AI‑driven attacks and credential leaks spike risk 🚨. Integrated threat intel restores control 🤝
Good morning, March 12 2026. Here’s today’s top cyber and AI threat updates.
Today's headlines
- GreyNoise now integrates with Google SecOps and CrowdStrike Falcon.
- Microsoft Authenticator bug could expose one‑time passwords.
- OpenClaw AI skills are being weaponized for automated malware delivery.
- New Android vulnerability can bypass lock screens in seconds.
- Google Groundsource uses Gemini to turn news into actionable hazard data.
1️⃣ GreyNoise integrates with Google SecOps to sharpen threat detection
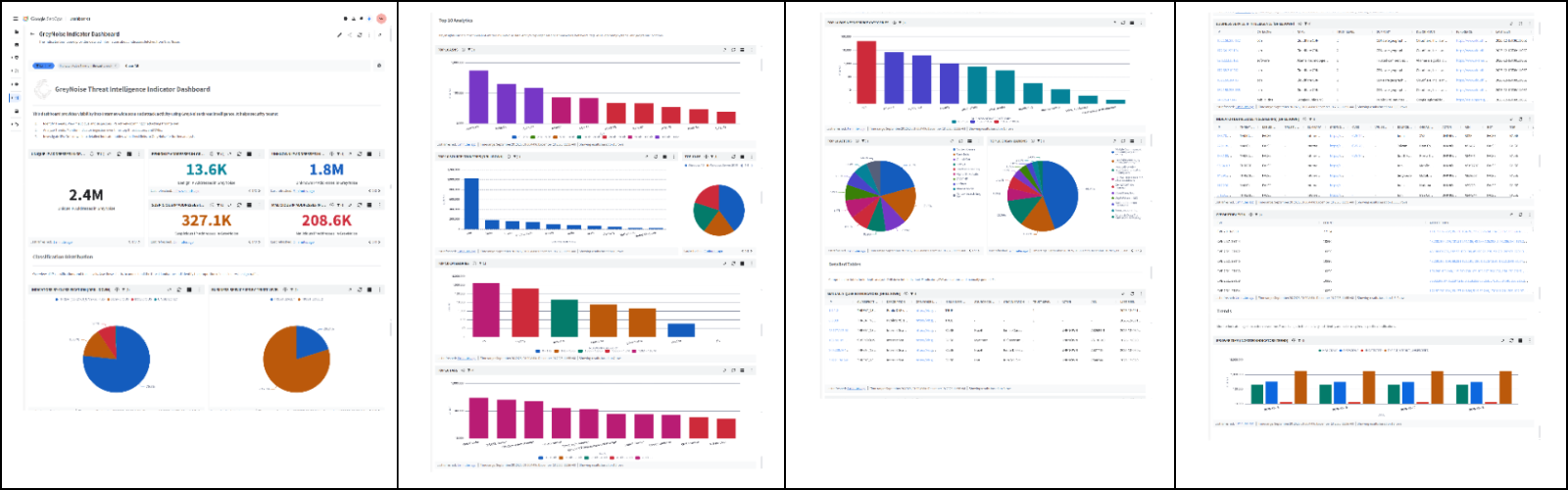
Key Points:
- Real‑time blocklists automatically block malicious IPs.
- Reduces false‑positive alerts from internet scanners.
- Enriches incident investigations with context on threat actors.
- Improves SOC efficiency and response times.
Description:
GreyNoise announced a native integration with Google Cloud SecOps, delivering configurable blocklists and contextual threat data directly into Google’s security tooling, enabling faster identification of malicious traffic and streamlined triage.
Why It Matters:
For CISOs, the integration means tighter perimeter control without increasing alert fatigue, allowing security teams to focus on high‑impact incidents and improve overall resilience against mass‑scan attacks.
2️⃣ GreyNoise intelligence now native in CrowdStrike Falcon platform
Key Points:
- Unified threat intel accessible within Falcon console.
- Accelerates threat hunting and malware attribution.
- Filters out noisy background traffic.
- Supports vulnerability prioritization with exploitation trends.
Description:
The partnership extends GreyNoise’s IP reputation data into CrowdStrike Falcon, allowing analysts to see real‑time malicious activity signals alongside endpoint detections, improving correlation and reducing investigation time.
Why It Matters:
Embedding this intel directly into a leading EDR platform gives security leaders a consolidated view of external threats, enhancing decision‑making for patching and threat mitigation.
