platform
Key Points:
- Real‑time blocklists stop malicious IPs at the edge.
- Early warning on emerging CVE exploitation spikes.
- Filters mass internet scans to reduce SOC noise.
- Adds context to incidents for faster investigation.
Description:
GreyNoise has integrated its intelligence into the CrowdStrike Falcon platform, delivering configurable, real‑time blocklists and early warning capabilities that help organizations block malicious traffic before it reaches critical assets while streamlining incident response.
Why It Matters:
For CISOs, this integration reduces alert fatigue, shortens detection cycles, and enhances protection against fast‑moving threats, directly supporting resilience and risk reduction strategies.
2️⃣ OpenAI Codex Security scans 1.2M code commits, reveals 10,561 high‑severity flaws

Key Points:
- AI agent identifies complex vulnerabilities missed by traditional scanners.
- Provides validated fix suggestions within ChatGPT interfaces.
- Available as a research preview for paid ChatGPT plans.
- Free usage for the first month encourages early adoption.
- Highlights AI’s expanding role in software supply‑chain security.
Description:
OpenAI launched Codex Security, an AI‑powered agent that analyzes 1.2 million code commits, detecting over ten thousand high‑severity issues and offering actionable remediation directly through ChatGPT, now accessible to Pro, Enterprise, Business and Education customers.
Why It Matters:
Enterprises can leverage this tool to automate vulnerable code detection, accelerate patching cycles, and lower the risk of supply‑chain breaches, aligning with proactive security postures.
3️⃣ GoAnywhere MFT zero‑day exploited by Storm‑1175 underscores perimeter limits

Key Points:
- CVE‑2025‑10035 is a critical deserialization bug (CVSS 10.0).
- Attack bypassed traditional firewall defenses.
- CISA warns such shared‑service flaws remain hidden long.
- Incident caused significant data exposure on Sept 11 2025.
- Calls for internal micro‑segmentation and zero‑trust controls.
Description:
A critical zero‑day in GoAnywhere Managed File Transfer (CVE‑2025‑10035) was weaponized by the Storm‑1175 actor group, exploiting a deserialization flaw to bypass perimeter defenses and compromise sensitive data during a September 2025 attack.
Why It Matters:
The breach illustrates that perimeter‑only security is insufficient; organizations must adopt zero‑trust architectures, micro‑segmentation, and continuous monitoring to contain such high‑impact vulnerabilities.
4️⃣ Anthropic’s Claude Opus discovers 22 new Firefox bugs, 14 high severity

Key Points:
- 22 vulnerabilities found over a two‑week period in Jan 2026.
- 14 classified high, seven moderate, one low severity.
- Prompted release of Firefox 148 to address issues.
- Demonstrates AI’s speed in vulnerability research.
- Emphasizes need for rapid browser hardening.
Description:
Using the Claude Opus 4.6 model, Anthropic uncovered 22 new security flaws in Mozilla’s Firefox browser, including 14 high‑severity bugs, leading to a rapid patch rollout in Firefox 148.
Why It Matters:
The findings confirm AI can accelerate vulnerability discovery, urging vendors and enterprises to adopt continuous patching processes to maintain browser security and protect end‑user data.
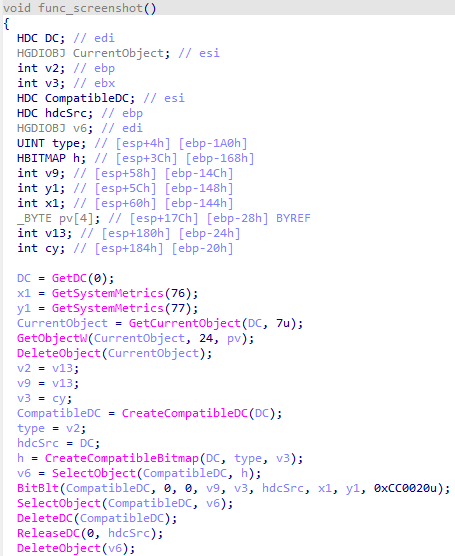
5️⃣ LummaStealer resurfaces, paired with CastleLoader, evades detection through legit‑like behavior
Key Points:
- Malware mimics legitimate user actions to avoid alerts.
- Shares IoCs on GitHub for community remediation.
- Integrates with CastleLoader for multi‑stage infection.
- Targets Windows via phishing and malicious macros.
- Highlights importance of behavioral analytics in defenses.
Description:
The LummaStealer infostealer has re‑emerged alongside the CastleLoader dropper, employing techniques that imitate normal user behavior, complicating detection and broadening its impact across Windows environments.
Why It Matters:
Defenders must enhance behavioral monitoring and threat‑intel sharing to spot such stealthy malware, reducing the risk of credential theft and data exfiltration.
6️⃣ AI agents accelerate attacker infrastructure, evidence of North Korean use

