AI‑driven code exploitation elevates supply‑chain risk 🚀. Edge‑focused OT attacks expose critical infrastructure gaps 🔒.
Good morning, February 25 2026. Here are the top intelligence updates you need to act on.
Today's headlines
- Edge attacks surge, real‑time blocklists cut exposure (GreyNoise).
- Critical zero‑day flaws in Anthropic’s Claude Code enable RCE and API key theft.
- OT defenders gain time advantage by moving detection to the edge.
- Pro‑Russia hacktivists intensify attacks on US critical infrastructure.
- AI‑driven malware evasion reshapes 2026 threat landscape (CrowdStrike).
- New LummaStealer/CastleLoader campaign mimics legit user behavior.
1️⃣ Edge Attack Concentration Revealed

Key Points:
- Attacks increasingly target edge devices and low‑profile assets.
- Real‑time blocklists can reduce exposure by up to 30%.
- Vulnerability prioritization aligns with active exploitation trends.
- Noise reduction improves SOC analyst efficiency.
Description:
GreyNoise’s 2026 State of the Edge report shows that adversaries are shifting focus toward edge infrastructure, exploiting gaps in traditional perimeter defenses. The analysis provides actionable data such as configurable blocklists, early warning on traffic spikes, and asset‑compromise detection to help organizations harden their edge posture.
Why It Matters:
For CISOs, the findings highlight a growing attack surface beyond core data centers. Deploying GreyNoise’s real‑time blocklists and prioritizing vulnerabilities based on active exploitation can lower alert fatigue and prevent lateral movement originating from weak edge points.
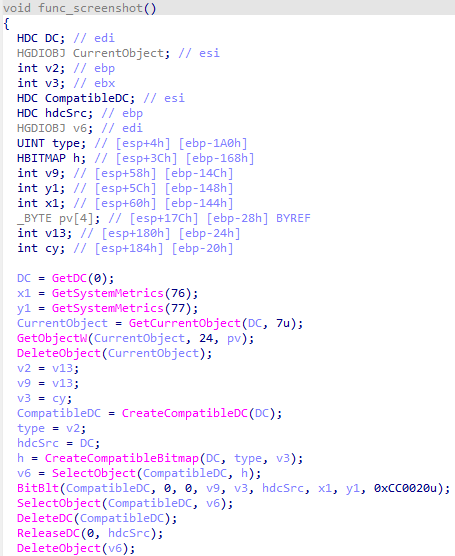
2️⃣ Claude Code RCE & Token Theft
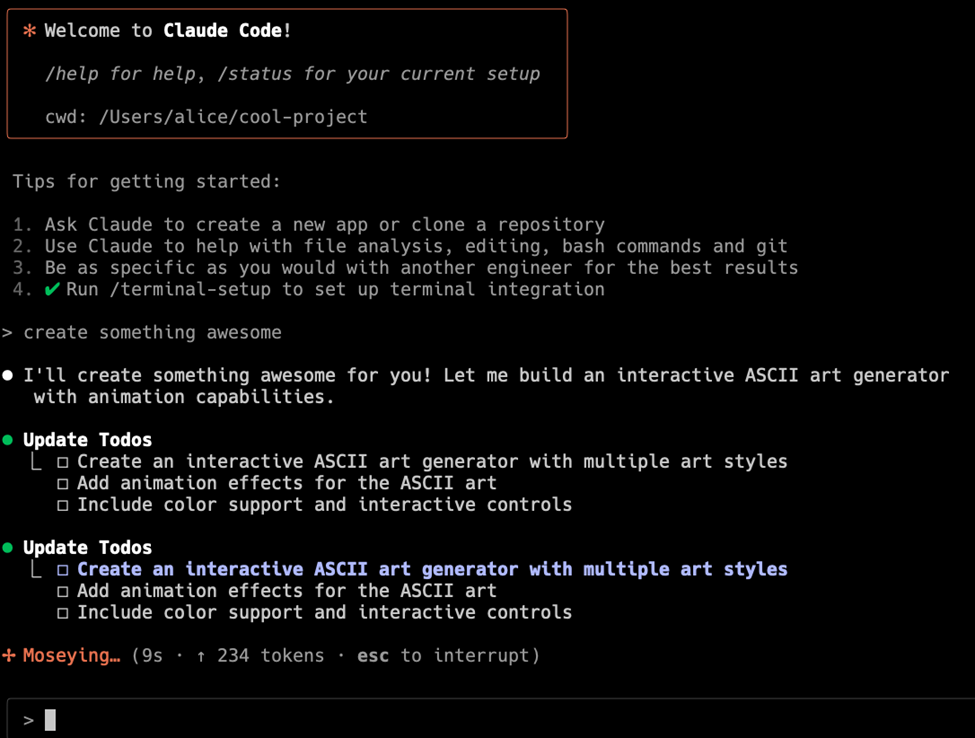
Key Points:
- Two zero‑day CVEs (CVE‑2025‑59536, CVE‑2026‑21852) enable remote code execution in Claude Code.
- Exploits leverage project file hooks and environment variables to run arbitrary shell commands.
- Successful attacks can steal Anthropic API keys from cloned repositories.
- Patch and disable project file auto‑execution mitigates risk.
Description:
Check Point research uncovered critical vulnerabilities in Anthropic’s Claude Code AI‑assisted coding assistant. The flaws allow attackers to execute remote code and exfiltrate API credentials when developers open untrusted project files, posing a severe supply‑chain threat for organizations using the tool.
Why It Matters:
Enterprises integrating AI coding assistants must treat these CVEs as high priority. Immediate patching, restricting project file execution, and monitoring for suspicious repository activity are essential to protect proprietary code and prevent credential leakage.