3️⃣ IoT devices granting admin access expose critical infrastructure

Key Points:
- Default or weak credentials common on IoT admin accounts.
- Lack of multi‑factor authentication amplifies risk.
- Device fingerprinting and continuous monitoring recommended.
- Business Impact Analyses essential for IoT risk assessment.
Description:
A recent SANS diary entry highlights cases where IoT devices automatically log in with administrative privileges, allowing attackers to move laterally across networks if not properly segmented and hardened.
Why It Matters:
Enterprise leaders must enforce strong credential policies and real‑time monitoring for IoT assets to prevent unauthorized control that could disrupt operational technology environments.
4️⃣ Microsoft Authenticator bug may expose one‑time passwords

Key Points:
- App caches OTP codes in plaintext.
- Potential for code extraction on compromised devices.
- Immediate update required to fix leakage.
- Impact spans personal and corporate MFA deployments.
Description:
Security researchers discovered that certain versions of Microsoft Authenticator improperly store generated login codes, creating a window for attackers to capture MFA tokens before they expire.
Why It Matters:
Since MFA is a cornerstone of modern security, any weakness can undermine authentication guarantees; rapid patching is critical to preserve account integrity across organizations.
5️⃣ Android lock screen bypass tool cracks devices in under a minute

Key Points:
- Exploits a flaw in lock‑screen verification routine.
- Affects Android 12 and newer versions.
- Allows unauthorized access without PIN or biometric.
- Enterprise MDM solutions must enforce immediate updates.
Description:
A newly disclosed Android vulnerability enables attackers to bypass lock screen protections within 60 seconds by exploiting a timing discrepancy in the authentication module, compromising device confidentiality.
Why It Matters:
Mobile devices often contain corporate data; the rapid bypass heightens the risk of data leakage, prompting IT leaders to accelerate patch deployment and enforce stricter device policies.
6️⃣ OpenClaw AI agents weaponized to deliver malware via fake skills
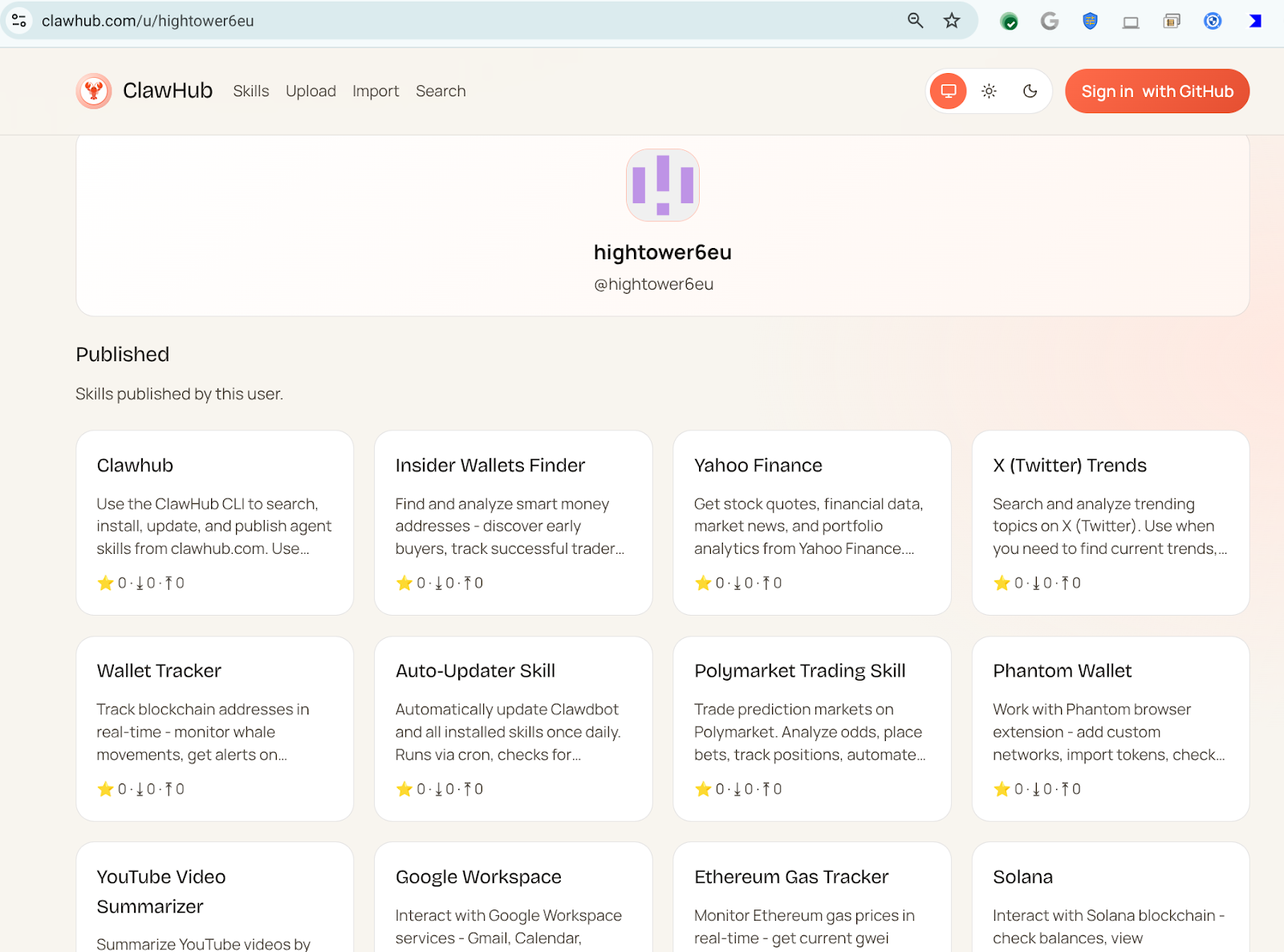
Key Points:
- Malicious actors publish seemingly benign AI skills.
- Skills automate download and execution of external code.
- Over 300 malicious skills linked to a single user.
- Obfuscation leverages legitimate AI workflow appearances.
Description:
VirusTotal’s analysis reveals that OpenClaw AI agents are being repurposed as a distribution platform for malware, with threat actors publishing malicious ‘skills’ that instruct victims to fetch and run code from untrusted sources.
Why It Matters:
The abuse of AI‑driven automation expands the attack surface, allowing rapid, scalable malware deployment that can evade traditional detection, underscoring the need for AI‑aware security controls.
7️⃣ Advanced OpenClaw skills deploy reverse shells and cognitive rootkits
Key Points:
- Introduces reverse‑shell capabilities within AI skills.
- Semantic worms propagate across AI‑enabled environments.
- Cognitive rootkits modify agent behavior stealthily.
- JA4 fingerprinting aids detection of malicious traffic.
Description:
The follow‑up blog post details how threat actors have evolved OpenClaw skills to include reverse shells, semantic worms, and AI‑crafted rootkits, enabling persistent, low‑profile compromises across distributed AI ecosystems.
Why It Matters:
These techniques demonstrate a new class of AI‑centric threats that can infiltrate and manipulate automated systems, requiring security teams to monitor AI workloads and adopt behavior‑based defenses.
8️⃣ Study reveals generalization tactics in autonomous cyber‑attack agents

Key Points:
- Autonomous agents learn transferable attack patterns.
- Demonstrates risk of self‑evolving threat capabilities.
- Highlights gaps in current defensive modeling.
- Calls for robust AI governance frameworks.
Description:
Researchers published a paper examining how autonomous cyber‑attack agents generalize learned exploits across environments, showing that these agents can adapt and conduct novel attacks without direct human input.
Why It Matters:
Understanding these mechanisms is vital for policymakers and security architects to develop countermeasures that anticipate AI‑driven threat evolution and enforce responsible AI usage.
9️⃣ ISC Stormcast highlights surge in SSH scanning activity

Key Points:
- Significant increase in global SSH/Telnet scans.
- Top scanning sources originate from Eastern Europe.
- Pre‑attack reconnaissance often precedes ransomware.
- Recommendation: enforce strong SSH keys and rate limiting.
Description:
The Internet Storm Center’s daily report notes a marked rise in SSH scanning traffic, suggesting heightened reconnaissance activity that may foreshadow credential‑stealing or ransomware campaigns.
Why It Matters:
CISOs should prioritize hardening SSH access and monitoring for anomalous connection attempts to block early-stage intrusion efforts.