Key Points:
- Large language models automate reconnaissance and credential stuffing.
- Facilitate rapid deployment of ransomware and phishing kits.
- North Korean actors leverage AI for drudge tasks.
- Increases attribution difficulty and scale of attacks.
- Necessitates AI‑aware defensive strategies.
Description:
Recent intelligence shows state‑aligned threat groups, including North Korea, are employing AI agents to streamline the deployment and management of attack infrastructure, automating low‑level tasks that previously required manual effort.
Why It Matters:
The adoption of AI by adversaries expands their operational tempo, demanding that defenders integrate AI detection and response capabilities to keep pace with automated threats.
7️⃣ Falcon Next‑Gen SIEM streamlines onboarding with sensor‑native log collection
Key Points:
- Eliminates manual agent deployment for log ingestion.
- Provides unified visibility across endpoints, cloud, and network.
- Accelerates SOC scaling and reduces deployment time.
- Integrates with Falcon Fusion for automated response.
- Supports compliance reporting with built‑in normalization.
Description:
CrowdStrike’s Falcon Next‑Gen SIEM introduces sensor‑native log collection, allowing organizations to ingest data directly from existing sensors without extra agents, thereby simplifying onboarding and enhancing real‑time analytics.
Why It Matters:
This capability reduces operational overhead, shortens time‑to‑detect, and helps CISOs meet compliance timelines while improving overall security posture.
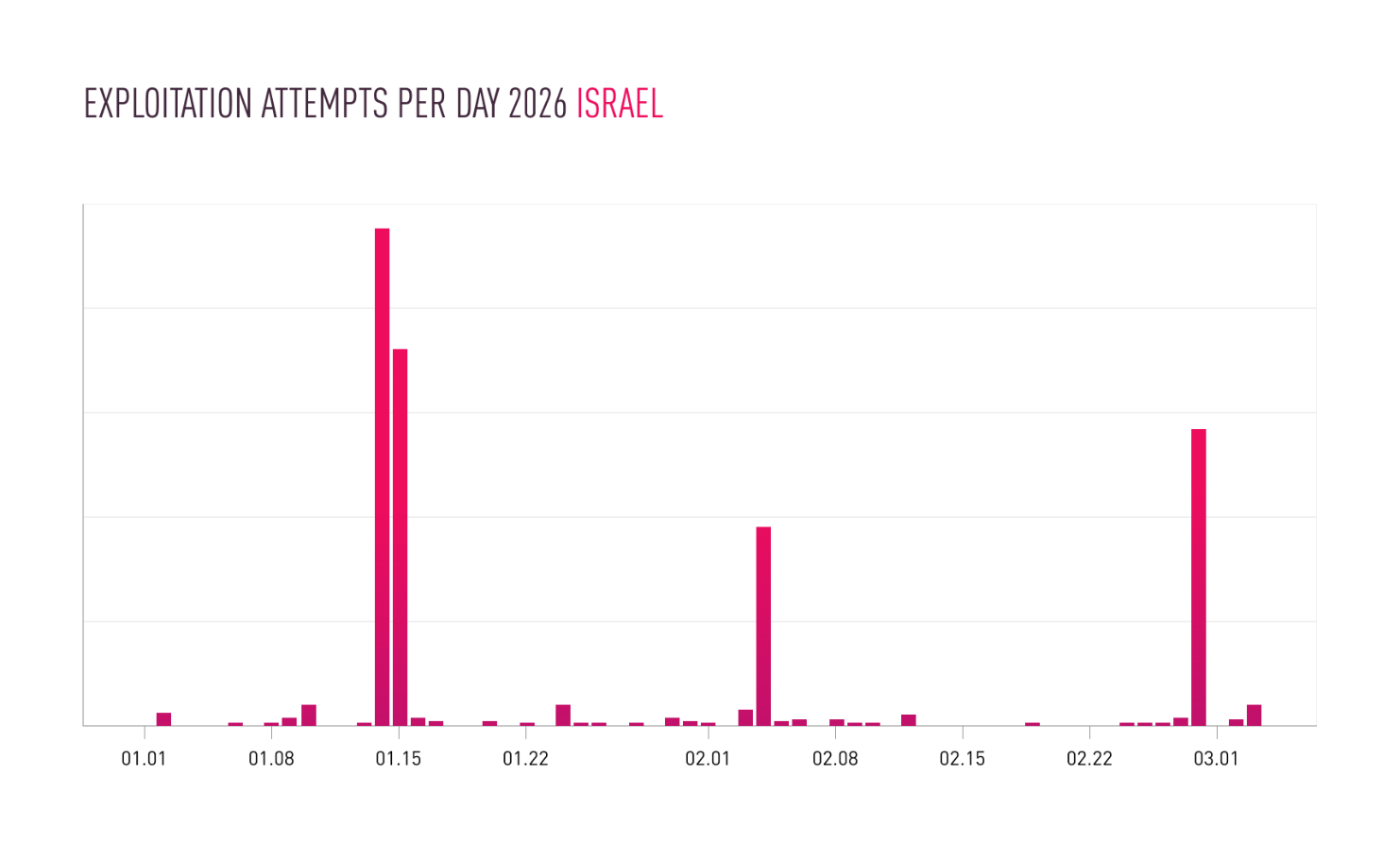
8️⃣ Iranian campaigns intensify IP‑camera attacks, blend cyber and kinetic tactics
Key Points:
- Threats focus on surveillance devices in conflict zones.
- Exploit default credentials and outdated firmware.
- Provide real‑time visual intel for physical operations.
- Show convergence of cyber and kinetic warfare.
- Advise hardening IoT devices and network segmentation.
Description:
Checkpoint research reveals that Iranian actors are escalating attacks on IP cameras across the Middle East, leveraging compromised video feeds to support kinetic operations and gather battlefield intelligence.
Why It Matters:
Enterprises operating in or near conflict zones must treat IoT assets as critical infrastructure, applying strict hardening, credential rotation, and network isolation to prevent adversary exploitation.
9️⃣ APT TA423 uses watering‑hole lures to deploy ScanBox keylogger