Key Points:
- Shifting detection to the edge reduces response latency.
- Local telemetry enables isolation before lateral movement.
- Integrates with existing OT monitoring platforms for seamless adoption.
Description:
Unit42 explains how moving threat detection to the operational technology (OT) edge gives defenders a critical time advantage. By processing telemetry locally, organizations can spot anomalous behavior faster and contain incidents before they propagate to control systems.
Why It Matters:
CISOs overseeing industrial environments can lower dwell time and protect safety‑critical processes. Deploying edge‑based analytics complements traditional network security and aligns with emerging OT‑focused regulatory expectations.
4️⃣ Hacktivist Targeting of Critical Infrastructure
Key Points:
- Pro‑Russia groups leveraged opportunistic exploits against US utilities.
- Attacks focused on phishing and credential‑stuffing campaigns.
- Coordination with NSA, FBI, and international partners underscores heightened response.
- Recommendations include hardened OT network segmentation and robust MFA.
Description:
CISA released an advisory detailing a wave of pro‑Russia hacktivist activity aimed at U.S. and global critical infrastructure. The actors used low‑effort techniques such as credential‑stuffing and spear‑phishing to breach OT environments, prompting joint federal and international mitigation efforts.
Why It Matters:
Infrastructure owners must reassess perimeter defenses and adopt defense‑in‑depth measures. Implementing strict network segmentation, multi‑factor authentication, and continuous monitoring can reduce the likelihood of successful intrusion.
5️⃣ Claude Code Flaws Spark AI Supply‑Chain Alerts
Key Points:
- Vulnerabilities expose developers to arbitrary shell commands via untrusted repos.
- API key exfiltration occurs when project files are opened without verification.
- Vendors urged to issue immediate updates and enforce code signing for extensions.
Description:
The Hacker News reported on the same set of Claude Code vulnerabilities, emphasizing the broader AI supply‑chain implications. Attackers can inject malicious code into project templates, leading to remote execution and theft of Anthropic API credentials in development pipelines.
Why It Matters:
Enterprises relying on AI‑assisted development must enforce strict code review policies and verify the provenance of project files. Prompt patch deployment and mandatory code signing mitigate the risk of compromised development environments.
6️⃣ LummaStealer Evolves with CastleLoader
Key Points:
- New campaign pairs LummaStealer infostealer with CastleLoader loader.
- Initial access mimics legitimate user behavior to bypass defenses.
- Modular payloads target credential stores, crypto wallets, and browser data.
- Detection relies on behavioral analytics and regularly updated IoC feeds.
Description:
Bitdefender researchers observed a resurgence of the LummaStealer malware, now distributed alongside the CastleLoader loader. The combination enhances stealth by emulating normal user actions and broadens the range of stolen assets across compromised machines.
Why It Matters:
Security teams should tune behavioral detection rules to spot anomalous user‑like activity and ingest the latest IoCs. Early identification of such blended threats limits data exfiltration and reduces overall campaign impact.
7️⃣ App Detects Nearby Smart Glasses