🔟 Groundsource leverages Gemini to transform news into actionable data
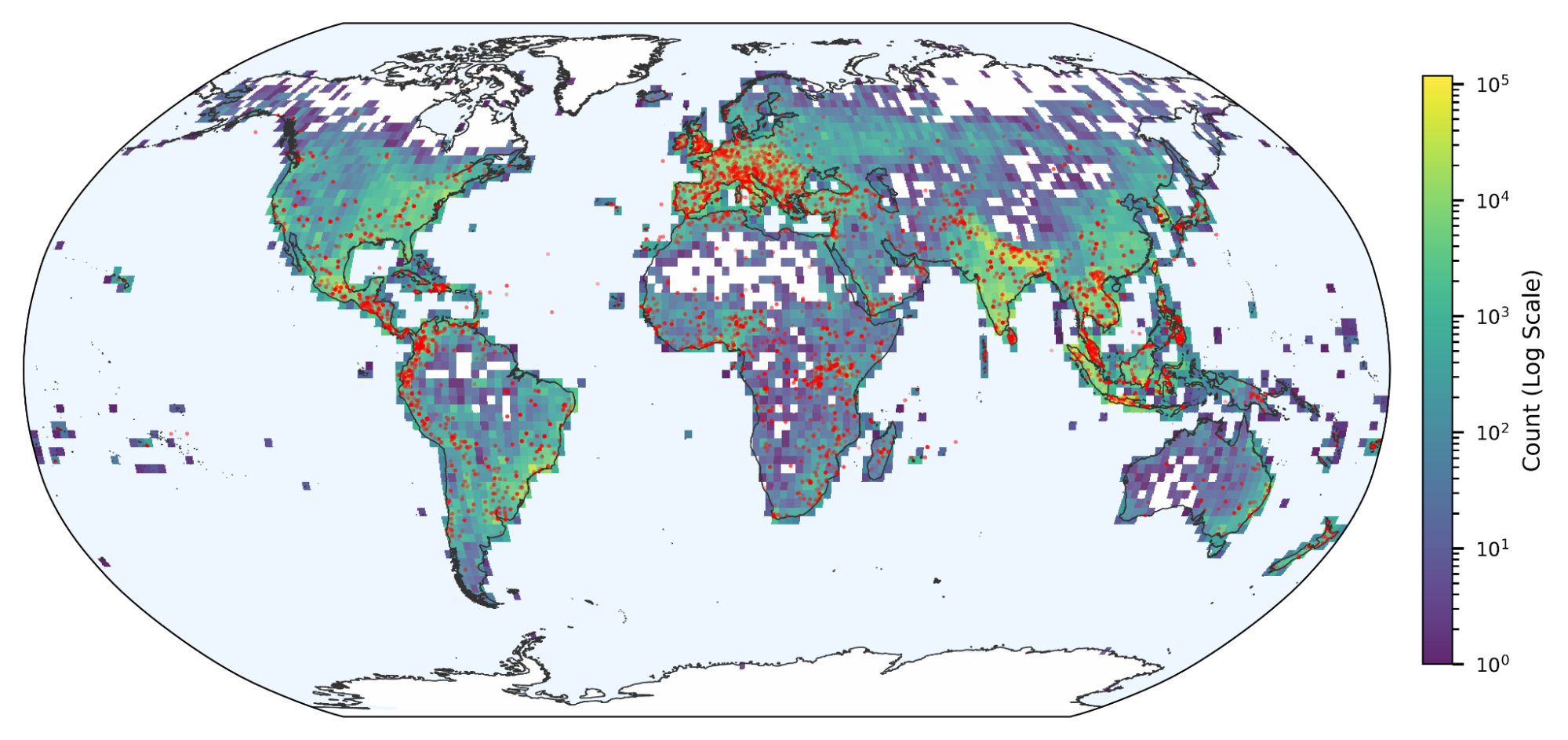
Key Points:
- AI extracts geospatial and temporal details from news articles.
- Creates structured datasets for natural disaster prediction.
- Expands to additional hazard types and rural coverage.
- Supports early warning systems for emergency responders.
Description:
Google Research unveiled Groundsource, a Gemini‑powered service that parses news reports into machine‑readable data, enabling rapid synthesis of hazard information for disaster response and risk analysis.
Why It Matters:
The ability to convert unstructured news into real‑time intelligence enhances situational awareness for organizations managing physical and cyber resilience, informing proactive risk mitigation.
Stay vigilant and keep your defenses ahead.
Member discussion