Key Points:
- ScanBox JavaScript tool harvests keystrokes from victims.
- Targets Australian news sites to reach domestic and energy firms.
- Part of broader ‘0ktapus’ threat‑group campaign.
- Demonstrates resurgence of watering‑hole technique in 2026.
- Recommends strict web filtering and threat‑intel feeds.
Description:
A new watering‑hole campaign attributed to APT group TA423 is delivering the ScanBox JavaScript keylogger to visitors of compromised Australian news websites, aiming at energy and government sectors in the South China Sea region.
Why It Matters:
The resurgence of watering‑hole attacks underscores the need for continuous web traffic monitoring, threat‑intel integration, and user awareness to prevent credential theft and lateral movement.
🔟 Malicious fake Google Meet update grants attackers full PC control
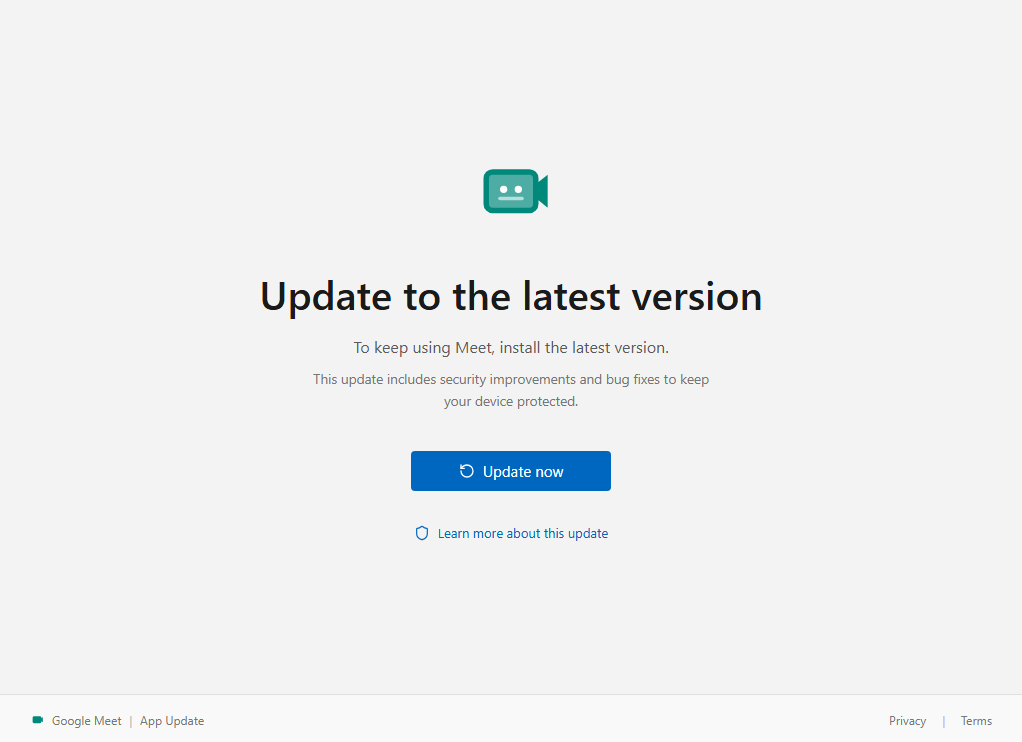
Key Points:
- Social‑engineering lure mimics legitimate update prompt.
- Executes a remote‑access trojan upon click.
- Targets Windows users via Microsoft Store download.
- Early detection possible through heuristic monitoring.
- Emphasizes user education and strict patch management.
Description:
A new phishing campaign distributes a counterfeit Google Meet update dialog that, when clicked, installs a remote‑access trojan capable of fully controlling the victim’s PC, exploiting the trust placed in legitimate software updates.
Why It Matters:
Organizations must reinforce user training on update authenticity, deploy application control solutions, and monitor for anomalous installer behavior to thwart such high‑impact supply‑chain attacks.
Evolve your defenses—stay ahead of AI‑enhanced threats.
Member discussion