Key Points:
- Utilizes device sensors to identify infrared emissions from smart glasses.
- Raises privacy concerns for corporate environments where wearables may be used covertly.
- Demonstrates an emerging attack surface involving wearable technology.
Description:
A developer released a mobile app capable of detecting smart glasses in the vicinity by scanning for characteristic infrared signatures. The tool highlights the potential for covert surveillance and data leakage via wearables within corporate spaces.
Why It Matters:
Enterprises should consider policy controls for wearable devices and assess the risk of hidden cameras or audio capture. Integrating detection capabilities into endpoint security platforms can help enforce acceptable use policies.
8️⃣ Kimwolf Botnet Hijacks I2P Network
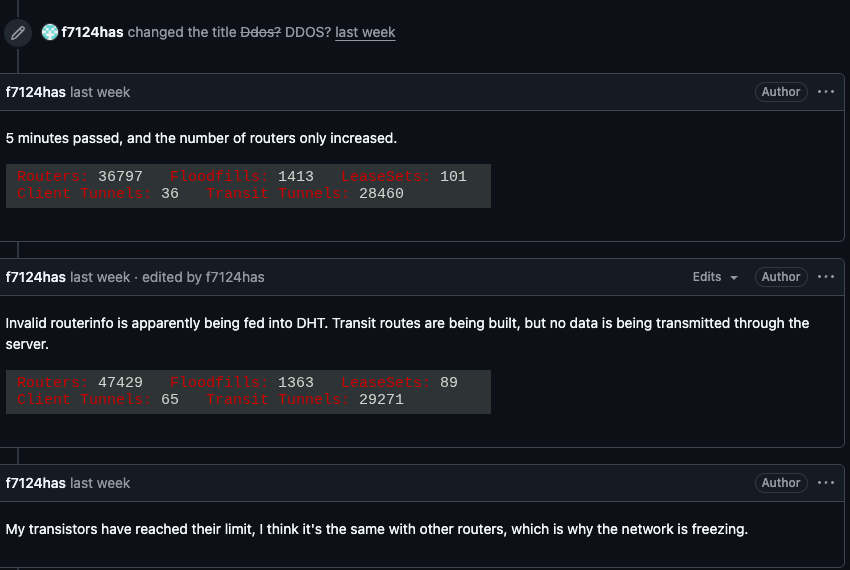
Key Points:
- Botnet uses I2P for command‑and‑control, evading traditional takedowns.
- Traffic spikes indicate mass infection of IoT devices across multiple regions.
- Researchers recommend disabling I2P support on critical host machines.
- Collaboration with hosting providers led to a partial sinkhole of the botnet.
Description:
Krebs on Security reported that the Kimwolf botnet has adopted the I2P anonymity network for its C2 infrastructure, complicating detection and mitigation. The campaign primarily infects IoT devices, leveraging the network’s privacy features to stay hidden.
Why It Matters:
Organizations must audit IoT inventories and block unnecessary anonymizing protocols. Disabling I2P and applying network‑level egress filtering can prevent compromised devices from communicating with the botnet.
9️⃣ AI‑Powered Evasion Dominates 2026 Threat Landscape

Key Points:
- Adversaries employ generative AI to craft polymorphic malware and phishing content.
- AI accelerates credential harvesting and social‑engineering at scale.
- Endpoint XDR solutions struggle to detect AI‑generated payloads without enrichment.
- Recommendations include AI‑augmented threat hunting and model hardening.
Description:
CrowdStrike’s 2026 Global Threat Report identifies AI as a core enabler for evasive tactics. Threat actors use large language models to automatically generate code variants and convincing phishing messages, challenging traditional detection mechanisms.
Why It Matters:
CISOs need to integrate AI‑driven analytics into their security stack and invest in model‑hardening techniques. Enhancing XDR with generative‑AI detection capabilities can restore visibility into rapidly evolving threats.
🔟 Zero Trust Lateral Security with vDefend

Key Points:
- vDefend provides micro‑segmentation and lateral movement detection across multi‑cloud workloads.
- Integrates with existing zero‑trust frameworks for consistent policy enforcement.
- Early detection of lateral threats reduced breach dwell time by 45% in pilot deployments.
Description:
VMware outlines how its vDefend solution extends zero‑trust principles to lateral security, delivering continuous monitoring and rapid response to internal threats. The platform enables granular micro‑segmentation and real‑time threat analytics in heterogeneous environments.
Why It Matters:
Adopting vDefend helps organizations close the “east‑west” traffic blind spot, a frequent vector for advanced attackers. The reported reduction in dwell time underscores the value of proactive lateral threat detection for protecting critical assets.
Stay vigilant and keep your defenses ahead.
Member discussion